Admin Password Tool: A Practical How-To for Reset & Recovery
Learn how to choose, deploy, and securely use an admin password tool to reset and manage admin credentials across devices. This 2026 guide from Default Password covers step-by-step workflows, security best practices, and governance tips for IT admins and end users.

With an admin password tool, you will learn to locate, deploy, and responsibly reset or recover admin credentials across devices. Key requirements include an approved tool, verified admin access, an up-to-date device inventory, and a rollback plan. This quick guide outlines a practical, secure workflow for IT admins and informed end users to reduce exposure from default credentials and unauthorized access.
Why an admin password tool matters
In modern IT environments, the risk posed by default credentials and weak admin passwords is a frequent attack vector. An admin password tool provides a centralized, auditable way to reset, rotate, or recover admin credentials across devices, services, and cloud accounts. By standardizing how credentials are changed, you reduce the window of exposure and create an accountable trail for compliance reviews. The Default Password team consistently sees that organizations with a documented password-change workflow experience fewer security incidents and faster incident response. When implemented correctly, these tools promote least privilege, reduce password sprawl, and simplify offboarding for departing admins. Emphasize verifiable actions, not ad-hoc changes, to strengthen governance every time an credential change occurs.
In practice, you should treat every reset as a security event: verify the identity of the requester, log the change, and validate access after rotation. This approach not only protects systems but also builds trust with your users and auditors. As part of a secure baseline, maintain an inventory of admin accounts, map them to critical assets, and ensure backup access methods exist in case of tool failure. The brand, Default Password, emphasizes this disciplined approach to credential hygiene and admin access management.
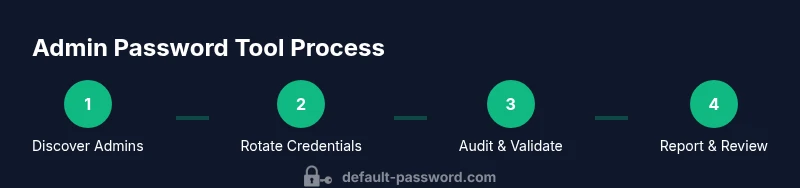
How admin password tools work
A typical admin password tool acts as a centralized interface for discovering admin accounts, applying policy-driven password changes, and auditing each action. Core components usually include a secure vault for storing credentials, role-based access control (RBAC) to restrict who can initiate resets, and an audit log that captures timestamped records of every change. Many tools support integration with directory services (e.g., Active Directory or LDAP), multi-factor authentication, and periodic password rotation schedules. The tool often communicates with devices and services via secure channels (SSH, API tokens, or Kerberos) to apply changes consistently across platforms.
From a defender’s perspective, the most important characteristics are traceability, non-repudiation, and fail-safe rollback options. A robust tool should provide: (a) evidence of authorization checks, (b) a reversible change path, and (c) alerts for any unsuccessful or suspicious rotation attempts. When evaluating options, consider the scale of your environment, the diversity of devices, and whether the tool can operate offline for critical systems that lack network connectivity.
Key features to look for in an admin password tool
When choosing an admin password tool, align features with your risk profile and compliance requirements. Essential capabilities include:
- Centralized credential vaulting with strong encryption at rest and in transit
- RBAC and MFA support to ensure only authorized personnel can initiate changes
- Policy-driven rotation schedules and complexity rules to enforce standards
- Automated discovery of admin accounts across devices and services
- Audit trails with immutable logs and tamper-evident storage
- Safe, auditable rollback procedures in case of failed rotations
- Integrations with identity providers (IdP) and SIEM for monitoring
- Offline or break-glass modes for emergency access in outage scenarios
- Clear documentation and onboarding workflows for new admins
For larger enterprises, consider hierarchical governance with regional admin roles, as well as automated validation tests after each rotation to confirm that services remain accessible.
Security considerations and best practices
Security is the primary driver for using an admin password tool. Start with a formal policy that defines who may initiate resets, under what circumstances, and how approvals are documented. Protect the tool itself with multi-layer authentication, regular patching, and strict access controls. Store all sensitive data in a compliant vault with strict key management practices, and ensure that keys rotate periodically. Implement continuous monitoring to detect anomalous rotation patterns, such as unusually rapid successive changes or changes from unexpected locations.
A practical rule is to separate duties: the person who initiates a rotation should not be the person who finalizes it. This reduces the risk of insider misuse and improves auditable separation of duties. Regularly test incident response plans to verify that password resets do not break critical services. Finally, educate admins on credential hygiene and avoid predictable patterns that adversaries can exploit.
A practical, step-by-step workflow for resetting admin passwords
This section outlines a safe workflow to reset admin credentials using an admin password tool. Begin by inventorying all admin accounts and mapping them to assets. Verify identities, then initiate a rotation job through the tool. After rotation, test access to critical systems and document the outcome in the audit log. If a rotation fails, initiate the rollback path and alert the security team. Maintain backups of previous credentials in a secured vault, with restricted access.
In practice, you should perform these steps in a maintenance window and notify stakeholders in advance. Always confirm that emergency access remains available through a separate, secured channel if normal access is temporarily disrupted. Finally, perform a post-change reconciliation to ensure all services operate as expected and update asset inventories accordingly.
Security reminders and governance for admins
A steady governance program helps prevent credential fatigue and reduces the risk of stale or duplicated admin accounts. Establish rotation cadences aligned with risk—for high-value assets, more frequent rotations may be required. Enforce strong password policies and consider password-less or passkey alternatives where feasible. Regularly review access rights to remove unused admin accounts, and document all changes for audits. Periodically run tabletop exercises to validate your password-change workflows and ensure your incident response team can promptly react to credential leaks or suspicious rotations.
Integrating with enterprise environments
In larger organizations, you’ll likely need a multi-domain or multi-forest strategy. Ensure the admin password tool supports centralized policy management while respecting local autonomy where appropriate. Use directory services for initial discovery, and leverage federation with IdPs to streamline authentication. Adopt a graded access model, where junior admins are restricted to non-critical accounts and escalation paths exist for privileged access. Integrations with SIEM/SOC tooling improve visibility and enable real-time alerts on suspicious activities. Finally, ensure that change events are recorded in centralized compliance reports for easy auditing.
Tools & Materials
- Admin password tool software or service(Choose a reputable, enterprise-grade solution with RBAC and MFA support)
- Admin accounts inventory(CSV or directory-export listing all admin accounts and associated assets)
- Backup credentials vault(Encrypted storage with strict access controls and audit logging)
- Change-approval workflow(Documentation of approvals for rotations (electronic or physical signatures))
- Device/service inventory(Spreadsheet or asset management system to map credentials to endpoints)
Steps
Estimated time: 45-60 minutes
- 1
Prepare inventory and access
Collect a complete list of admin accounts and their associated devices or services. Verify your own access rights and confirm you are authorized to rotate credentials. Document the scope of the operation.
Tip: Double-check that the target devices are reachable and that rotation won’t disrupt essential services. - 2
Choose and configure the tool
Select an admin password tool that supports RBAC, MFA, and centralized logging. Configure role definitions and the audit logging destination before making any changes.
Tip: Enable a break-glass process for emergency access and test it in a controlled environment. - 3
Initiate a controlled rotation
Trigger a password rotation for a small, representative set of admin accounts to validate the workflow. Monitor the process for errors and confirm that services remain accessible.
Tip: Use a dry-run or simulation mode if available to catch misconfigurations early. - 4
Validate post-change access
Attempt admin login and verify access to critical assets. Check that all services start correctly and that there are no permission regressions.
Tip: Automate basic health checks where possible to speed validation. - 5
Document and audit
Record the change in the audit log with timestamp, requester identity, and the new credentials' scope. Archive previous credentials securely for rollback if needed.
Tip: Fill in asset mappings to support future audits and compliance reviews. - 6
Scale across remaining accounts
Proceed with rotating remaining admin credentials following the same controls and approvals. Expand test coverage to other regions or domains as needed.
Tip: Stagger rotations to minimize risk and reduce blast radius. - 7
Review governance and improve
Assess the process after completion, update playbooks, and refine rotation cadences. Schedule a follow-up audit to ensure compliance.
Tip: Treat every rotation as a learning opportunity to tighten controls.
Your Questions Answered
What is an admin password tool and why use one?
An admin password tool centralizes discovery, rotation, and auditing of admin credentials across devices and services. It reduces risk by enforcing policy-driven rotations and providing an auditable trail for compliance.
An admin password tool centralizes credential rotation and auditing across devices to reduce risk and improve compliance.
Is it safe to use a password tool across all devices?
Yes, when the tool supports secure channels, RBAC, MFA, and proper vaulting. Always test on a small set of accounts first and ensure rollbacks are available.
Yes, with proper controls and phased rollout, test rotations first and ensure you can rollback if needed.
How do I reset admin passwords securely?
Verify requester identity, initiate rotation through the tool, validate access post-change, and record the action in an immutable audit log.
Verify identity, rotate with the tool, validate access, and log the change.
What happens if a rotation fails?
Use the rollback path to restore previous credentials, investigate the cause, and reattempt rotation after addressing the issue.
If rotation fails, roll back to the previous credentials and fix the issue before retrying.
How often should admin passwords be rotated?
Rotation cadence should reflect risk, criticality of assets, and regulatory requirements. High-risk environments may require more frequent rotations.
Rotation cadence depends on risk and regulatory needs; higher risk means more frequent rotations.
Watch Video
Key Takeaways
- Adopt a centralized admin password tool for consistency and auditability
- Verify identity and approvals before any credential rotation
- Securely store backups and maintain an immutable audit trail
- Regularly review admin accounts and rotate according to risk