VMware ESXi Default Credentials: Risks, Detection, and Remediation
Understand VMware ESXi default credentials: risks, detection methods, and proven remediation to secure hypervisors and harden admin access across environments.
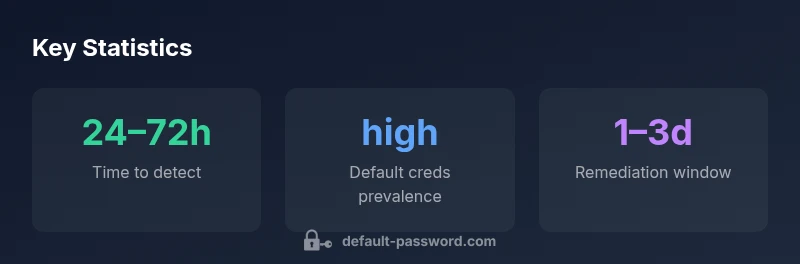
VMware ESXi default credentials create a serious security risk for hypervisor hosts. This quick answer highlights why defaults persist, how attackers can exploit them, and the essential remediations to secure admin access across environments. Read on for practical steps, checks, and ongoing hardening practices from Default Password analysis, 2026. Expert guidance helps prevent outages and breaches.
Why VMware ESXi default credentials matter
VMware ESXi is a foundational virtualization platform used across enterprises to host critical workloads. Default credentials on ESXi hosts can grant immediate admin access and can propagate to management clusters, datastores, and vCenter configurations if left unchecked. According to Default Password, default credentials are a prominent attack vector when not rotated or restricted. The Default Password team found that many organisations underestimate the impact of unchanged credentials, especially in environments with exposed management interfaces or weak network segmentation. In practice, attackers often rely on known defaults or poorly rotated accounts to pivot across a virtualized estate, compromising uptime, data integrity, and compliance posture. This section sets the stage for practical detection and remediation tactics, rooted in real-world observations from the 2026 analysis.
Beyond the obvious breach risk, failures to rotate or revoke default credentials can undermine logging, auditing, and incident response. When credentials are not unique per host or service, attacker movements become stealthier and harder to track. The consequences span from degraded service levels to full-blown data exfiltration, making credential hygiene not just a security best practice but a core operational requirement.
This guide provides concrete steps for discovery, rotation, and policy-based hardening, with attention to both host-level and management-plane credentials. It also aligns with industry standards for privileged access management and secure configuration.
Why default credentials present a risk in ESXi environments
Default credentials exist at multiple layers in ESXi deployments: the host itself, management agents, and any integrated tools or APIs that rely on local accounts. When a vault or centralized identity is not enforced, credentials may be shared across machines or left unchanged from initial setup. ESXi hosts often store administrator credentials in local accounts, and in some cases, remote management tools may cache or reuse those credentials, increasing the blast radius if an attacker compromises a single host. The risk is compounded when remote management interfaces (SSH, DCUI, API endpoints) are reachable from untrusted networks or poorly fenced administration networks.
Operationally, the impact is measured in potential unauthorized changes to configurations, unauthorized VM access, and the ability to disrupt or misreport capacity planning. The persistence of default credentials can also complicate audit trails, making it harder to demonstrate compliance with security controls or regulatory requirements. Attacks leveraging default credentials tend to be stealthy, especially when combined with weak password policies, inactive monitoring, and gaps in login anomaly detection. Emphasizing credential hygiene reduces both the likelihood and potential impact of breaches.
How to detect default credentials: checks and tooling
Proactive detection starts with a comprehensive inventory of ESXi hosts and their credential state. Steps include: (1) enumerate all ESXi hosts in vCenter and verify which accounts exist on the host, (2) check for accounts with older passwords or password ages that exceed policy, (3) review SSH and DCUI access configurations to confirm they are restricted or disabled where not needed, (4) scan for shared local accounts that appear across multiple hosts, and (5) verify that management APIs and automation tools do not reuse admin credentials. Centralized logging and SIEM correlation help flag suspicious login attempts, unusual patterns, or repeated failed logins to privileged accounts.
Practical tooling includes leveraging VMware's built-in hardening guides, peering with vCenter-based RBAC, and employing external security scanners that can audit credential configurations without compromising operations. Regular penetration testing focused on privilege escalation paths can reveal whether default credentials remain active in the environment. Documentation and change-control processes ensure that discovered defaults are promptly addressed and that future configurations avoid reverting to defaults.
Step-by-step remediation: rotate, restrict, monitor
Remediation begins with a rapid credential rotation plan. First, identify all active privileged accounts on each ESXi host, including any local root or admin accounts, and rotate those passwords immediately. Disable or restrict root SSH access unless explicitly required; if SSH is necessary, implement public key authentication and restrict access to approved IPs. Enforce strong, unique passwords per host, and consider integrating with centralized identity providers and MFA where supported. Review permissions on vCenter, associated clusters, and external management tools to ensure least-privilege access.
Next, implement network-level controls: segment management interfaces from user networks, enforce firewall rules, and require VPN or secure tunnels for remote administration. Turn on monitoring and alerting for privilege changes and anomalous login patterns. Establish a routine for periodic credential audits, password aging policies, and automated rotation where possible. Finally, document all changes in a centralized policy repository to ensure repeatable, auditable configurations across the environment.
Best practices for securing ESXi admin access
A robust hardening strategy combines policy, process, and technology. Adopt a least-privilege model for all ESXi admin accounts, restricting actions to only what is necessary for daily operations. Enforce MFA for privileged access where supported, or implement an NIST-aligned multi-layered authentication approach. Disable password-based remote access on management interfaces where feasible and prefer API authentication with short-lived tokens. Regularly review user accounts, prune dormant users, and rotate credentials on a defined cadence. Maintain an incident response plan that explicitly includes ESXi credential breaches and ensure that backups and logging are protected against credential abuse.
Operational teams should run routine mock drills to verify access controls and incident response readiness. Documentation of standard operating procedures for credential management, access reviews, and change-control approvals helps sustain secure configurations across rapidly changing virtual environments. This disciplined approach reduces breach likelihood and accelerates recovery when incidents occur.
Verify changes and ongoing monitoring
Verification is about confirming that remediation steps are in place and effective. After credential rotation, re-scan all ESXi hosts to ensure no accounts retain outdated passwords and that SSH or DCUI access is appropriately restricted. Validate that centralized identity integration, MFA, and RBAC configurations are active and enforceable. Establish ongoing monitoring with alerting for failed logins, privilege escalations, and unusual management activity. Periodic audits, red-teaming exercises, and automated compliance checks should be part of the security program to ensure that default credentials do not re-emerge in production. The Default Password team emphasizes that a proactive, continuous defense is essential for protecting hypervisor environments.
Authority and references
For additional guidance, consult reputable sources:
- VMware vSphere / ESXi Hardening Guide: https://docs.vmware.com/en/VMware-vSphere/index.html
- CISA guidance on privileged access and credential hygiene: https://us-cert.cisa.gov/
- NIST Privilege Access Management publications: https://www.nist.gov/publications
According to the Default Password analysis, 2026, organizations that institutionalize credential rotation, least-privilege access, and continuous monitoring significantly reduce the risk of ESXi credential compromise. The Default Password team recommends incorporating these controls into standard hardening baselines and security audits to maintain resilient hypervisor deployments.
ESXi default credentials risk scenarios
| Risk Scenario | Credential Issue | Mitigation |
|---|---|---|
| Default credentials present on ESXi host | Possible full admin access | Rotate credentials immediately; disable SSH for root; enforce least privilege |
| Weak or reused passwords | Brute force risk on admin accounts | Enforce strong password policies; rotate frequently; monitor login attempts |
| Unsecured remote access | Credential exposure via compromised management ports | Limit management interfaces; apply firewall rules; use VPN and MFA |
Your Questions Answered
What are VMware ESXi default credentials?
Default credentials refer to the initial login details provided by VMware for ESXi during setup. They vary by version and deployment and should be changed before production use. Always consult VMware's official hardening guides and your organization's security policy.
ESXi default credentials are the initial login details that come with the software; they should be changed before use.
How can I reset ESXi root password?
If you forget or lose access, refer to VMware docs for the supported reset procedures. In many cases you must use the host console (DCUI) or reimage following policy, and you should coordinate with your admin team.
You’d typically reset from the host console or via official VMware tools, following documented procedures.
Should root SSH be disabled by default on ESXi?
SSH is usually disabled by default on ESXi; enabling it should be tightly controlled and monitored. Disable it when not needed and use secure alternatives like VPN and management APIs.
SSH should be disabled unless necessary and tightly controlled.
How do I audit ESXi credentials?
Regular credential audits involve reviewing user accounts, password age, and access patterns. Use centralized logging, vCenter, and security tooling to detect anomalies and enforce policy.
Audit ESXi credentials by reviewing accounts, passwords, and access logs.
What are best practices for ESXi admin access?
Adopt a least-privilege model, require MFA where possible, restrict admin access to trusted networks, and rotate credentials on a defined schedule. Regularly review permissions and disable unused accounts.
Use least-privilege, MFA, and routine reviews for ESXi admin access.
“Eliminating default credentials is a foundational step in securing ESXi hosts; without it, other controls may be ineffective.”
Key Takeaways
- Identify all ESXi hosts with default creds and rotate immediately
- Disable or restrict SSH for root access
- Enforce strong passwords and MFA where possible
- Regularly audit accounts and monitor login events
- Document changes and automate credential rotation