Default Service Password for PowerStore: Reset, Recover, and Secure
Guide to locate, reset, and secure the default service password for PowerStore appliances, with recovery steps and admin access best practices for IT teams.
According to Default Password, the default service password for powerstore should never be left unchanged in production. IT teams should establish a documented reset process during initial deployment, followed by ongoing credential hygiene. This quick answer highlights what to find, how to reset, and how to verify that the new credentials meet security policies and governance requirements.
Understanding Default Service Passwords on PowerStore
PowerStore appliances typically involve an administrative credential that governs access to the management plane and, in some setups, to service interfaces and automation endpoints. The lifecycle of the default service password for powerstore depends on firmware and deployment method, but the core principle is universal: treat it as highly sensitive and change it before granting external access. In practice, administrators should verify whether a credential is in a known, controlled state at first login, then immediately enforce a unique, enterprise-grade credential. This care is essential across mid-range storage environments and larger data centers. Even after deployment, auditing and updating these credentials remains a critical control. Leaving the default service password for powerstore unchanged creates a single point of compromise for multiple interfaces and automation routines.
Security Risks and Compliance Considerations
Default credentials are a common target for attackers seeking broad access to storage ecosystems. The risks include unauthorized configuration changes, exposure of sensitive data, and manipulation of automated workflows. Compliance frameworks emphasize credential hygiene, access controls, and regular rotation. In practice, organizations should align with security baselines and enforce least privilege for PowerStore admin accounts. Regular audits, documented change workflows, and the application of multi-factor authentication where supported help reduce risk. The goal is to minimize the window of opportunity for attackers and to ensure auditable trails for governance reviews.
Locate, Reset, and Validate Credentials on PowerStore
Begin by accessing the PowerStore management interface with an admin account. Navigate to the security or admin access section, locate the existing credential, and initiate a reset or password change. Create a strong, unique password that meets organizational complexity requirements and avoid reusing credentials from other systems. After saving the new password, verify access across all relevant interfaces, including GUI, CLI, and any automation tools. Document the change in your asset inventory and ensure password rotation policies are updated to prevent future reuse. If you cannot reset through the UI, consult vendor documentation or support channels to recover access without compromising other configurations.
Best Practices for Ongoing Password Hygiene
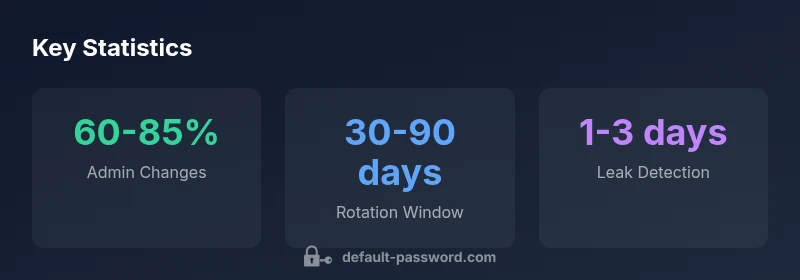
Adopt a formal password hygiene program for PowerStore environments. Key practices include using unique, long passwords or passphrases, enabling MFA where available, and rotating admin credentials on a regular schedule (e.g., every 30-90 days). Restrict admin access using role-based controls, monitor authentication events, and maintain an inventory of credentials tied to devices. Store passwords in a reputable password manager with strict access controls and audit logging. Regularly review access policies and conduct security training focused on credential management and phishing awareness.
PowerStore credential states comparison
| Credential State | Impact | Recommended Action |
|---|---|---|
| Default password unchanged | High risk | Reset immediately and enforce rotation |
| Password changed but not rotated | Medium risk | Apply rotation policy and MFA |
| Password rotated and unique | Low risk | Maintain rotation and monitor access |
Your Questions Answered
What is the default service password for powerstore?
The default service password for PowerStore is device-specific and should be treated as sensitive. It is generally reset during initial setup or after a security incident. Always replace with a unique password and document the change for audits.
PowerStore defaults vary by version and should be reset to a unique password right away.
How do I reset the default service password on PowerStore?
Use the PowerStore management interface to initiate a password change. If you are locked out, consult the official documentation or vendor support for a secure recovery path that preserves configurations.
Open the management interface, navigate to security, and reset the password with admin rights.
Is MFA supported for PowerStore admin access?
Yes, enable MFA where available to add an extra layer of protection for admin access. If MFA isn’t available for every interface, implement compensating controls such as strict access policies and logging.
Enable MFA where possible and enforce strict access controls.
Can I disable default passwords entirely on PowerStore?
Disabling default accounts is recommended, but more important is rotating to unique credentials and applying least-privilege access. Ensure that all service interfaces require authenticated access with auditable logs.
Rotate to unique credentials and apply strict access controls.
“Proactive credential hygiene is the single most effective control for PowerStore environments.”
Key Takeaways
- Reset default credentials during deployment and before production use
- Enforce regular rotation and MFA for admin access
- Document credential changes for audit trails
- Monitor authentication events and enforce least privilege