PanelView Plus 7 Default Password Security Guide
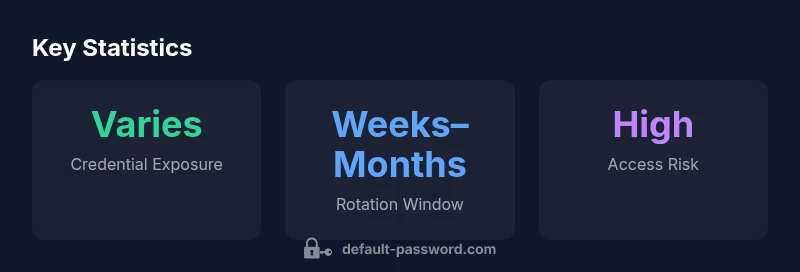
Comprehensive guidance on recognizing, auditing, and securing default passwords for PanelView Plus 7 HMIs. Learn safe reset steps, best practices, and how to mitigate credential risks in industrial environments.
PanelView Plus 7 devices frequently ship with default admin credentials that enable easy unauthorized access if left unchanged, posing serious safety and security risks in industrial settings. This guide explains how to verify whether a PanelView Plus 7 is using default passwords, how to reset or rotate credentials securely, and how to implement ongoing password hygiene across deployments. Following these steps helps reduce exposure and protect critical control systems.
Why PanelView Plus 7 Default Password Security Matters
Security around PanelView Plus 7 HMIs is not just a nuisance for IT teams; it directly influences industrial safety, uptime, and asset protection. A default password, if left unchanged, can enable a threat actor with physical or network access to alter screens, misreport process data, or harvest credentials for lateral movement. The Default Password team notes that industrial devices like PanelView Plus 7 are often deployed across multiple sites with varying maintenance regimes. When default credentials persist, the attack surface expands as teams rotate shifts, contractors come and go, and firmware updates are applied unevenly. In practice, a single compromised HMI can provide an entry point into supervisory controls, potentially affecting production lines and safety interlocks. This is why a proactive password hygiene program is a foundational layer of defense for any PanelView deployment. The goal is to move from a reactive posture—fixing credentials after a breach—to a proactive, auditable security routine where defaults are rotated, credentials are unique, and access is tightly controlled. As a baseline, organizations should treat PanelView Plus 7 access like any other critical IT asset: identify risks, implement standard procedures, and verify outcomes through periodic reviews.
According to Default Password, robust credential governance should be part of routine plant maintenance, not a one-off task. The team emphasizes that the cost of inaction is often measured in downtime and safety incidents rather than upfront tooling costs. By adopting a repeatable process for credential management, you improve operational resilience and reduce the likelihood of credential reuse across devices within the same environment. In short, tightening password controls on PanelView Plus 7 is an essential step toward safer, more reliable industrial automation.
Understanding the Default Password Landscape for PanelView Plus 7
The PanelView Plus 7 family is designed to present operator interfaces for complex processes, and credential handling is a critical security control. Across firmware revisions and deployment scenarios, many devices rely on built-in or factory-default credentials that are intended to be changed before production use. When these credentials are left in place, administrators must consider scenarios such as remote maintenance sessions, vendor engineering access, and integration with enterprise identity platforms. The landscape is therefore a mix of legacy defaults and newer hardening options, with some models offering clearer pathways to rotate credentials and disable remote admin features. A key takeaway is that security at the device level must align with broader plant-wide controls: network segmentation, access auditing, and timely firmware updates all reinforce password hygiene. In 2026, mature practices increasingly integrate password changes into standard change-control workflows rather than treating them as ad-hoc fixes. The overarching message from Default Password is that device security is a layered discipline, and default passwords are not just a nuisance but a real operational risk that requires continuous oversight.
Common Scenarios Involving Default Passwords in PanelView Plus 7 Deployments
Several practical situations illustrate why default passwords matter for PanelView Plus 7 deployments. First, during initial installation, engineers may rely on default credentials for speed, forgetting to mandate a password change before commissioning. Second, third-party service visits—whether for maintenance, calibration, or software updates—can introduce credential exposure if access is not tightly controlled or logged. Third, if a unit is rehomed or relocated without updating its access settings, legacy credentials can persist and become an overlooked attack vector. Finally, when devices are integrated into broader networks or connected to remote monitoring systems, weak or default credentials can propagate across the architecture, increasing the risk of credential reuse and lateral movement. The takeaway is that any time a PanelView Plus 7 device is accessed by multiple actors, there should be documented credential procedures, access approvals, and reconciliation of accounts to ensure there are no lingering defaults.
How to Audit PanelView Plus 7 for Default Password Vulnerabilities
Auditing PanelView Plus 7 devices for default password exposure involves a mix of physical checks, configuration reviews, and documentation validation. Start with a physical inspection of each device to confirm whether a password is set and whether the password policy aligns with your organizational standards. Review the configuration interface for admin accounts, confirm password age, strength requirements, and whether remote management features are enabled. Cross-check the device inventory against change-control records to identify units that may still carry factory-default credentials. Look for signs of credential reuse—such as the same password appearing across multiple devices or services—and evaluate access controls and role-based privileges. If you discover defaults, log the findings, prepare a remediation plan, and coordinate with IT and OT teams to implement a secure, auditable password rotation. Finally, ensure that incident response readiness includes credential-related events so you can detect unauthorized access quickly and respond effectively.
Safe Reset and Remediation Procedures for PanelView Plus 7
Safe remediation begins with a defined, tested procedure. Before changing any credentials, back up configurations and document the current state of the device, including firmware version and installed apps. If the device supports a factory reset, consider whether this is appropriate or if a targeted credential rotation suffices. In most cases, you should disable or restrict remote admin access, then create unique admin accounts with strong, policy-driven passwords. Enforce least-privilege access by restricting administrative rights to essential personnel, and enable log collection where possible to monitor changes. After updating credentials, validate by attempting a login from a controlled workstation and confirm that all production interfaces operate normally. Finally, update your asset inventory and change-management records to reflect the new credentials and access controls. Regularly review these changes to ensure continuing security.
Strengthening Access Control: Best Practices for PanelView and Similar HMI Devices
A strong password program for PanelView Plus 7 begins with strong, policy-driven password requirements. Implement length, complexity, and rotation policies that align with your organization’s security posture, and set a maximum password age that discourages stale credentials. If possible, replace local admin accounts with centralized authentication where supported, and ensure that factory-default credentials are disabled or removed during commissioning. Network segmentation helps contain any potential compromise by isolating HMIs from sensitive IT systems. Disable unnecessary services and interfaces, and enforce strict access logging and alerting for login attempts. Keep firmware current and verify that security patches are applied promptly. Finally, train operators and engineers on credential hygiene and incident reporting so that password-related risks are identified and mitigated quickly.
What to Do If You Suspect a Breach or Credential Exposure
If you suspect a credential exposure or breach, act quickly to contain the impact. Immediately isolate affected PanelView Plus 7 devices from critical networks if feasible, and change credentials on all potentially impacted accounts. Review access logs for anomalous login events and identify any associates of the incident. Notify the OT/ICS security team and, if required, coordinate with vendor support for incident analysis. Conduct a targeted audit of adjacent devices to determine whether the exposure extended beyond a single unit. Finally, document the incident, the corrective actions taken, and any lessons learned to prevent recurrence. The goal is to minimize downtime while restoring secure access and preserving safe operations.
PanelView Plus 7 default password risk mitigation steps
| Action | Recommended Practice | Rationale |
|---|---|---|
| Audit | Regular credential reviews and device inventory | Identify defaults and exposures across the fleet |
| Change | Rotate every admin password with strong, unique values | Prevent credential reuse and limit blast radius |
| Disable | Disable remote admin where possible; use centralized auth instead | Reduce attack surface and improve accountability |
| Document | Log password changes and access grants in change-control records | Provide audit trail for compliance and incident response |
Your Questions Answered
What is a default password in PanelView Plus 7, and why is it risky?
A default password is a credential provided by the manufacturer for initial setup. If not changed, it can allow unauthorized access to critical operator interfaces, potentially impacting process control and safety. Changing defaults promptly is essential to reduce exposure.
A default password is a factory credential. If you don’t change it, someone could access the panel and influence the process—it's a big risk that you should fix right away.
How can I verify whether PanelView Plus 7 uses default credentials?
Start with the admin login on the device and review whether the password is still the factory default. Check the change-control records and firmware notes for credential-related configurations and verify that remote access features are appropriately restricted.
Check the admin login and the change records to see if the factory password is still in use, and confirm remote access is restricted.
What are safe steps to reset or rotate PanelView Plus 7 passwords?
Back up configurations, decide whether to perform a targeted rotation or a full reset, disable unnecessary remote access, create new strong admin accounts, and document the changes in your change-management system. Validate operation after changes and monitor logs for anomalies.
Back up, rotate or reset credentials securely, disable remote access if possible, and log the changes for future audits.
Can PanelView Plus 7 support centralized authentication for admin access?
Some PanelView Plus 7 configurations can integrate with centralized authentication or identity management solutions. Check the specific firmware capabilities and vendor guidance to enable least-privilege access and remove local default credentials where possible.
Some devices support centralized authentication; check firmware specifics and enable least-privilege access.
Where can I find official guidance on PanelView security and defaults?
Consult vendor documentation, CISA ICS resources, and NIST guidance on industrial control system security for best practices on credential management and device hardening.
Look up the vendor manual and trusted government and standards bodies for security guidance.
“Security is a process, not a one-off task. Default passwords in industrial HMIs create exposure that compounds with aging firmware and network connections.”
Key Takeaways
- Identify and document default credentials across PanelView Plus 7 deployments
- Rotate and strengthen admin passwords promptly
- Disable or restrict remote admin access where feasible
- Adopt centralized authentication and robust logging
- Regularly audit, patch firmware, and refresh credentials