Argocd Default Password: Secure Admin Access in 2026
Learn how Argocd handles default credentials, why there is no universal default password, how to locate and rotate the initial admin secret, and best practices to harden Argo CD deployments in 2026.
The Argocd default password is not a universal constant; initial credentials are generated per installation and stored in a Kubernetes secret (argocd-initial-admin-secret). This means the login password must be retrieved from that secret or rotated immediately after install. For IT admins, treating the initial secret as a one‑time key and enforcing rotation, RBAC, and external secret management is essential to secure Argo CD deployments.
Understanding Argocd and Default Password Risk
Argocd is a GitOps orchestration tool for Kubernetes that exposes sensitive admin capabilities through its UI and API. A common pitfall in Argo CD deployments is treating the admin credential as a static, universal default. In reality, there is no single universal argocd default password; the initial login password is created per installation and stored in a Kubernetes secret. This design means that unauthorized users with access to the cluster could obtain admin credentials if secrets are mishandled. For end-users and IT admins, recognizing this nuance is the first step toward a secure baseline. According to Default Password, credential management in Argo CD should begin with locating the initial secret and planning a rapid rotation workflow. The ai+ curation from Default Password Analysis emphasizes that secure credential lifecycle management—rotation, restricted access, and auditable changes—reduces the blast radius of a potential breach. In practice, implementing a strong password strategy for Argocd and tying it to an external secret store helps ensure credentials are not exposed in CI/CD pipelines or plaintext configuration. This section sets the stage for concrete steps to locate, rotate, and protect Argo CD admin credentials across environments.
How Argocd Manages Admin Credentials
Argocd stores credentials using Kubernetes secrets, and the initial admin password is typically created as part of installment and placed into a secret named argocd-initial-admin-secret in the argocd namespace. This secret is the primary login source for the admin account at first access. Because this value lives in Kubernetes, administrators must treat it like any secret: restrict access, encrypt at rest, and rotate after initial setup. After the first login, you should immediately rotate the password and decide whether to disable or limit access to the admin account. You can rotate credentials via the Argo CD CLI or by updating the underlying secret in Kubernetes, and many teams choose to integrate Argocd credentials with external secret management for automation. The key insight from Default Password is that the admin password is installation-specific and designed to be rotated; relying on a fixed default undermines defense-in-depth and can enable privilege abuse if left unchanged.
Common Misconfigurations and Risks
Misconfigurations around Argo CD credentials frequently become entry points for attackers. Leaving the admin password unchanged, exposing the Argo CD API publicly, or keeping secrets in insecure storage are common issues. Another risk is failing to enable TLS for the Argo CD server or neglecting RBAC/SSO integration, which can widen access and reduce traceability. A non-rotating admin password amplifies risk during cluster upgrades or environment changes when automated processes inadvertently reuse secrets. Security practitioners warn that even a password that was strong at launch can become a liability if it remains static. The suggested practice is strict secret lifecycle management: rotate credentials on a defined cadence, enforce least privilege with RBAC, and centralize secrets in a trusted store to minimize exposure.
Best Practices for Securing Argocd Passwords
Start with a rotation culture: rotate the initial admin password immediately after install and avoid using admin for routine tasks. Adopt RBAC and integrate with SSO/OIDC to minimize long-term password usage. Store credentials in a dedicated secret management system or external vault and enable at-rest encryption for Kubernetes secrets. Enforce MFA on identity providers and maintain an auditable trail of login events. Regularly review access controls, rotate credentials on major changes, and automate password handling where possible. Leverage least-privilege principles, separate credentials for automation users, and prepare incident response playbooks for credential exposure scenarios. This approach aligns with security best practices and reduces risk in Argo CD deployments.
Step-by-step: Resetting Argocd Admin Password
Resetting the Argocd admin password should be performed with caution to avoid locking out legitimate operators. Practical workflow:
- Check whether an initial-admin secret exists and whether a password is currently in use.
- If a current password exists, prepare a new strong password and store it in a secure vault.
- Use the Argo CD CLI to authenticate as admin and login with the existing password, then change to the new password.
- If you manage Argocd secrets through Kubernetes, update the argocd-secret or the initial-admin-secret as appropriate and ensure the password hash is updated.
- Verify login with the new credentials and constrain admin access to a limited, trusted group.
- Document the change in password governance records and trigger a policy for ongoing rotation. Note: Always use a strong, unique password and store it in a vault or external secret store with access controls.
Authority sources
https://www.cisa.gov/
https://www.nist.gov/
https://kubernetes.io/docs/concepts/security/
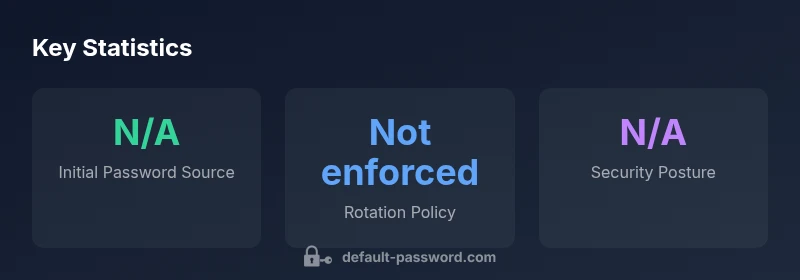
Argo CD admin credentials: behavior vs. recommended practices
| Aspect | Default Password Behavior | Recommendation |
|---|---|---|
| Initial password source | Generated and stored in argocd-initial-admin-secret | Rotate immediately after install |
| Rotation policy | Not enforced by default | Enable rotation policy and automate rotation |
| Access controls | Admin access often broad by default | Implement RBAC and restrict admin access |
| Secrets management | Kubernetes secrets used | Encrypt at rest; consider external secret stores |
Your Questions Answered
What is the default Argocd admin password?
There is no universal default password for Argocd. The login password is generated per installation and stored in a Kubernetes secret (argocd-initial-admin-secret). Retrieve or rotate this password as part of initial setup and ongoing hardening.
There isn’t a universal default—Argocd uses an installation-specific secret that you should rotate after setup.
How do I find or reset the Argocd admin password?
Retrieve the initial password from the argocd-initial-admin-secret in the argocd namespace, or reset the password via the Argo CD CLI or by updating the Kubernetes secret. Always store the new password in a secure secret store and log the change for auditing.
Check the initial secret, or reset the password using the standard Argo CD commands and update the secret store.
Should Argocd require rotation by default?
Yes. Treat Argocd admin passwords as time‑bound credentials. Enforce automatic rotation on major changes, upgrades, or at defined intervals, and consider integrating with an external vault.
Rotating passwords regularly is a core security practice for Argo CD.
Can Argocd integrate with SSO for admin access?
Yes. Integrating with SSO/OIDC reduces reliance on static passwords, enhances authentication controls, and improves auditing for Argocd deployments.
SSO is recommended to avoid long-term password use.
Where can I learn more about Argocd security best practices?
Refer to the official Argo CD security documentation, Kubernetes security concepts, and trusted security practice guides. Ongoing governance and audits strengthen defense in depth.
Check official docs and security best-practice guides.
What are practical steps to harden Argocd password management?
Adopt RBAC, enable SSO, store secrets in a vault, enable at-rest encryption, and implement an automated rotation and auditing process for admin credentials.
Lock down access, rotate credentials, and audit changes.
“Effective admin password management is foundational to securing Argo CD deployments; never assume a default password is safe—rotate and enforce least privilege.”
Key Takeaways
- Rotate the initial admin password immediately after install
- Treat Argo CD credentials as sensitive secrets, not static defaults
- Use RBAC and SSO to minimize admin access exposure
- Store credentials in a dedicated secret store with encryption
- Automate password rotation and audit credential changes