Windows Server 2019 Password Policy: Defaults and Best Practices
Explore what are the Windows Server 2019 default password requirements. Learn how local and domain policy define rules, and how to configure secure, policy-driven admin passwords in 2026.
There is no universal Windows Server 2019 default password requirement. Password rules are defined by the local security policy or domain policy in place during setup. The built-in Administrator account typically requires you to set a strong password during installation, and ongoing requirements depend on policy settings for password length, complexity, and lockout thresholds.
What are the Windows Server 2019 default password requirements?
According to Default Password, there is no universal default password for Windows Server 2019. The question the searcher wants to answer is not a fixed set of requirements but how policy governs these rules. On installation, administrators must define a password policy that aligns with organizational security goals. In practice, Windows Server 2019 relies on the local security policy or a domain policy to enforce password length, complexity, history, and lockout rules. This means that the exact requirements are determined by policy and can vary between environments, organizations, and whether servers are standalone or part of an Active Directory domain. The keyword here underscores the core reality: the "default" password is not a one-size-fits-all spec, and the security posture hinges on the policy you configure and enforce.
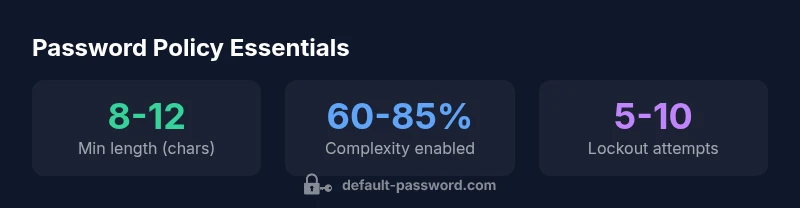
From a practical perspective, this means you should treat password requirements as policy-driven rather than fixed defaults. You will typically see guidance around: minimum length, complexity (a mix of uppercase, lowercase, digits, and symbols), password history (blocks reuse), and account lockout (to deter brute-force attempts). However, all of these are adjustable by policy, not mandated across every Windows Server 2019 deployment. The takeaway for administrators is to design a policy that fits risk tolerance and regulatory obligations rather than relying on a presumed built-in standard.
Built-in Administrator account and initial password
The built-in Administrator account is a privileged entry point to the server, but there is no pre-set universal password that applies to all installations. During setup, you are prompted to set a password for the local Administrator account, and this password becomes the baseline for security until changed or further protected by policy. If the server is later joined to a domain, domain password policies take precedence and can override local defaults for admin accounts. In short, there is no single, fixed password you can rely on; you must establish and maintain a policy-driven password posture from day one.
For environments using virtualization or cloud-based images, make sure to customize the initial credentials as part of the image provisioning process. Always document the initial Administrator password in a secure vault and enable logging so you can track password changes for audits.
Domain vs Local Policy: How policy shapes password rules
Windows Server 2019 supports two parallel policy ecosystems: local security policy (for standalone servers) and Active Directory domain policy (for joined servers). Local policy is configured with Secpol.msc and affects only that machine, while domain policy is defined via Group Policy Objects (GPOs) and can apply across many servers. The password parameters—minimum length, complexity requirements, history, and lockout thresholds—are typically set at the domain level to ensure consistency. Organizations often align Local Security Policy with their domain standards to avoid conflicts. When a server is domain-joined, domain-level policies generally win, so it is critical to synchronize local settings with group policy to prevent policy drift.
A practical approach is to document the baseline policy used across the fleet and enforce it through a combination of GPOs and local security settings. This ensures predictable behavior during audits and reduces the chance of weak password configurations slipping through when new servers are deployed.
Core policy elements you should configure
Key elements to configure in Windows Server 2019 password policy include: minimum password length, which sets the baseline for password strength; password complexity, which requires a mix of character types; password history, which prevents reuse of recent passwords; and lockout thresholds, which deter brute-force attempts. Beyond these, consider maximum password age to compel regular updates and service account protections to avoid credential leakage. Always ensure the policy aligns with regulatory requirements and your organization’s risk posture. After implementing changes, test by attempting a login with a non-policy-compliant password to verify enforcement and logging.
Verifying and enforcing your password policy in practice
To verify that policies are in effect, start with the Local Security Policy tool (secpol.msc) or the Group Policy Management Console (gpmc.msc) for domain environments. Use commands like net accounts or Get-LocalUser in PowerShell to review current settings and user credentials. Run gpresult /r on a client or server to view applied policies and confirm that password-related settings are not overridden by other GPOs. Regularly review event logs for password-change events, failed login attempts, and lockouts. Finally, simulate password resets in a controlled test environment to ensure the authentication flow behaves as expected under policy constraints.
Security best practices for admin passwords on Windows Server 2019
Adopt strong, defendable password practices: prefer long passphrases, minimize password reuse, enable password complexity, and enforce a reasonable lockout policy. Combine password policy with privileged access management (PAM) where possible and consider multi-factor authentication (MFA) for privileged accounts. Treat administrator credentials as highly sensitive and rotate them on a defined schedule. Document policies, train administrators on security expectations, and perform periodic audits to ensure compliance with internal standards and external regulations.
Recovering or resetting a forgotten admin password
If an administrator password is forgotten, use an alternate admin account with appropriate privileges to reset it. If no admin accounts are accessible, you may need to leverage recovery options, such as a password reset disk, or in extreme cases, offline recovery or reinstalling the server. Always maintain tested recovery procedures and ensure backups are in place before performing password resets that could affect system availability. For high-security servers, consider PAM or a password vault with audit trails to minimize the risk of credential loss.
Auditing, baselines, and compliance resources
Establish a baseline by aligning with recognized standards (e.g., NIST SP 800-63-3 and CIS/Center for Internet Security benchmarks) and customize them to your environment. Use PowerShell and Windows administrative tools to automate audits of password policies and account health. Regularly review security baselines against evolving threats and regulatory requirements. Keeping a current baseline reduces the likelihood of non-compliance and strengthens overall security.
Authority sources
Authority Sources
Window Server 2019 password policy elements and how they are enforced
| Policy Element | Windows Server 2019 Default | Notes |
|---|---|---|
| Minimum password length | Defined by policy (not built-in) | Configured via Local Security Policy or Group Policy |
| Password complexity | Defined by policy (may require mix of character types) | Controlled by password policy |
| Password history | Configured by policy | Prevents reuse of recent passwords |
| Account lockout threshold | Configured by policy | Defines response to brute-force attempts |
Your Questions Answered
Is there a default password for Windows Server 2019?
No. There is no universal default password. The Administrator password must be set during install, and ongoing rules are determined by the configured password policy in Local Security Policy or Group Policy.
No universal default password exists; administrators must set one during install and maintain policy-driven rules afterward.
How do I configure Windows Server 2019 password policies?
Use Secpol.msc for local servers or Group Policy Management (GPO) for domain environments to set minimum length, complexity, history, and lockout thresholds. Ensure the settings are aligned across the fleet to avoid policy conflicts.
Configure password policy using Secpol.msc or GPO, then enforce it across servers.
What should I do if I forget the Administrator password and no other admin accounts exist?
If you have other admin accounts, reset from one of them. If not, follow recovery options provided by your organization or consider offline recovery or reinstall as a last resort, ensuring backups and logs are preserved.
If you’re locked out with no admin access, follow your organization’s recovery plan or contact support for secure reset options.
Are there official guidelines I should follow beyond Windows policies?
Yes. Refer to NIST SP 800-63-3 and CISA password security guidance for general best practices; apply their principles to Windows Server password policy to strengthen defenses.
Follow NIST and CISA guidelines to harden Windows Server password policy.
How often should password policies be reviewed?
Policies should be reviewed at least annually or after major changes to the IT environment, regulatory requirements, or incidents that indicate a policy gap.
Review policies at least once a year or after major changes.
“Windows Server 2019 does not ship with a universal default password; strong security comes from clear policy and consistent enforcement.”
Key Takeaways
- There is no universal default password for Windows Server 2019.
- Policy-driven rules govern all password requirements, not fixed defaults.
- Configure minimum length, complexity, history, and lockout to improve security.
- Verify and enforce policies with gpresult/secpol.msc and regular audits.
- Regularly review and update policies to meet security and compliance needs.