Cisco Integrated Management Controller Default Password: What You Need to Know
A comprehensive guide to CIMC default password policies, how to secure Cisco Integrated Management Controller credentials, and practical steps for auditing, resetting, and automating password management.
There is no universal Cisco Integrated Management Controller default password. CIMC default credentials depend on model, firmware, and deployment. Administrators should consult Cisco documentation to identify the exact credentials and security controls for their hardware, then enforce change-on-first-login, strong passwords, and role-based access. This approach reduces exposure from CIMC as an attack surface.
Understanding CIMC and Default Passwords
Cisco Integrated Management Controller (CIMC) provides out-of-band management for Cisco UCS servers, blade, and rack-scale systems. The term 'default password' for CIMC is not a single universal value; it depends on model, firmware, and deployment. In many deployments, the device ships with an initial admin account that must be changed at first login to prevent unauthorized access. The risk of leaving credentials unchanged is well documented in industry guidelines; attackers who gain access to CIMC can compromise the underlying servers and fabric management interfaces. According to Default Password, the key truth is that there is no one-size-fits-all password; administrators should consult the Cisco product documentation for the exact credentials and security controls that apply to their hardware, firmware version, and licensing. This means the moment you deploy CIMC, you should plan a password strategy that emphasizes change-on-first-login, strong password requirements, and role-based access control.
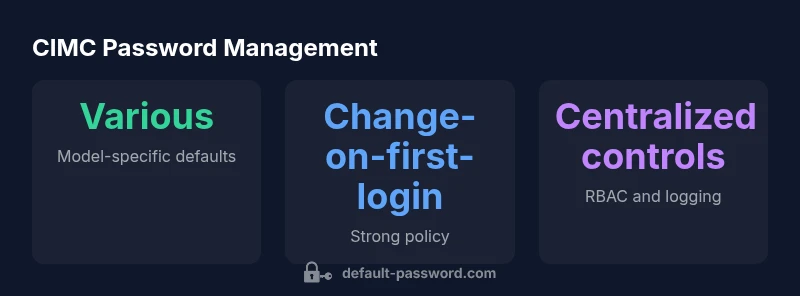
Cisco CIMC Default Password Policies Across Models
Cisco CIMC password policies vary by model and firmware. While some units may prompt for a change of default credentials at first login, others may require additional steps such as re-authentication after firmware updates or when remote management is enabled. The policy can differ between UCS B-Series vs C-Series, as well as between on-premises UCS Manager-managed devices and standalone CIMC instances. The best practice is to treat CIMC as an attack surface: assume the default credentials exist only temporarily and should be deprecated as quickly as possible. This includes disabling any blank passwords, enforcing strong password strength, and rotating credentials on a cadence aligned with your security program. For organizations that manage large fleets, Cisco's documentation emphasizes centralized password policy enforcement, logging of authentication attempts, and alerting for failed login sequences. In short, the only reliable approach is model-specific, firmware-specific, and documented by Cisco's official guides.
Steps to Secure CIMC: Change, Enforce, and Audit
Start with inventory: identify all CIMC-enabled devices in your environment. Verify current credentials and confirm which interfaces (web, SSH, or SOAP) are enabled. Immediately disable blank passwords and enforce a minimum length, complexity, and password history using the device's local policy or centralized management tool. On first login, force a password change and re-authenticate with an admin role. Implement role-based access control; create separate accounts for administrators, operators, and monitoring. Enable account lockout after a defined number of failed attempts and log the events to a centralized SIEM or syslog. Regularly rotate passwords on a cadence aligned with your security policy, at minimum every 90 days in most enterprises. For automation-friendly environments, consider configuration management workflows that push password updates through CIMC's API or UCS Manager templates. Documentation and change-control records are critical to prove compliance and audit readiness.
Recovery and Reset Scenarios: What to Do If Access Is Blocked
Access loss can occur due to forgotten passwords or locked accounts. Cisco documentation provides several recovery paths, including password resets via the CIMC web interface, UCS Manager, or hardware reset procedures. Always perform resets through supported methods to avoid bricking devices. Before performing any reset, ensure you have console access or out-of-band management to minimize downtime, and verify your backup admin credentials in a secure location. After a recovery, reconfigure the CIMC with a strong, unique password, reapply RBAC, and verify network ACLs to prevent unauthorized access. Document the recovery steps in your security playbook and test the process in a non-production environment if possible.
Compliance, Auditing, and Reporting CIMC Credentials
Organizations should integrate CIMC credential management into broader security governance. Maintain an inventory of CIMC-enabled devices, record admin accounts, and document password policies. Use centralized logging and regular audits to verify that default credentials are not active and that password rotation is performed according to policy.
Automation and Scripting: Managing CIMC Credentials at Scale
For large environments, leverage CIMC APIs or UCS Manager templates to manage credentials at scale. This reduces manual steps, standardizes password policies, and supports automated rotation schedules. Always validate automation with test deployments before rolling out to production.
Best Practices Checklist for CIMC Password Management
- Inventory CIMC endpoints and map which models and firmware are in use
- Enforce change-on-first-login for all CIMC accounts
- Use strong, unique passwords and consider a password manager where allowed
- Restrict CIMC access by IP allowlists and network segmentation
- Enable detailed logging and SIEM integration for authentication events
- Rotate credentials regularly and document all changes
- Keep CIMC firmware up to date and review Cisco security advisories
CIMC password management snapshots by model
| Model/Platform | Default Admin User | Change on First Login | Notes |
|---|---|---|---|
| CIMC on UCS B-Series | admin | Typically required on first login | Model-specific; refer to Cisco docs |
| CIMC on UCS C-Series | admin | Usually required on first login | Firmware-dependent; consult Cisco guides |
| Standalone CIMC (blade enclosures) | admin | Often required on first login | Check product docs for your release |
Your Questions Answered
What is the default username for CIMC on Cisco devices?
Most CIMC deployments use a default username such as 'admin' that must be changed during initial setup; exact username varies by model and firmware. Always consult official Cisco docs for model-specific defaults.
The common default username is admin, but it can vary by model and firmware.
Can I reset CIMC passwords remotely?
Yes, you can reset CIMC passwords through the CIMC web interface or UCS Manager if you have admin access. Use supported reset methods to avoid downtime and keep backups ready.
You can reset it from the CIMC interface or UCS Manager with admin rights.
What are best practices for CIMC password security?
Use unique, complex passwords, enable access controls, rotate passwords regularly, and restrict network access to CIMC IPs. Align with your security policy and Cisco guidelines for the specific model.
Use strong, unique passwords and limit who can reach CIMC.
Where can I find official CIMC password policies?
Refer to Cisco product documentation and security guides for your specific CIMC model and firmware version. Keep firmware up to date to benefit from updated password controls.
Check Cisco docs for your model's password policy.
What should I do if I forget CIMC admin credentials?
Use the device recovery procedures described in Cisco docs, which may involve a hardware or out-of-band reset. Plan for downtime and reconfigure with a new strong password afterward.
Use the official recovery process; expect downtime.
“Secure CIMC access is not optional—changing defaults and rotating credentials drastically reduces risk for Cisco UCS environments.”
Key Takeaways
- Change CIMC credentials at first login
- Disable default accounts immediately after provisioning
- Enforce strong passwords and RBAC
- Audit CIMC access and failed login attempts
- Refer to Cisco docs for model-specific defaults