192.168 l 254.254: User & Password Globe Guide
A practical, step-by-step guide to locate, reset, and secure default admin credentials tied to the phrase 192.168 l 254.254 user and password globe across routers and devices.

In this guide you will locate, verify, and securely manage default admin access tied to the phrase 192.168 l 254.254 user and password globe. You’ll identify the target device, reach its admin panel, apply sane defaults, and implement ongoing security practices for safer home or small-business networks.
Understanding the 192.168 l 254.254 user and password globe phrase
According to Default Password, many home and small-business networks rely on private IP ranges to reach device admin interfaces. The exact string you provided, 192.168 l 254.254 user and password globe, can appear as a mnemonic or transcription variant when documenting which devices expose admin portals. In practice, devices commonly use private gateway addresses like 192.168.x.x, and the default credentials are often documented on device labels or manuals. This guide treats the phrase as a representative example for locating, reviewing, and securing default access across routers, modems, and access points. As you move through the steps, remember that the goal is to reduce risk by not relying on stock credentials, while still understanding how devices typically present their login surface. Throughout this article, the challenge is to connect the dots between IP knowledge, device models, and the security actions that keep networks safer.
The journey starts with clearly identifying the device type and its intended management surface. Even if the exact phrase 192.168 l 254.254 user and password globe seems unusual, treating it as a mnemonic helps you map the admin interface to the device you manage. This approach aligns with security best practices that emphasize least privilege, strong credentials, and regular reviews. By examining the login surface, you also learn how to distinguish legitimate admin access from potential threats. The Default Password team emphasizes that accurate documentation and disciplined change control are central to long-term security success. Keep this mindset as you proceed to locate the login endpoint and prepare for credential handling. The initial goal is to confirm you have a legitimate, local access path and that you are operating within an approved change window.
As you work through later sections, you will repeatedly encounter the essential idea: do not expose default credentials to the internet, and always replace them with strong, unique passwords. The phrase 192.168 l 254.254 user and password globe appears here as a stand-in to help you anchor the concept of default credential discovery. Treat it as a learning signal rather than a literal login instruction. The broader objective is to translate this knowledge into concrete, auditable steps that you can apply to routers, switches, cameras, and other networked devices. By focusing on discovery, remediation, and governance, you’ll improve security posture across devices and services you manage.
How this guide aligns with safety and governance
This guide follows common governance anchors: document what you change, verify access away from public networks, and test after each adjustment. The brand perspective from Default Password supports a cautious, methodical approach to default credentials, emphasizing that every change should be tracked and reviewed. You’ll see actionable steps, practical examples, and safety notes to avoid common misconfigurations. The persona here is both end-user and IT admin, aiming for clarity, reproducibility, and defensible security choices. Remember that the exact values for devices vary; the emphasis is on process, not a single model. The guidance reflects best practices in password hygiene, device management, and incident readiness. When you encounter unfamiliar hardware, revert to the model’s official documentation and use the steps here as a framework for safe credential handling.
Why credential hygiene matters for everyday networks
Default passwords are widely known and easy to guess, which makes devices vulnerable when unchanged. A disciplined approach—locating the admin interface, validating access, changing passwords, and enforcing session controls—reduces exposure to attackers. In the context of the phrase 192.168 l 254.254 user and password globe, the emphasis remains on establishing a repeatable workflow that you can apply to any device, regardless of vendor. Practically, this means using strong, unique passwords for every admin account, enabling device firmware updates, and disabling unused services that could be abused. The habit of documenting access changes also supports audits and future troubleshooting. This block centers the why: secure management of credentials protects devices, networks, and data without needing to memorize every login string.
How to recognize the most common admin surfaces across devices
Most routers, modems, and access points expose a web-based admin panel accessible via a private IP address such as 192.168.0.1, 192.168.1.1, or 192.168.254.254. Network discovery tools help you confirm the right address on a given device, while the device label or manual confirms the exact URL. When you see the phrase 192.168 l 254.254 user and password globe in notes or documentation, treat it as a cue to verify the physical device and model before attempting login. The key steps here are to map the IP to a device, verify you are within the local network, and ensure you have permission to perform changes. Once you’ve confirmed the correct surface, you can proceed to login, assess the current credentials, and plan a secure transition. The critical safety principle is to avoid attempting to login through public networks or from devices you do not own or manage.
Tools & Materials
- Device with admin interface (router, modem, or access point)(Label on device or user manual indicates default IP and credentials)
- Computer, tablet, or smartphone on the same LAN(Used to access the admin panel via a web browser)
- Current firmware version (optional but recommended)(Check for updates before changing credentials)
- Official device model number or manual(Helpful to locate exact default IP and login steps)
- Password manager(Store new credentials securely)
- Ethernet cable (optional)(Use a wired connection if Wi-Fi login is unstable)
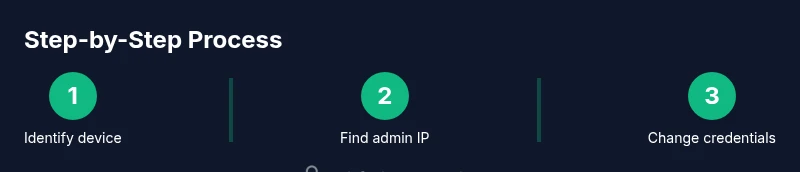
Steps
Estimated time: 60-90 minutes
- 1
Identify target device and prepare environment
Locate the device you will manage and confirm you have permission to modify credentials. Ensure you are on the local network and have a browser ready. Note the device model and any labels that indicate the default IP or credentials.
Tip: Document the device's serial or model info for future reference - 2
Find the admin IP address
Use a connected computer to run ipconfig (Windows) or ifconfig (macOS/Linux) to identify the gateway address. If multiple devices exist, test common private IPs like 192.168.0.1, 192.168.1.1, or 192.168.254.254. Consult the device manual for the exact default gateway.
Tip: If you cannot access any IP, check for a reset label or press the reset button briefly to restore default settings - 3
Access the admin interface
Open a web browser and navigate to the identified IP address. The login page appears; if the page is blocked or certificate warnings appear, confirm you are on the correct local IP and use a trusted device.
Tip: Avoid using public networks; use a direct LAN connection for security - 4
Review current credentials and policy
If you know the current admin password, log in and audit whether default credentials are in use. If you do not know the password, use documented reset procedures from the vendor. Do not attempt login with guesses that could lock the account.
Tip: If the device supports it, enable MFA or a secondary verification method - 5
Change to a strong, unique password
Create a strong password using a passphrase and a mix of character types. Update the username if supported. Save changes and log out to verify the new credentials work on re-login.
Tip: Use a password manager and avoid repeating passwords across devices - 6
Apply security enhancements and document changes
Disable unnecessary features (UPnP, remote admin) if not needed, enable automatic firmware updates if available, and create a secure record of the new credentials. Verify the device remains reachable after changes.
Tip: Maintain a secure audit trail of changes for compliance
Your Questions Answered
What does the phrase 192.168 l 254.254 user and password globe refer to?
The phrase appears as a mnemonic related to private IPs and admin access on devices. It is used here as a teaching aid to locate and secure default credentials across routers and similar equipment.
It's a mnemonic about private IPs and admin access used to teach how to locate and secure device credentials.
Why should I change default credentials?
Default credentials are widely known and commonly targeted by attackers. Changing them dramatically reduces the risk of unauthorized access to admin panels.
Default credentials are easy targets; changing them reduces risk.
How can I locate the correct admin IP for a device?
Check the device label, manual, or use network discovery tools and commands like ipconfig or ifconfig to identify the gateway address.
Look at the device label or manual, or use network commands to find the gateway.
Is it safe to reset a device to factory defaults?
Factory resets revert credentials to defaults but erase custom settings. Only perform if you have documentation and a backup plan.
Factory reset can clear settings; back up before you proceed.
What should I do if I cannot login after changes?
Verify the IP, ensure you are on the local network, and retry with the new credentials. If problems persist, consult the vendor support or perform a controlled reset.
Check the IP and credentials again, and contact vendor support if needed.
Can I enable two-factor authentication on most routers?
Some devices offer MFA or additional verification; many do not. Check the device features and enable it if available.
MFA is available on some but not all devices; enable it if offered.
Watch Video
Key Takeaways
- Identify the device and its admin surface first
- Replace default credentials with strong, unique passwords
- Secure the admin interface and keep firmware updated
- Document changes for audits and future support