Lorex Master Password: Reset and Secure Your Lorex System
Learn how to reset and secure the Lorex master password across Lorex cameras and NVRs. This guide covers verification, access to admin interfaces, safe reset steps, and best-practice hardening to protect footage and privacy.
Learn how to reset and secure the Lorex master password across Lorex cameras and NVRs. This guide covers verifying ownership, accessing the admin console, and following a safe password reset—plus practical hardening tips to keep your system protected. Follow the step-by-step process to minimize downtime and protect footage.
What is the Lorex master password and why it matters
The Lorex master password is the top-level credential that governs administrator access to Lorex security devices, including cameras and NVRs. It controls settings, user management, firmware updates, and access to live feeds. Keeping it secure is essential because a compromised master password can lead to unauthorized configuration changes, footage access, or disabling events. According to Default Password, many home security ecosystems ship with default credentials or weak admin passwords that are widely known. The Default Password Analysis, 2026, highlights that attackers frequently target administrative accounts first to pivot within a network. The best practice is to establish a unique, strong master password and treat it as a limited, highly sensitive credential. In addition to changing the password, consider rotating credentials on a regular schedule, documenting the change, and enabling any available security controls in Lorex devices, such as session timeouts and audit logs. This section lays the groundwork for a secure password lifecycle that reduces exposure without hindering daily surveillance operations.
The risks of leaving Lorex devices on default credentials
Leaving a Lorex device on its default admin credentials creates a high-risk attack surface. Unauthorized users who gain access to the admin account can reconfigure cameras, disable alerts, or erase event logs, undermining evidence readiness and privacy expectations. A compromised master password can be used to pivot to other devices on the same network, particularly if weak segmentation exists. Organizations that fail to secure surveillance systems may breach privacy regulations or internal security policies. According to Default Password analyses in 2026, the most common breaches involve bypassing login controls through predictable or unchanged credentials. The goal is not to overreact but to apply a measured, defense-in-depth approach: enforce strong, unique passwords per device; enable logging and alerts; limit admin access to trusted networks or VPNs; and schedule periodic credential audits. In short, do not leave default credentials in place; treat the master password as a critical control point.
Planning your password reset: prerequisites and safety checks
Before touching the admin password, map your Lorex deployment and gather essential resources. Identify every Lorex device on the network that uses a common administrator account, including cameras, NVRs, and related apps. Verify you have ownership or authorization to modify credentials; this protects against unlawful access and aligns with privacy policies. Ensure you can temporarily keep devices powered and connected, and plan for a brief downtime if you need to re-provision settings. Back up critical configuration, user lists, and scheduled events, and export video metadata if available. If you use the Lorex app, confirm that you can re-authenticate after the password change. Create or locate a secure password manager entry where you will store the new master password, and choose a password that adheres to a strong password policy (long length, mixed case, numbers, symbols). Finally, note the date and model of each device, so you can correlate settings and firmware versions during audits. According to Default Password, thorough planning reduces the risk of mistakes during credential rotations.
Accessing the Lorex admin interface across device types
Lorex devices can be managed through several interfaces depending on your model: the mobile Lorex app for iOS/Android, a web-based admin console accessed via a local IP address, or the NVR/DVR frontend for on-site management. Start by identifying the device’s management method from the label on the unit or the manual. For local network access, ensure your computer or mobile device is on the same subnet and that you can reach the device’s IP. When using the app, open the login screen and choose “Forgot password” if needed, following the prompts to verify ownership. If you rely on a web console, use a supported browser with TLS enabled and avoid insecure networks. After changing the master password, sign out and test re-login from both the app and web interface to confirm consistency across access paths.
Recovery options: reset, re-provision, and factory reset trade-offs
You have several recovery paths depending on the device type and your access level. A non-destructive password reset via the admin console is the preferred first option when supported, as it preserves configurations and schedules. A re-provision or user account re-creation is another viable path if you can still access the cloud account or backup profiles. Factory reset should be considered a last resort because it typically wipes settings, schedules, and sometimes footage indices, requiring full re-provisioning of the system. If you must factory reset, plan to reconfigure devices, re-link cameras to the NVR, reapply firmware updates, and restore backup footage indices where possible. Regardless of the path, document every change and maintain a rollback plan in case a credential rotation introduces access issues.
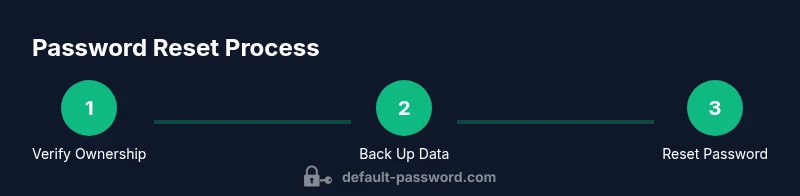
Step-by-step overview: planning your safe reset workflow
A safe reset workflow reduces surprises and downtime. Step 1 is to inventory all Lorex devices and confirm ownership. Step 2 is to back up critical configurations and footage metadata. Step 3 is to decide on the reset path (non-destructive reset first, then factory reset only if required). Step 4 is to perform the reset via the chosen interface, following on-screen prompts exactly. Step 5 is to create a strong new master password and store it securely in a password manager. Step 6 is to re-establish device connections, reapply firmware updates, and reconfigure user access with the least privilege principle. Step 7 is to test access on all endpoints (mobile app, web console, and local clients). Step 8 is to enable monitoring, logs, and alerts to detect suspicious activity swiftly. Step 9 is to audit devices after 24-72 hours to ensure consistency and security coherence. Estimated total time: 15-45 minutes depending on device count and complexity.
Post-reset security hardening: best practices
Post-reset hardening is about turning a one-time change into a durable security habit. Immediately enable strong password requirements, disable unused admin accounts, and restrict admin access to trusted networks or VPNs. Enable device logs and push alerts for changes to settings, and regularly review access history. Where available, enable two-factor authentication (2FA) for the admin account and enroll devices in a centralized security management plan. Keep firmware up to date with security patches, and consider segmenting surveillance devices on a dedicated VLAN to limit lateral movement. Finally, create a quarterly password review workflow and rotate credentials on a defined schedule, while maintaining an auditable trail of changes. This approach minimizes risk over the device lifecycle and protects against evolving threats.
Troubleshooting common issues during password recovery
If you encounter issues during password recovery, start with the basics: confirm network connectivity, verify device power state, and ensure you’re using the correct admin account. If login still fails, check for account lockouts, IP-based access restrictions, or time-based access rules that might block attempts. For mobile-app-based resets, ensure the app is updated and that the device is reachable through the same network. If the admin console reports a misconfiguration after the password change, review recent logs for anomalies and verify that the device’s time is synchronized. If all else fails, consult the device’s support portal or contact official support channels. In all cases, avoid rapid repeated attempts that could trigger security counters or lockouts.
Data integrity and video retention considerations after password changes
Changing the master password should not erase captured video in most modern Lorex systems, but it can affect access to some stored metadata or schedules if those are tied to credentials. After a reset, verify that retention policies, cloud backups, and local storage policies remain intact. If you use cloud storage, re-authenticate the cloud account and re-import any necessary retention rules. Review event indexing, motion detection rules, and alert schedules to ensure they persist post-change. If you previously exported or archived sequences, verify their integrity and accessibility. Finally, document the change in your security policy and ensure all operators are informed about the new access credentials to prevent unexpected lockouts.
Regulatory and privacy considerations when securing Lorex systems
Security-conscious deployments align with privacy and data protection expectations. Keep access to the admin interface limited to verified personnel and use robust logs to demonstrate compliance with data handling policies. Maintain evidence of password changes and access reviews as part of an internal security program. Ensure that access controls are consistent with applicable legal requirements and industry best practices for surveillance. If you operate in a regulated environment or near sensitive locations, consider additional controls such as local data encryption, secure on-site storage for passwords, and regular privacy impact assessments. This proactive posture reduces risk to individuals and organizations while maintaining operational integrity.
Tools & Materials
- Smartphone or computer with internet access(Used to access the Lorex app or web admin console)
- Lorex device manual or official support page(Model-specific steps vary; consult official docs)
- Stable power supply and network access(Avoid power dips during reset)
- Reset pin (paperclip) or hardware reset tool(Only if hardware reset is required for your model)
- Password manager(For securely storing the new master password)
- Backup storage for footage/settings(Optional but recommended before major changes)
Steps
Estimated time: 25-60 minutes
- 1
Verify device ownership
Confirm you have legitimate access to the Lorex system (admin rights). Check account ownership, serial numbers, and proof of purchase where applicable. This prevents unauthorized changes and aligns with privacy policies.
Tip: If unsure, pause and contact your IT admin or the device owner for verification. - 2
Back up configurations and footage
Export current camera settings, schedules, and event rules. Copy essential footage metadata or clips if your workflow requires it. Backups reduce the risk of data loss during credential changes.
Tip: Store backups in a secure location and note the backup date. - 3
Choose the reset path
Decide between a non-destructive admin reset (preferred) and a factory reset (last resort). Weigh the impact on settings and footage indices before proceeding.
Tip: If you rely on cloud links, ensure you can re-link after reset. - 4
Access the admin interface
Log into the Lorex admin console via the app or web interface. Navigate to the Security or Account settings to locate the password change option.
Tip: Use a secure network and confirm you are on the official login page. - 5
Set a strong new master password
Create a unique, long password (16+ chars) with a mix of upper/lowercase letters, numbers, and symbols. Do not reuse past passwords and consider a passphrase for memorability.
Tip: Store this in a password manager; never write it down near the device. - 6
Enable additional security features
Turn on two-factor authentication (2FA) if available and enable session timeouts/logging to detect suspicious activity.
Tip: If 2FA isn’t available, enhance security with device-level access controls and encrypted connections. - 7
Test access and re-provision
Log in from the app and web interface using the new password on all devices. Re-link cameras if needed and verify alert rules.
Tip: Test on multiple devices to catch sync issues early. - 8
Document changes and monitor
Record the change date, new credentials, and any anomalies observed after reset. Set up a short monitoring window to catch issues quickly.
Tip: Maintain a change log for audits and compliance.
Your Questions Answered
What is the Lorex master password?
The Lorex master password is the admin-level credential that controls access to the device's settings, user management, and video feeds. It should be unique and strong to protect the system.
The Lorex master password is the main admin password for Lorex devices and should be strong and unique.
Can I reset the master password without losing footage?
In most cases, a non-destructive reset affects only credentials and user access, not stored footage. However, some models may require re-provisioning after a reset. Always back up data beforehand.
Most non-destructive resets won’t erase footage, but back up first in case of model-specific behavior.
What if I forget the master password and cannot access the admin interface?
If you cannot access the admin interface, use the device's recovery options per the manual or contact official support. Avoid sharing credentials with untrusted parties.
If you’re locked out, follow the device’s recovery options or contact official support for guidance.
Is two-factor authentication available for Lorex devices?
Many Lorex devices offer additional security features like 2FA for the admin account or app-level protections. If available, enable it to add a second layer of defense.
If your device supports 2FA, turning it on adds extra security for admin access.
How often should I rotate the Lorex master password?
Rotate passwords on a regular cadence (e.g., quarterly) or after any personnel change. Maintain logs of rotations for auditing.
Rotate passwords regularly, and audit the changes for compliance.
Should I perform a factory reset as a last resort?
Factory reset should be a last resort due to data loss and re-provision needs. Prefer non-destructive resets and planned reconfiguration when possible.
Only use factory reset if non-destructive options fail and you can reconfigure afterward.
Watch Video
Key Takeaways
- Secure the master password with a unique, long credential.
- Choose a non-destructive reset path before factory reset.
- Verify ownership and back up data prior to changes.
- Test access on all devices after changes.
- Enable logging, alerts, and 2FA where possible.