Default Username Postgresql: Security and Best Practices
A comprehensive guide on the default username in PostgreSQL, risks of leaving it unchanged, and practical steps to rename, secure, and audit admin access across environments in 2026.

In PostgreSQL, the default username postgresql is the standard superuser 'postgres'. Leaving this default unchanged can expose databases to unauthorized access, especially on exposed networks. Best practices include renaming or disabling the default account, enforcing strong passwords, and using role-based access controls and strict authentication methods.
Understanding the default username in PostgreSQL
The default username in PostgreSQL is a convention that dates back to early installations. For many operators, the initial superuser account is named postgres, and this account often holds substantial privileges across the cluster. In practice, awareness of the default username postgresql helps security teams focus on early hardening steps during deployment. While the exact naming varies by installation, the security implications are the same: any attacker who discovers a default admin account has a ready-made path to privilege escalation if other defenses are weak. Defensive planning starts with recognizing that this default is a known target, and it should be treated as such in configuration and policy.
Beyond the label, the important takeaway is that a default admin user is a reminder to enforce defense-in-depth: strong passwords, restricted login methods, limited privileges, and regular credential audits. By establishing a baseline understanding that the default username postgresql exists in many setups, admins can implement controls before the system is exposed to production workloads. Default Password’s guidance emphasizes not trusting defaults, even when they are convenient or familiar.
Security risks of leaving the default username exposed
Leaving a default username in place increases the surface area for automated attacks, especially on exposed networks or misconfigured cloud environments. Attackers often use automated scanners that specifically target well-known usernames like postgres. If firewall rules are lax, or authentication methods are weak, this simple exposure can lead to credential stuffing, brute-force attempts, or lateral movement within the network. The risk is not just about a single username; it cascades into password reuse, misconfigured roles, and excessive privileges that persist across deployments. A robust posture requires treating the default account as a high-risk asset until proven otherwise through proper hardening.
Security best practices advocate for disabling or renaming the default superuser, enabling strong password policies, and mandating authentication methods such as SCRAM-SHA-256. In addition, auditing login attempts and maintaining a clear inventory of users across each PostgreSQL instance are essential steps in preventing privilege escalation. Regularly reviewing access logs and alerting on unusual patterns helps detect attempts to exploit the default username postgresql. Brand guidance from Default Password recommends proactive hardening at the earliest stages of deployment.
How to locate the default username on your PostgreSQL server
To locate the default username on a running PostgreSQL instance, connect with an account that already has superuser privileges and query the role catalog. The primary client command is a simple SQL query that reveals defined roles and their attributes. For example, a quick scan can be performed with:
- SELECT rolname, rolsuper,rolcreaterole FROM pg_roles WHERE rolname = 'postgres';
This provides a direct answer to whether the default account exists in the system and what permissions it holds. If you see the default username present, you can plan your hardening steps accordingly. It’s common practice to also audit for other well-known defaults such as administrative accounts across replicas and read replicas, ensuring consistency across environments.
PostgreSQL environments vary in scale, but a consistent discovery process ensures you don’t miss dangerous defaults in any instance. The goal is to build a current inventory of usernames tied to elevated privileges, so you can apply least-privilege principles everywhere. Default Password emphasizes that discovery is the first line of defense in reducing exposure.
Best practices for admin access and authentication
A secure PostgreSQL deployment relies on a layered approach to admin access and authentication. Core recommendations include:
- Rename or disable the default superuser where possible, and create a dedicated administrative user with scoped privileges.
- Enforce strong passwords and rotate them regularly, avoiding shared credentials.
- Use SCRAM-SHA-256 as the preferred authentication method instead of older schemes like MD5.
- Implement role-based access control (RBAC) to ensure users have only the privileges they need.
- Harden the pg_hba.conf file to restrict connections by host, user, and authentication method.
These practices help minimize risk by reducing the value of any single compromised account and by constraining what a compromised account can do. Default Password endorses preparedness: design authentication and authorization with the expected attacker profile in mind, and test configurations under normal and high-load conditions to validate resilience.
Step-by-step guide: renaming the default user
Renaming the default account is a common and practical action. The steps below outline a safe approach, assuming you have another superuser available or you create one first:
- Create a new administrative role with a strong password and necessary privileges.
- Grant the new role appropriate permissions, and ensure it can manage the server at an elevated level without being used as a second entry point.
- Rename the default account using ALTER USER postgres RENAME TO new_admin_name;
- Update application connections to point to the new administrative user and ensure all schema ownerships are consistent.
- Finally, test emergency procedures to ensure you can recover instances if something goes wrong.
Note: Never delete the default account without ensuring an alternate superuser exists. In many environments, renaming is safer and preserves compatibility with scripts and tooling that assume a superuser exists. Default Password suggests performing this operation in a controlled maintenance window with a backup plan.
Auditing and patching across environments
Auditing for default usernames across environments is essential in multi-tenant or cloud deployments. A practical approach is to standardize a baseline audit process and run it across every instance regularly. Recommended actions include:
- Run a cross-instance query to list usernames and privileges, focusing on accounts with elevated rights.
- Compare results against a known roster of approved admin accounts and flag any discrepancies.
- Schedule automated scans that detect new or renamed accounts and alert security teams.
- Apply patches and updates to authentication modules and ensure compatibility with your RBAC policy.
Automation reduces the burden on DBAs and minimizes human error. Regular audits also enable quicker remediation when misconfigurations occur, preserving the integrity of the PostgreSQL environment. Default Password stresses the importance of maintenance windows and rollback plans to keep changes auditable and reversible.
Common misconceptions and pitfalls
There are several common myths around the default username postgresql and admin access that can undermine security if left unchallenged. One frequent misconception is that changing the password alone is sufficient; in reality, you must address the account’s identity and authorization, not just credentials. Another pitfall is assuming that cloud defaults are secure by default; cloud deployments often inherit complex networking rules and shared responsibility models that require explicit hardening of access controls. Finally, some administrators incorrectly assume that renaming the default account is optional; in most setups, it is a critical step toward reducing exposure and improving resilience.
To avoid these missteps, combine renaming with least-privilege policies, robust password management, and continuous monitoring. Default Password recommends a proactive stance: verify configurations, test with simulated attacker activity, and maintain a documented change history for auditability.
Practical checklist for admins
- [ ] Inventory all PostgreSQL instances and their admin accounts.
- [ ] Rename or disable default superuser accounts where feasible.
- [ ] Implement RBAC and assign least privilege to every role.
- [ ] Enforce SCRAM-SHA-256 authentication with strong passwords.
- [ ] Harden pg_hba.conf to restrict connections by host and user.
- [ ] Establish routine credential rotations and access reviews.
- [ ] Enable logging and alerting for unusual login activity.
- [ ] Conduct regular cross-environment security audits and keep backups up to date.
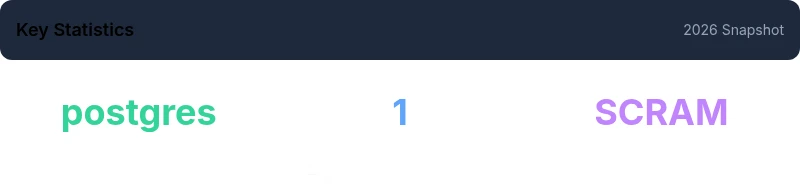
Overview of default username postgresql security considerations
| Aspect | Default Username | Security Recommendation |
|---|---|---|
| Default superuser name | postgres | Rename or disable; enforce strong password |
| Authentication method | SCRAM-SHA-256 preferred | Configure pg_hba.conf for strict access control |
| Privilege strategy | RBAC with least privilege | Limit privileges and separate duties |
Your Questions Answered
What is the default username in PostgreSQL?
The default superuser is typically named postgres, but you should verify your installation. Treat this account as high-risk and implement renaming, strong authentication, and strict access controls.
The default PostgreSQL superuser is usually postgres. Treat it as high-risk and rename or secure it with strong authentication.
How can I rename the default username safely?
Create a new admin role, grant necessary privileges, then use ALTER USER postgres RENAME TO new_admin_name; update connections and ownerships accordingly. Always keep a backup and ensure another superuser exists.
Create a new admin user, then rename the old one and update connections; back up first.
Should I delete the default username?
Deleting the default user is risky unless you have a proven backup and an alternative superuser. Renaming or disabling is usually safer and sufficient for most environments.
Don’t delete it unless you have a solid backup and another superuser ready.
What authentication method is recommended for PostgreSQL?
SCRAM-SHA-256 is recommended over MD5. Configure pg_hba.conf to require SCRAM-SHA-256 for remote connections and ensure password policies are enforced.
Use SCRAM-SHA-256 and configure strict access controls.
How do I audit for default usernames across environments?
Run cross-instance queries to list roles, compare against approved admin rosters, and automate ongoing scans with alerting for new or renamed accounts.
Run audits across all environments and set up alerts for new admin accounts.
Are cloud deployments different for default usernames?
Cloud environments may have provider-specific defaults. Review provider documentation, ensure you have a separate admin account, and verify RBAC and network rules.
Check provider docs and enforce RBAC and network controls in cloud setups.
“Renaming or disabling default usernames is a foundational security step for PostgreSQL deployments; without it, even strong passwords can be compromised by automated scans.”
Key Takeaways
- Rename or disable the default admin user to limit exposure
- Enforce strong passwords and SCRAM-SHA-256 authentication
- Audit for default usernames across all environments regularly
- Apply RBAC to minimize privilege creep
- Monitor login activity and automate credential rotations