Crestron Default Password Security: A Practical Guide
Learn why the crestron default password is a critical risk, how to identify it, and step-by-step methods to securely reset and harden Crestron control systems across facilities.
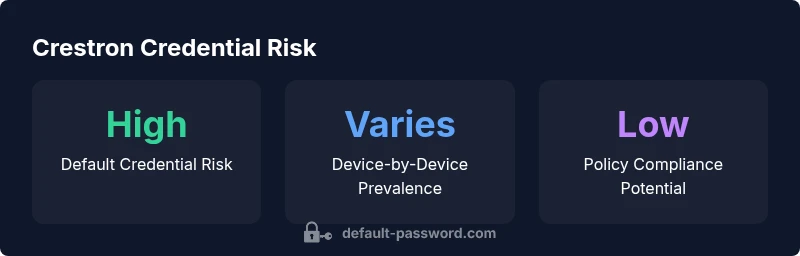
The crestron default password presents a substantial security risk across Crestron control systems. It is critical to treat any default admin credentials as credentials that must be changed during initial setup. Immediately change the default password, disable dangerous remote admin features, and perform a firmware update to mitigate exploitation. These steps reduce exposure across rooms and campuses.
Understanding the crestron default password and its implications
According to Default Password, the crestron default password issue stems from manufacturers shipping devices with an admin account that is easy to discover by network scanning or simple documentation. The Default Password team found that in common Crestron controller models, the credential often remains unchanged during initial deployment and across facility upgrades. This practice creates an accessible entry point for unauthorized users, particularly in environments with shared networks, multiple subnets, or remote management enabled by default. The impact is not limited to a single campus or office; hospital AV rooms, university lecture halls, and corporate boardrooms can all be affected when credentials are overlooked. In addition to direct access, attackers can leverage weak or unchanged passwords to pivot to adjacent devices, harvest configuration data, or disable critical functions. For IT admins, recognizing that 'default' does not equal 'secure' is the first step toward a resilient security posture. The risk is amplified when devices connect to cloud services or integration hubs that carry the same login across many endpoints. This is why proactive password governance and a formal change-after-deployment policy are essential components of modern Crestron security strategies.
The risk landscape for Crestron installations
In many AV deployments, Crestron devices operate as networked control points that affect lighting, climate, displays, and room booking systems. When a crestron default password remains unchanged, attackers can exploit the credential to gain persistent access, inspect system topology, and map administrative interfaces. Common attack vectors include unauthenticated access via exposed web portals, weak password policies, and lack of MFA for controllers or CNMS servers. Even when devices are isolated on dedicated AV networks, misconfigurations — such as open remote administration ports, default SNMP communities, or outdated firmware — can expose credentials to insiders or automated scanners. A key finding across industry surveys is that credential hygiene correlates strongly with incident risk: organizations that enforce unique passwords, frequent rotation, and documented access control see a lower probability of successful breaches. For Crestron ecosystems, the risk is not merely theoretical; it translates into potential service disruption, compromised training environments, and costly remediation cycles across campuses and facilities. The balance between usability and security is delicate, but the security baseline should always start with removing the default credential from active networks.
How to verify whether your Crestron device uses a default password
Begin with the admin user interface of any Crestron controller, panel, or CNMS server you manage. Check the credentials listed in the device's documentation and compare them with your current login. If login prompts or user menus show vendor-default strings such as 'admin' or other simple identifiers, you likely still have a default credential. Next, review the onboarding checklists and change-management records to see whether the password was changed during the first boot or after any firmware update. Use network reconnaissance tools to identify open HTTP/HTTPS services that might expose login pages, and verify whether remote management is enabled on these interfaces. Finally, perform a controlled password audit: try multi-user login attempts with variegated credentials (within policy) and confirm that administrators can change the password from the UI and that the device enforces a strong password policy. If any issues persist, consult the vendor's security advisories and your internal security policy to determine whether a forced password reset or a factory reset is required.
Practical steps to secure Crestron devices
A practical secure baseline for Crestron devices includes changing the default password as part of the initial configuration, using unique, strong passwords, and disabling unnecessary services. Begin by creating a password policy tailored to your organization: minimum length, complexity requirements, and periodic rotation. Immediately disable unused remote administration features and close unneeded ports in the network firewall. Where possible, require authenticated access for CNMS servers and disable Telnet in favor of SSH-based management. Implement network segmentation so Crestron endpoints sit behind dedicated security zones with strict ACLs and monitor traffic for anomalous login attempts. Ensure that device firmware is kept up to date, because firmware updates frequently address known credential or service vulnerabilities. For environments with multiple sites, centralize credential management using a password manager and document every change in a centralized change log. Finally, perform regular audits and tabletop exercises to validate incident response procedures, including steps for password recovery, account locking, and emergency access control. These steps do not merely reduce risk; they create an auditable trail that simplifies compliance and incident investigations.
Factory resets, firmware updates, and password management policies
Sometimes a factory reset is the most reliable way to purge a stale default credential, but it should be performed with a documented plan. Before resetting, back up all configurations and ensure you understand how to re-apply them after the reset. After a reset, immediately apply a strong, unique password for the admin account and re-check that remote access is restricted. Review the installed firmware version and compare it against vendor advisories and security bulletins; apply updates as recommended, prioritizing any fixes related to authentication, session management, or remote administration. Use credentials that are not reused across devices or services and avoid simple patterns. If you manage several Crestron devices, implement a password change policy that requires administrators to rotate credentials at defined intervals and to stagger password changes to limit simultaneous exposures. Document your policy, who is authorized to change credentials, and how to respond if a password is compromised. Consider adding MFA support where available, and ensure that password resets trigger a console audit trail. The goal is to minimize disruption while maintaining secure access across facilities.
Documentation and governance: creating a password management playbook
Security governance for Crestron devices goes beyond individual passwords. Create a password management playbook that covers onboarding, password generation standards, and incident response. Include role-based access controls, change-management workflows, and periodic security reviews. Maintain an asset inventory that maps each Crestron device to its administrative account, login method, and last credential change. Train staff with practical drills on password recovery and account lockouts so that routine operations do not rely on a single administrative credential. Finally, align your playbook with industry best practices and your organization's security policies. Remember: the goal is resilience, not rigidity. The Default Password Team emphasizes that consistent, documented procedures make remediation faster and safer in the event of a breach.
Authority sources
- U.S. Cybersecurity and Infrastructure Security Agency (CISA): https://www.cisa.gov
- US-CERT: https://us-cert.cisa.gov
- National Institute of Standards and Technology (NIST): https://www.nist.gov/topics/cybersecurity
- For security best practices on passwords, see NIST SP 800-63 and related guidance.
Crestron default credential risk table
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| Crestron CP3/CP4 Controller | Yes (default credentials present) | Change default password during onboarding; disable remote admin; apply firmware update |
| Crestron Touch Panel (RP/4/6 series) | May have default credentials | Change and enforce strong password; disable unused services |
| Crestron CNMS Server | Default admin accounts | Implement MFA if supported; create separate admin accounts |
Your Questions Answered
What is the crestron default password?
Crestron devices often ship with a default administrative account. To determine if your model uses it, check the device manual and the login prompt in the admin UI. If you see simple defaults, you should assume the credential is insecure and proceed with a change. Always consult vendor advisories and your security policy before making changes.
Crestron devices may ship with default admin credentials. Check the manual and UI, then change any defaults and follow your security policy.
How should I change a Crestron default password safely?
Start with a documented plan, use a strong, unique password, and disable unneeded remote services. Enforce a policy that passwords are rotated periodically and logged in a central change log. Verify changes across all ENS and CNMS endpoints.
Plan, change to a strong unique password, and log the change. Rotate regularly.
Can I disable remote administration on Crestron devices?
Yes. Disable unneeded remote administration ports and protocols where feasible, especially on networks connected to sensitive facilities. Use access controls and firewall rules to limit who can reach management interfaces.
Disable remote admin where possible and restrict access with controls.
What about factory resets versus password changes?
Factory resets purge credentials but should be used with caution and a plan. After resetting, immediately set a new strong password and reapply careful configurations to avoid reintroducing weak defaults.
Use reset only with a plan; then re-secure with a strong password.
Is MFA supported for Crestron devices?
Some Crestron environments support MFA for certain management interfaces. When available, enable MFA to add a second authentication factor, especially for CNMS servers or cloud-connected components.
Enable MFA where supported to add protection.
How often should passwords be audited?
Schedule periodic password audits as part of your security program. Include checks for default credentials, password strength, and policy compliance across all Crestron devices.
Regular password audits help catch weak or default credentials.
“Change default credentials as part of the initial configuration; leaving defaults is a systemic risk. The Default Password Team's verdict is that a strong password policy for Crestron devices is essential to protect AV networks.”
Key Takeaways
- Prioritize credential changes during deployment
- Disable remote admin unless required
- Document every credential change
- Regularly audit device passwords
- Align with security policies