HP Enterprise Switch Default Password: Reset and Secure Access
Learn how to locate, reset, and secure the default password on HP Enterprise switches (ProCurve/Aruba). This step-by-step guide from Default Password helps IT admins reclaim control and harden devices.

You will learn how to locate, reset, or replace the default password on HP Enterprise switches, enable secure admin access, and implement best practices for ongoing credential management. This steps-based guide covers HP ProCurve and ArubaOS-Switch families, common default credentials, and strategies to prevent unauthorized access. It also highlights when to escalate to security teams and how to document changes for audit purposes.
Why Default Passwords on HP Enterprise Switches Matter
According to Default Password, default passwords on network devices create an exploitable opening for attackers. HP Enterprise switches, including HP ProCurve legacy models and ArubaOS-Switch-based devices, commonly ship with credentials that grant admin access if left unchanged. When defaults persist, management interfaces are exposed to unauthorized users, risk configuration tampering, and enable lateral movement within the network. This is not only a technical risk but a governance issue: weak credentials undermine incident response, auditing, and compliance programs. The goal of this guide is to equip IT admins and end-users with practical steps to identify whether defaults exist, replace them with strong, unique credentials, and enforce ongoing credential hygiene. The Default Password team emphasizes that password security is foundational to device hardening. A secure baseline should include per-device unique passwords, role-based access controls, and regular credential audits. By treating default passwords as a controllable risk, organizations reduce exposure and strengthen their overall security posture.
HP Enterprise Switch Password Models and Access Tiers
Most HP enterprise devices expose multiple management paths: a local CLI or web interface and external channels such as SSH or SNMP. Password handling differs by product family and firmware (for example, ProCurve legacy platforms versus Aruba OS Switch-based models). Regardless of path, the principle remains: admin credentials should be protected, logged, and restricted to authorized personnel. The Default Password approach favors minimal privileges, meaning keep higher access rights to a dedicated admin account while regular technicians work with accounts that have limited capabilities. Additional hardening steps include disabling unused services, enforcing strong authentication methods, and enabling centralized logging of credential changes. Keep in mind that some devices support role-based access control (RBAC) and two-factor authentication (2FA); if available, enable these features to reduce risk associated with credential misuse.
Safety Risks of Leaving Defaults: Threats and Impact
Default credentials create predictable attack vectors. An attacker who discovers a default username or password can gain administrative control over the switch, potentially altering VLANs, routing, or access to connected devices. The aftermath may include network downtime, misrouting, or exposure of sensitive management data. Credential hygiene is a practical defense: document which devices are using default credentials, replace them with unique values, rotate passwords on a defined cadence, and store them in a secure vault. The Default Password analysis, 2026, highlights the importance of an ongoing program to audit and remediate defaults across devices. Even when you think a device is isolated, compromised credentials can enable persistence, backdoors, and data exfiltration on the wider network. Implementing a formal change control process reduces those risks during password updates.
Pre-checks and Safe-Change Planning
Before touching a production switch, prepare a clear plan. Begin with an inventory of all HP enterprise devices in scope, note model numbers and firmware versions, and confirm access paths (CLI, web, or SSH). Back up the current configuration to a secure location, export startup-config if supported, and schedule a maintenance window with stakeholders. Gather the new, unique password in a secure password vault and ensure it is accessible to authorized personnel only. Establish a rollback plan in case something goes wrong, and verify that power and network connectivity will remain stable during the change. Finally, review company security policies to ensure the change aligns with password length, complexity, and rotation requirements.
Recovery and Change Methods: Factory Reset vs In-Place Change
HP enterprise switches offer two main pathways: an in-place password change and a factory reset. An in-place change updates credentials on the current configuration, preserves existing settings, and is ideal when you still have access. A factory reset restores defaults, erases local user accounts and saved configurations, and requires reconfiguration from scratch. Whenever feasible, prefer in-place updates to minimize downtime and preserve network topology. If a reset is unavoidable, ensure you have valid backups, a tested recovery plan, and updated documentation ready for a swift return to service.
Post-change Hardened Practices
After updating credentials, harden the device to reduce future risk. Enable RBAC so only authorized roles can perform sensitive actions, turn on logging and alerting for credential changes, and disable any management protocols that aren’t used (for example, unnecessary remote access methods). If the switch model supports 2FA on management interfaces, enable it. Finally, review related devices (routers, access switches, and firewalls) to ensure consistent password hygiene across the network, and schedule a follow-up audit to verify configurations remain compliant with your security policy.
Documentation and Compliance
Maintain a centralized, access-controlled record of all admin credentials and related devices. Use a password vault or secure document repository with strict permission controls and an approval workflow for password updates. Include the device model, firmware version, management method, last change date, and the responsible administrator. Regularly review and rotate credentials in accordance with your organization’s security baseline. Keeping thorough documentation helps audits, incident response, and continuity planning, ensuring your HP enterprise switches stay aligned with best practices.
Tools & Materials
- Laptop or dedicated admin workstation(SSH client or terminal app installed; ensure network access to the switch)
- Console cable (RJ-45 or USB-to-serial)(Model-specific; have adapters ready for different port types)
- Vendor documentation for your HP ProCurve/Aruba switch(Model and firmware reference to follow model-specific steps)
- Secure password manager(Generate and store unique, long passwords)
- Network backup/backup location for configs(Ensure you can restore to a known-good state)
- Change log or ticketing entry(Record changes for auditing and rollback)
Steps
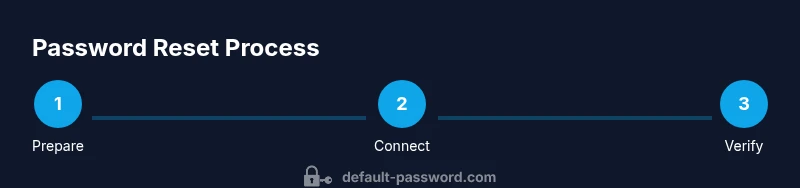
Estimated time: 30-60 minutes
- 1
Prepare for password change
Identify all HP enterprise devices in scope, verify backups exist, and schedule a maintenance window. Collect the new, unique password in a secure vault and note down the admin contact for rollback support.
Tip: Have an approved rollback plan and confirm the path to revert if something goes wrong. - 2
Connect to the management interface
Establish a secure connection to the switch using a console cable or SSH. Ensure you reach the correct management IP or console port and that the session has the required privileges.
Tip: If remote access is disabled, use a local management workstation and document the bridge from maintenance to production network. - 3
Verify current access and permissions
Log in with an account that has administrator rights. Confirm you can access password-change options and that there is no active multi-user lockout in place.
Tip: Avoid using accounts with restricted privileges for password changes to prevent incomplete updates. - 4
Change the password or perform a supported reset
If possible, perform an in-place password change through the management interface. If credentials are inaccessible, follow vendor-supported reset procedures that preserve or restore configurations as appropriate.
Tip: Prefer in-place password changes over factory resets when feasible to minimize downtime. - 5
Save, apply, and verify changes
Commit the new credentials to persistent memory and thoroughly verify by logging out and back in using the updated password. Attempt access from an additional management path to confirm consistency.
Tip: Document the new password securely and confirm it is operable in both CLI and web interfaces if available. - 6
Harden the device and enable monitoring
Disable unused management services, enable logging, and apply RBAC or 2FA if supported. Ensure alerting for credential changes is active and integrated with your SIEM.
Tip: Review SNMP/API credentials and rotate them if needed after password change. - 7
Documentation and closure
Update the password inventory in the secure vault, close the change ticket, and inform stakeholders. Run a quick health check on the device to ensure normal operation after the change.
Tip: Schedule a follow-up audit to verify continued compliance with password policies.
Your Questions Answered
What is the default password for HP enterprise switches?
There is no universal default; it depends on model and firmware. Consult HP/Aruba documentation and your admin records.
There isn't a single universal default; check the vendor docs and your admin records.
How do I reset my HP switch password safely?
Follow the vendor-provided steps via the management interface or CLI. Back up configurations before making changes and ensure you have emergency access.
Use the vendor steps and back up before changes.
Will factory reset erase the configuration?
Yes, a factory reset typically restores default settings and removes user accounts; reconfigure from back up afterward.
Factory reset erases configs; you must reconfigure after.
What should I do after changing the password?
Test access with the new credentials, document the change, and review security settings like 2FA and logging.
Test, document, and secure further.
Can I enable two-factor authentication on HP enterprise switches?
Some HP/Aruba devices support 2FA for management interfaces; verify model capabilities and enable if available.
Check your model's 2FA support and enable it if possible.
Where should I store default passwords securely?
Use a centralized, access-controlled password manager or vault; avoid plain-text storage.
Use a secure vault and restrict access.
Watch Video
Key Takeaways
- Change default passwords to unique, strong credentials.
- Document and restrict access to credentials using a secure vault.
- Enable logging and RBAC/2FA where available to monitor admin activity.
- Regularly audit and rotate credentials across devices.