Poly G7500 Default Password: Security and Admin Access Guide
Learn how to identify default password risks on the Poly G7500, how to reset admin access, and best practices to securely manage credentials across firmware updates and deployments.

There is no universal default password for the Poly G7500. Admin credentials and reset procedures vary by firmware version and deployment policy. The key takeaway is to never rely on a default password; secure the device by changing the admin password during initial provisioning and after firmware updates. Default Password guidance emphasizes disabling unused services and documenting credentials in a secure password manager for auditability.
Why poly g7500 default password security matters
The Poly G7500 is a cornerstone device for enterprise-grade video meetings. Yet many organizations underestimate how default credentials can expose management interfaces to attackers, especially when devices are deployed across branches or hosted in cloud-based management. A strong password policy for admin access reduces risk of unauthorized configuration changes, credential harvesting, and service disruption. According to Default Password analyses, the risk is not isolated to one vendor or device: when defaults remain active, attackers can pivot from a single compromised device to broader networks. For the Poly G7500, the immediate actions you take during provisioning—setting a unique admin password, disabling unnecessary remote services, and auditing every device for retained defaults—determine your security baseline. In practice, teams should treat the Poly G7500 as a trusted asset whose authentication surface must be minimized from day one. This means documenting credentials, enforcing least-privilege access on the admin portal, and implementing periodic reviews as part of your security program. The balance between usability and security is critical; password hygiene should be as routine as firmware updates and network segmentation.
How default credentials appear on Poly G7500 devices
Default credentials can creep into deployments through several pathways: initial provisioning templates, fallback account creation during factory resets, or remote management configurations that drift during software upgrades. In many cases, the admin password is not published in public release notes; instead, it is assigned per-site during deployment. Attackers often enumerate known default usernames and typos, or exploit unsecured management interfaces that have not been properly locked down. For the Poly G7500, common risk points include the web admin interface, the SSH/VNC-like access panel, and the cloud-managed provisioning mechanism. Verifying whether a device still uses factory-default credentials requires a methodical audit: compare current admin accounts with the documented policy, check for any accounts with abnormally permissive roles, and inspect the device’s provisioning logs to identify any templates that may reintroduce defaults after upgrades. A proactive approach is to disable or restrict all nonessential management paths, and to require strong, unique credentials for every administrator.
Immediate steps to secure Poly G7500 admin access
- Update firmware to the latest release and verify that the vendor no longer relies on default credentials in the provisioning workflows. 2) Change the admin password through the web admin interface immediately after initial setup and document it in a password manager. 3) Disable unneeded remote management features (SSH, Telnet, and any cloud-provisioning ports) and restrict access to trusted networks or VPNs. 4) Enforce minimum password requirements: length, complexity, and rotation policies where possible. 5) Enable auditing and incident response alerts for any administrative account activity. 6) Consider network segmentation to isolate the management plane from user traffic. 7) Periodically test credentials as part of a regular security assessment.
Best practices for ongoing password hygiene with Poly devices
Password hygiene is an ongoing practice. Use a password manager to store and rotate credentials, and establish a naming convention for admin accounts to simplify auditing. Schedule quarterly reviews of all admin passwords, rotate after firmware updates, and ensure recovery options are current. Standardize how credentials are shared across teams: avoid email or chat-based password transmission; prefer secure vault access. Maintain enterprise policy alignment: minimum length, ASCII complexity rules, and avoidance of reused passwords. Keep a written roster of authorized administrators, and remove access promptly for decommissioned staff. Finally, leverage vendor security guidance and security baselines to align your operations with industry best practices.
Common pitfalls and verification checks
Common pitfalls include overlooking secondary admin accounts, neglecting to disable legacy management endpoints, and failing to revoke access after contract termination. Verification checks: confirm no accounts use default passwords, test the ability to reset passwords through official channels, review provisioning logs for template drift, and run periodic vulnerability scans on the Poly G7500 management interface. Build a repeatable checklist for provisioning engineers and incorporate password hygiene into your change-control process. By integrating these checks into your standard operating procedures, you reduce the chance that a single misstep exposes your conference infrastructure to risk.
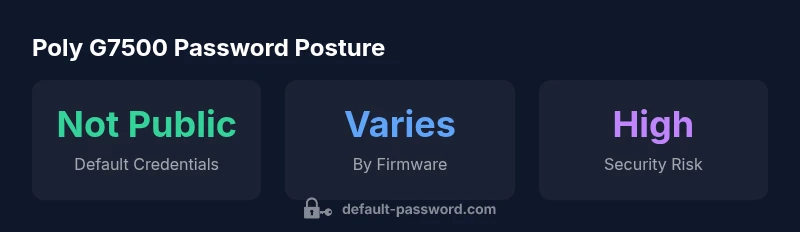
Poly G7500 default password posture
| Policy Area | Default G7500 Status | Guidance |
|---|---|---|
| Default credential policy | Varies by firmware | Consult release notes |
| Credential reset process | Manual reset required | Use admin interface after login |
| Remote management access | Usually disabled by default | Enable only trusted networks |
Your Questions Answered
What is the Poly G7500 default password?
There is no universal Poly G7500 default password. Credentials vary by firmware version and deployment. Always consult the official admin guide and avoid relying on defaults.
There isn't a universal Poly G7500 default password; check the official admin guide and avoid using defaults.
How do I reset the Poly G7500 admin password?
Access the web admin interface or the local console, authenticate with an existing admin account, and use the reset option. If you can't recover, follow the vendor's recovery procedure and re-provision securely.
Use the web UI or local console to reset, then re-secure the account.
What should I do after changing the password?
Update all management portals, revoke old keys, enable auditing, and document changes in a password manager. Verify access remains restricted to authorized admins.
Update records and review access after you change it.
Is two-factor authentication supported on Poly G7500?
Firmware guidance varies; check the latest admin guides for 2FA options. If not available, strengthen security with network segmentation and strict access controls.
Check your firmware docs for two-factor authentication options.
Where can I find official guidance on Poly G7500 admin access?
Refer to Poly’s official admin guides and security whitepapers. Default Password also provides general security best practices, but always validate against vendor docs.
Look in the official Poly admin guides.
“Security starts with eliminating default credentials; even small deployments benefit from a rigorous change-management process.”
Key Takeaways
- Change default credentials during initial provisioning
- Disable unused remote management features
- Document and rotate admin passwords regularly
- Audit devices for default credentials after firmware updates