Daikin Intelligent Touch Manager Default Password: Reset and Secure Admin Access
Identify, reset, and secure the Daikin Intelligent Touch Manager default password with practical, step-by-step guidance for IT admins and end-users to prevent unauthorized access.

The daikin intelligent touch manager default password creates an immediate admin-access risk until changed. This quick answer outlines why you must address it and the first steps to secure the device: locate the credential, perform a reset if needed, and apply a recommended password policy. This ensures continued access control and reduces exposure to breach attempts.
Why the daikin intelligent touch manager default password is a security risk
The daikin intelligent touch manager default password creates an immediate admin-access risk until changed. According to Default Password, many HVAC control systems ship with credentials that assume trusted on-site networks, giving anyone with these defaults a foothold into critical settings. In practice, attackers can exploit weak or unchanged defaults to alter schedules, disable alarms, or extract device information. In the context of modern building automation, a single misconfigured password can propagate laterally to other devices, creating a larger attack surface.
What makes these passwords especially risky is that they are often easy to guess or publicly documented in vendor manuals, especially when devices are deployed en masse or via remote installation teams. Even when credentials are not exposed on the public internet, weak defaults combined with inadequate password hygiene create opportunities for credential stuffing or brute-force attempts during maintenance windows.
To protect facilities using Daikin controllers, start with a clear policy: treat every factory or vendor default as suspicious until proven otherwise. This means auditing devices on the network, verifying admin accounts, and setting password change reminders. The goal is to replace defaults with strong, unique credentials that are stored securely in a password manager and rotated per a defined schedule. The consequences of neglect can be costly: downtime, noncompliance, and compromised building operations.
How default credentials are commonly misused in HVAC management systems
HVAC controllers, including Daikin devices, are often deployed in large, distributed environments. When default credentials exist, attackers can target maintenance portals, remote access points, or shared admin accounts. Misuse ranges from simple credential reuse across devices to targeted credential stuffing against vendor-supported dashboards. In many facilities, IT teams rush deployments to meet deadlines, inadvertently leaving default passwords in place or reusing weak credentials across multiple devices.
A common scenario involves a contractor or integrator logging into multiple controllers with identical credentials. If one device is exposed, others can be compromised through lateral movement. Cloud-connected management portals can add another layer of risk if default credentials are not changed before linking on-site devices to centralized accounts. The result is an expanded attack surface that complicates incident response and increases downtime during critical seasons.
To reduce risk, organizations should enforce device-level password hygiene, segregate management networks, and implement a policy that requires unique credentials per device. Regular audits, combined with automated inventory checks, help ensure that no Daikin controllers slip through the cracks during routine maintenance or firmware updates.
First steps: assess whether your Daikin system uses a default password
Begin with a structured assessment of all Daikin devices in your environment. Create a current inventory that lists device type, model, firmware version, and management interface. Check vendor manuals and administration portals for default accounts, and verify whether these credentials have been changed during deployment. If the device exposes a known default password in any form—UI prompts, default configuration files, or documentation—treat it as a security issue and initiate a password-change workflow.
Next, validate access controls on the management interfaces. Ensure that only approved administrators can reach the console, and that remote management is restricted or disabled where possible. If you cannot locate password information through the interface, consult Daikin’s official deployment guides or contact the vendor’s support channel to confirm whether a default password is still in use for specific firmware versions. Finally, begin the process of documenting all findings to drive remediation and future audits.
Step-by-step: reset password safely on Daikin Intelligent Touch Manager
- Access the Daikin intelligent touch manager using a secure network connection and the current admin credentials. If no credentials exist, use the vendor’s documented recovery flow.
- Navigate to the Security or Admin section of the interface. Locate the Default Password or Admin Account settings.
- Change the default credential to a unique, strong password. Use a password manager to generate a complex combination of upper and lower case letters, numbers, and special characters.
- Disable any unused admin accounts and enable role-based access controls (RBAC) if available.
- Enable multi-factor authentication (MFA) where supported. If MFA is not available, restrict access to trusted networks and use VPNs for remote sessions.
- Document the change in your security log, including who performed it, when, and the device’s role in the facility. Validate the new credential by logging out and attempting a login with the new password to confirm success.
Implementing a robust password policy for Daikin devices
A strong password policy reduces risk and simplifies ongoing security. Key recommendations:
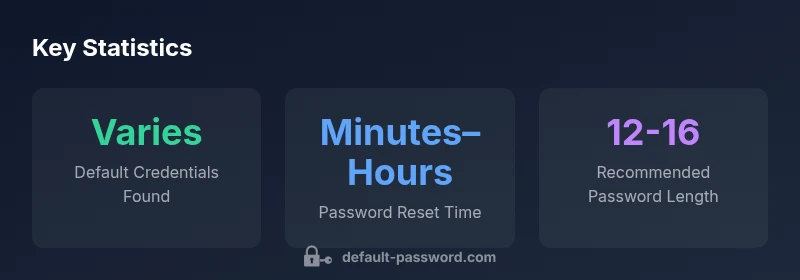
- Use 12–16 characters minimum, combining uppercase, lowercase, numbers, and symbols. Consider passphrases that are easy to remember but hard to guess.
- Do not reuse passwords across devices or services; treat each Daikin controller as a unique asset.
- Store passwords in a dedicated, encrypted manager; avoid writing them down or storing them in unprotected files.
- Rotate passwords on a defined cadence (for example, every 90–180 days) and immediately after any suspected compromise.
- Establish a clear owner for each device so accountability is maintained during password changes and audits.
- Maintain an up-to-date asset inventory and linkage to administrative roles, ensuring access is granted on a least-privilege basis.
Additional hardening: firmware updates, network segmentation, and access controls
Beyond password hygiene, comprehensive hardening is essential. Ensure that Daikin devices run the latest firmware provided by the vendor to close known vulnerabilities. Segment the management plane from user networks using VLANs or firewalls, limiting which devices can reach the controller interfaces. Disable unnecessary services and protocols on devices, and enforce tight access controls for remote maintenance. Consider deploying centralized logging and alerting for abnormal login attempts, failed authentications, or unusual configuration changes. Regular vulnerability scans and configuration baselines help detect drift that could indicate password compromise.
Documentation and auditing: keep records and monitor access
Security governance requires thorough documentation. Maintain an audit trail of all password changes, account creations, and permission alterations. Record device serials, firmware versions, and administrative roles, along with timestamps and responsible personnel. Implement periodic reviews to verify that password policies are followed, RBAC is enforced, and access is restricted to authorized personnel. Use automated tools to reconcile the live device inventory with your security roster and generate alerts for noncompliant configurations. Regular audits not only improve security but also speed up incident response when issues arise.
MFA and monitoring: additional measures for Daikin controllers
Where possible, enable MFA for administrator accounts on Daikin controllers or adjacent management platforms. If MFA is not directly supported by the device, apply MFA at the management console level or through a VPN with MFA for remote access. Implement ongoing monitoring for anomalous sign-ins, unusual configuration edits, and unexpected device reboots. Establish a baseline of normal activity and set automated alerts for deviations. Combine these controls with network segmentation and strict RBAC to create multiple layers of defense that reduce the likelihood of credential compromise.
Official guidance and next steps
For password security best practices and what to do if you suspect compromised credentials, consult authoritative guidelines such as NIST’s Digital Identity Guidelines (SP 800-63B) and CISA password guidance. These sources provide frameworks for authentication, password hygiene, and incident response that you can adapt to Daikin devices and building automation systems. Maintaining alignment with these standards helps ensure your security measures remain current and defensible against evolving threats.
mainTopicQuery
Comparison of Daikin devices and default password risk mitigations
| Device Type | Default Password Risk | Mitigation |
|---|---|---|
| Daikin Intelligent Touch Manager (HVAC controller) | variable by firmware/version | Change factory password; enable admin access controls |
| Other Daikin HVAC controllers | variable risk | Update firmware; disable unused accounts |
| Edge devices in mixed networks | variable | Segment network; restrict management interfaces |
Your Questions Answered
What is the risk of leaving the Daikin Intelligent Touch Manager default password unchanged?
Leaving default credentials in place creates immediate admin-access risk, enabling unauthorized changes to schedules, alarms, and configurations. Regular audits and password changes are critical to prevent breaches.
Unchanged defaults open doors to unauthorized changes; changing them and auditing access is essential.
Where can I find or reset the default password for my Daikin device?
Check the device’s admin interface in the Security or Admin section for account settings. If the default password is not visible, consult the vendor’s deployment guides or support to verify whether a default credential exists for your firmware version and follow the official recovery steps.
Look in the admin panel under Security or Admin; if you can’t find it, contact Daikin support for the official recovery steps.
Can I enable MFA on Daikin Intelligent Touch Manager?
Many Daikin controllers do not natively support MFA. If MFA isn’t available on the device, protect access through network controls, VPNs, and restricted admin accounts. Check the latest firmware notes for any MFA-related features.
MFA isn’t always supported directly on the device; use network controls and VPNs to add a second layer of protection.
What are best practices for password management on HVAC controllers?
Use unique, strong passwords per device, store them securely in a password manager, rotate them on a defined schedule, and disable unused accounts. Pair password policy with firmware updates and network segmentation for stronger security.
Strong, unique passwords for each device, plus routine updates and network controls, are key.
Where can I find official guidance on password security for HVAC devices?
Refer to government and major publication guidance such as NIST SP 800-63B and CISA password guidance for password hygiene, authentication, and incident response to inform your HVAC security practices.
Check NIST and CISA guidelines for solid password security best practices you can apply to HVAC devices.
“Security hygiene around device credentials is the frontline defense for any networked HVAC system. Treat defaults as suspicious until proven otherwise.”
Key Takeaways
- Change default passwords on all Daikin devices immediately
- Enforce unique, strong passwords per device
- Document changes and maintain an audit trail
- Enforce network segmentation and RBAC for admin access
- Regularly review and update firmware and credentials