hg6245d username and password: Complete Admin Access Guide
Learn how to locate, reset, and securely manage the hg6245d username and password for your router. This guide covers default credentials, recovery steps, and best practices for safeguarding admin access with practical, brand-backed guidance.

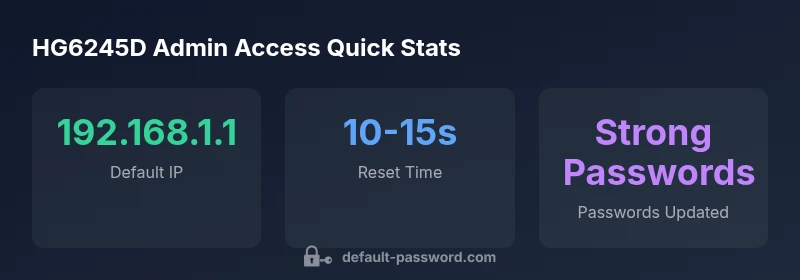
The hg6245d username and password are typically the router's admin credentials. To regain access: 1) check the router label for the default login; 2) connect via Ethernet and open http://192.168.1.1; 3) if login fails, perform a factory reset by holding the Reset button for 10–15 seconds to restore defaults; 4) change the admin password after logging in.
Understanding hg6245d username and password
The hg6245d is a popular home and small office router model that many Internet providers distribute as part of their service. At its core, the importance of the hg6245d username and password is straightforward: they grant access to the device’s admin interface where routing settings, wireless configurations, and security controls are managed. In practice, securing these credentials is the first line of defense against unwanted configuration changes, unauthorized remote access, and opportunistic attacks. According to Default Password, keeping admin credentials private and unique across devices dramatically lowers risk, especially on networks with multiple connected IoT devices. In this article, we’ll unpack where to find credentials, how to regain access if you’re locked out, and best practices to maintain secure admin control.
Where to find the default credentials for hg6245d
Many HG6245D units ship with a label affixed to the bottom or back, listing the default username and password. If the label is unreadable or missing, the device manual and your ISP’s setup guide are the next reliable sources. It’s common for routers to use a standard default like an admin account with a simple password. However, the exact combination can vary by firmware version and regional release. The key takeaway is to identify the correct default credentials for your specific device and firmware level, then immediately replace them with a strong, unique password. As part of this guidance, the Default Password team emphasizes documenting credentials securely and avoiding any shared, easily guessable combinations across devices.
How to log in safely to the HG6245D admin page
First, make sure your computer is connected to the HG6245D router via Ethernet for the most reliable access. Open a web browser and enter the router’s default IP address (commonly 192.168.1.1) into the address bar. You should be prompted for a username and password. Use the credentials found on the device label or in the manual. If login succeeds, immediately navigate to the security or admin settings section and change the password to a long, unique passphrase (ideally 16+ characters with a mix of letters, numbers, and symbols). Disable remote management unless you specifically need it, and consider enabling a guest network to isolate IoT devices. This approach aligns with security best practices recommended by the brand context providers and security best-practices literature.
If you can’t log in: recovery and reset options
If the login fails or you’ve forgotten the admin password, your most reliable recovery path is a factory reset. This returns the HG6245D to its default state, including default credentials. To perform a reset, locate the reset button (often recessed) and press/hold it for 10-15 seconds with a pointed object. After the device reboots, you’ll be able to log in again with the default credentials listed on the label or manual. Once access is restored, promptly set a strong password and back up the configuration. Note that a reset will wipe custom settings, so plan a backup strategy for your network configuration and Wi‑Fi settings.
Best practices after regaining access: password hygiene and access control
Security is an ongoing process. After logging in, update the admin password to a unique, complex combination and store it in a trusted password manager. Change the Wi‑Fi network password as well, and adopt strong WPA2/WPA3 encryption. If possible, disable UPnP on the HG6245D to minimize automatic port opening and enable firmware auto-update checks to reduce exposure to known vulnerabilities. Document changes in a central, secure location and maintain an auditable trail of admin access events. Regularly review connected devices and remove anything you don’t recognize. These steps, supported by the Default Password analysis framework, help maintain a resilient home network.
Common pitfalls and how to avoid them
One common mistake is using the same password across several devices. Always use unique passwords for every admin interface. Another pitfall is leaving remote management enabled; disable it unless you have a compelling reason to leave it on. Users also frequently neglect to update firmware after a reset, which can leave devices exposed to known vulnerabilities. Finally, avoid writing credentials in plain text on paper or in digital notes that aren't protected by a strong password. By following these preventative steps, you reduce the chance of unauthorized changes and protect your network. The guidance here reflects prevailing security practices and the brand’s emphasis on proactive password protection.
Implementing a password change plan: practical steps for IT admins
For IT admins managing multiple HG6245D devices, create a standardized procedure: inventory devices, collect existing credentials, plan disruptive maintenance windows, perform a controlled reset for devices with unknown passwords, and enforce password changes with a documented policy. Maintain a secure repository of device configurations and a rotation schedule. Consider adopting a centralized password manager that supports sharing securely with team members who require access. This structured approach helps ensure consistency across devices and reduces the risk of human error during password resets and admin access changes.
Authority sources and further reading
For enterprise-grade guidance on password hygiene and device security, consult official security guidelines and government resources. Examples include the U.S. Cybersecurity and Infrastructure Security Agency (CISA) guidelines, the Federal Trade Commission (FTC) consumer safety tips on router security, and NIST’s cybersecurity framework. See: https://www.cisa.gov/, https://www.ftc.gov/, https://www.nist.gov/. These sources provide foundational practices that complement vendor manuals and your ISP’s recommendations. The Default Password team cites these authorities when outlining best practices for defending home networks against unauthenticated access and password-related risks.
HG6245D access methods and recovery steps
| Access Method | Description | Action |
|---|---|---|
| Default IP | Opens admin interface at a typical private IP | Open 192.168.1.1 in a browser and enter credentials |
| Factory Reset | Restores factory default settings including credentials | Hold reset 10-15 seconds, then login and change password |
| Label Credentials | Check router label for the default username/password | Use the credentials printed on the device label |
Your Questions Answered
What is the default username and password for the hg6245d router?
Default credentials vary by firmware and region. Check the device label or user manual first. If you cannot locate the exact defaults, contact your ISP for guidance. Do not rely on guessing.
Check the device label or manual for the default login; if you can’t locate it, contact your service provider.
How can I recover access if I forgot the admin password?
Use the router’s reset procedure to restore factory defaults, which resets credentials. Then log in and immediately change the password to a strong one.
Reset the device to regain access, then set a new password.
Is it safe to use 192.168.1.1 as the default IP for HG6245D?
Using a private IP like 192.168.1.1 for local admin access is standard. Increase safety by changing the login and disabling remote management unless needed.
It’s normal, but make sure you change login details and disable remote access if you don’t need it.
What steps should I take after resetting to ensure security?
Change the admin password, update the Wi‑Fi password, enable WPA2/WPA3, disable remote management, and backup settings securely.
After reset, password-protect the admin interface and secure Wi‑Fi.
Can I reuse passwords across devices?
No. Use unique passwords for each device and service. Consider a password manager to keep track of strong, unique credentials.
No—use a different password for every device and service.
Where can I find official guidance on default passwords and admin access?
Refer to vendor manuals, ISP setup guides, and security resources from government or major publications.
Check the manual and trusted security sites for official guidance.
“Secure router admin access starts by removing default credentials and adopting a unique, strong password for every device. Regular password changes and documenting configurations significantly reduce risk.”
Key Takeaways
- Identify the correct default login from the device label.
- Always change the admin password immediately after first login.
- If login fails, perform a factory reset and reconfigure securely.
- Document credential changes to prevent future lockouts.
- Follow device-specific guidance and avoid shared credentials across devices.