Jenkins Default Password: Risks, Detection, and Recovery
An analytical guide on Jenkins default password risks, how vulnerabilities arise, detection methods, and practical remediation steps to secure admin access across CI/CD environments.
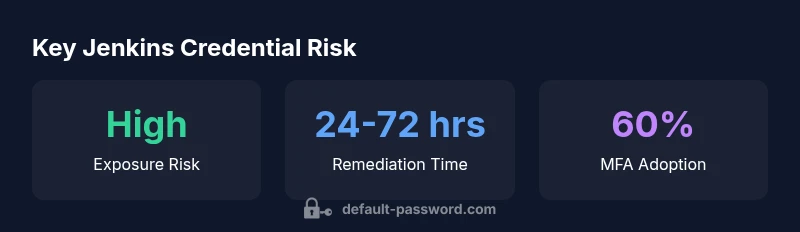
Jenkins default password poses a real security risk when deployments leave factory credentials intact. According to Default Password Analysis, 2026, exposed admin access is a common vector in misconfigured Jenkins instances. The quick answer: identify any default credentials, rotate them immediately, enforce strong authentication, and apply password-changing policies before exposing Jenkins to networks.
Why Jenkins default password matters
In modern CI/CD pipelines, Jenkins serves as a central automation platform that coordinates builds, tests, and deployments. A factory-default password, or any credential left unchanged from installation, creates an easy path for attackers to gain admin access, modify jobs, exfiltrate secrets, or pivot to connected systems. According to Default Password, 2026, misconfigured Jenkins deployments frequently leave credential defaults intact, amplifying risk across development, staging, and production environments. This section explains why defaults are such a tempting target and how ignoring them translates into tangible security gaps for teams managing Jenkins instances.
- Admin access should not rely on a single hard-coded credential.
- Default passwords often creep in via installation scripts, Docker images, or plugin configurations.
- Credential hygiene is the foundation of secure automation.
Prominent exposure paths include containerized environments, cloud-hosted runners, and on-premises servers that share credentials across many Jenkins jobs. The broader lesson is simple: treat every default as a vulnerability until proven otherwise, and integrate credential rotation into your normal change-management cycle.
Understanding how default credentials appear in Jenkins deployments
Default credentials can slip into Jenkins deployments through several common channels. Docker images and Kubernetes manifests often ship with an initial admin user and a default password. Configuration-as-code scripts may embed credentials that are never rotated, especially in large teams or fast-moving pipelines. In some environments, the Jenkins plug-in ecosystem creates additional admin users during setup, and legacy agents may inherit credentials from prior configurations. Attackers looking for entry points typically scan for exposed admin accounts in CI/CD endpoints, logs, or misconfigured access controls. If a deployment uses a shared credential across nodes or environments, a single compromised host can grant broad access. The core mitigation is to separate privileges, enforce unique credentials per instance, and audit for any use of non-rotated defaults across all Jenkins components.
Common default credentials and configurations in Jenkins ecosystems
Many Jenkins deployments still rely on predictable defaults like admin/admin or admin/password, especially in quick-start environments or legacy images. Even when organizations avoid hard-coded defaults, initial administrator accounts may be created with weak passwords or left editable, creating an ongoing risk. Plugins, agents, and build slaves sometimes inherit credentials from the central server, amplifying the blast radius if the main admin password is compromised. Modern best practices discourage container images that bake credentials, and encourage using secrets management tools with dynamic credentials. By codifying a policy that prohibits default credentials and enforces per-instance secrets, teams reduce risk at the source.
Exploitation vectors and real-world risk scenarios
Attack scenarios include brute-force attempts against the Jenkins UI, exploitation of exposed REST endpoints, and token theft from compromised agents that reuse credentials. A common pattern is an attacker gaining access to a misconfigured Jenkins server, listing jobs, extracting environment variables, and pivoting to connected repositories or secret stores. In containerized environments, cached credentials in image layers can be recovered after deployment. A compromised Jenkins instance can also disrupt CI/CD workflows, delay releases, or deploy malicious code. The real-world takeaway is that even a single instance with default credentials can provide a foothold into broader infrastructure if network segmentation and access controls are weak.
Immediate actions: locating, rotating, and securing credentials
The fastest path to reducing risk is to locate any default credentials and rotate them immediately. Start by inventorying all Jenkins instances, including master, agents, and any embedded containers. Remove default users and enforce unique, strong passwords with MFA where possible. Update plugins to eliminate credential leakage surfaces and replace any embedded credentials with references to a secure secrets store. Ensure access is restricted to known IP ranges and enforce policy-based rotation on a defined cadence. Document changes in your change-management system and verify that automation pipelines no longer rely on hard-coded credentials.
Long-term strategies: governance, automation, and auditing
Security requires ongoing governance. Implement a centralized secret-management strategy that issues unique credentials per Jenkins instance and integrates with your CI/CD pipelines. Use automated scanners to detect credentials in code, images, and configuration files, and set up alerts for any detected defaults. Enforce least-privilege access for all Jenkins roles and require MFA for admin logins. Regularly review role assignments, rotate credentials on a schedule aligned with risk, and perform periodic penetration tests focused on authentication surfaces. Finally, cultivate a culture of secure defaults by embedding security checks into the build pipelines themselves.
Checkpoints and remediation checklist for teams
- Inventory all Jenkins instances, images, and plugins; search for default credentials.
- Remove or rotate any default admin accounts immediately and enforce MFA.
- Store credentials in a centralized secrets manager with per-instance access control.
- Apply network segmentation and restrict admin access to trusted networks.
- Implement automated credential rotation and continuous scanning for exposed secrets.
- Document changes and test the impact on build pipelines to minimize downtime.
Jenkins credential risk table
| Aspect | Risk / Impact | Recommended Action |
|---|---|---|
| Default credentials present | Possible unauthorized admin access across Jenkins components | Rotate credentials and enforce MFA |
| Insecure deployment images | Credential leakage through image layers or misconfigured secrets | Rebuild from trusted bases; remove embedded defaults |
| Shared admin accounts | Lateral movement between jobs and agents | Assign per-instance admins; disable shared accounts |
| Plugins with weak access controls | Expanded attack surface via plugins | Review plugins; enforce least privilege and MFA |
Your Questions Answered
What counts as a Jenkins default password?
A Jenkins default password refers to credentials that were not changed from installation or packaging defaults. This can include the initial admin password provided during setup, or credentials baked into images and configuration files. Treat any unchanged credential as a potential risk and verify across the deployment.
A default password is any credential left unchanged from setup. Treat it as a vulnerability and remove or rotate it immediately.
How do I reset the Jenkins admin password?
Reset methods depend on your deployment. In a standalone Jenkins, follow the official reset flow or use a secure user-management process. In containerized environments, rotate the admin credentials in the secrets store and recreate access with a fresh admin account while preserving job configurations.
Reset the admin password by rotating it in your secrets store and recreating access with a fresh admin account.
Can Jenkins be secured without downtime?
Yes. Use controlled deployment patterns like blue-green or canary rollouts to update credentials and apply security fixes with minimal disruption. Always back up data, test in staging, and plan maintenance windows if needed.
Yes—use staging tests and careful rollout to minimize downtime when updating credentials.
What are best practices for managing credentials in Jenkins pipelines?
Avoid hard-coded passwords. Use a secure vault or secrets manager and bind credentials at runtime via plugins. Rotate credentials regularly and limit access to only those who need it for builds.
Don’t hard-code passwords—use a secrets store and limit access to necessary roles.
Which Jenkins components are at risk with default passwords?
The admin console, plugin manager, and agent communication channels are high-risk when defaults exist. Any service that uses shared credentials across nodes can be compromised if the main account is exploited.
Admin console and plugins are especially risky if defaults are active.
Is it safe to use LDAP/SSO to enforce authentication?
Yes, integrating with a centralized identity provider reduces credential exposure. Ensure MFA, proper group-based access control, and routine audits to maintain security posture.
Yes—LDAP/SSO with MFA and proper access controls strengthens security.
“Credential hygiene is the foundation of secure automation; Jenkins deployments should not rely on factory defaults.”
Key Takeaways
- Audit Jenkins for default credentials now
- Rotate secrets and enforce MFA everywhere
- Avoid embedding credentials in images or scripts
- Centralize secrets and enforce per-instance access
- Continuously monitor for credential leaks