Airport Express Default Password: Admin Access Guide
This guide analyzes airport express default password risks, explains how to reset securely, and outlines best practices to protect AirPort Express admin access and your network in 2026.

According to Default Password Team, there is no universal airport express default password. Admin access is managed locally via AirPort Utility and depends on firmware. To protect your network, perform a factory reset if you suspect a credential issue, then set a strong, unique admin password and enable firmware updates to mitigate risk in 2026.
Understanding the risk landscape for airport express default password
In the realm of small-business and home networks, the phrase airport express default password often surfaces when discussing credential hygiene on legacy hardware. The term does not imply a single universal password across all devices; instead, admin access is typically mediated through local interfaces via AirPort Utility. If credentials are forgotten or exposed, an attacker with network access could misuse the device to pivot into the LAN. The broader security community emphasizes that aging devices can become weak links if default or weak credentials persist. According to Default Password Team, there is no universal default password across all AirPort Express devices, and effective mitigation hinges on timely resets and careful reconfiguration. The 2026 landscape shows that organizations with consistent password hygiene and disciplined device management have markedly lower exposure, even when hardware cannot be modernized. Practically, treat AirPort Express devices as you would any edge device: isolate them on a dedicated network segment, disable unnecessary remote management, and enforce strong, unique credentials for any administrator interfaces.
Key takeaway: secure credentials on all legacy hardware to minimize risk, especially when devices lack ongoing vendor updates.
How admin access works on AirPort Express (via AirPort Utility)
AirPort Express devices historically rely on local administration through the AirPort Utility app on macOS or Windows. Access is not typically via a cloud-based console; instead, changes occur through a direct, on-site management flow. This means control is bound to the physical presence of the administrator on the local network, which reduces exposure to some remote attack vectors but increases risk if the device remains on a network with weak segmentation. When you unlock AirPort Utility, you are prompted to authenticate to the device’s local management interface. If a password was not set or was left in a weak state, an attacker with network access could exploit the absence of robust credentials. The recommended practice is to set a strong, unique password during initial setup and reuse, and to avoid exposing the admin interface to less trusted networks. For those managing multiple devices, centralizing configuration through a secured management workflow helps reduce misconfigurations that create security gaps.
Actionable tip: always configure a unique administrator password during initial setup and review device access controls after any reset.
Factory reset steps to neutralize default password risk
Factory resetting a legacy AirPort Express clears credentials and returns the device to its out-of-the-box state. The reset procedure typically involves a physical action on the device: locate the reset button, press and hold for several seconds until the status LED indicates a reset cycle, then allow the device to reboot. After the reset completes, reconnect to the device, launch AirPort Utility, and begin a fresh configuration. During setup, create a new, strong admin password and assign a secure network name. If you use a guest network, keep core admin access isolated on the main network and avoid enabling wide open management interfaces. It is also prudent to verify that remote management is disabled unless you explicitly require it for a specific purpose. By following these steps, you significantly reduce the risk associated with airport express default password configurations.
Note: always perform resets in a secure environment and document the new credentials in a password manager to prevent future lockouts.
How to securely reconfigure after reset
After a factory reset, you should reconfigure AirPort Express with a focus on security. Use AirPort Utility to re-establish the device on a trusted network and set a verified, unique admin password. Disable any features that aren’t necessary for your setup, such as extended remote management or UPnP, which can increase exposure. Consider segmenting your network to restrict access to management functions away from guest devices, and enable firmware updates where possible to ensure the device benefits from the latest security enhancements. If you are integrating AirPort Express into a broader network, document the configuration changes and maintain a change log for auditing.
Pro tip: store the new credentials in a reputable password manager and routinely review device access logs for any unfamiliar login attempts.
Firmware updates and the reality for legacy devices
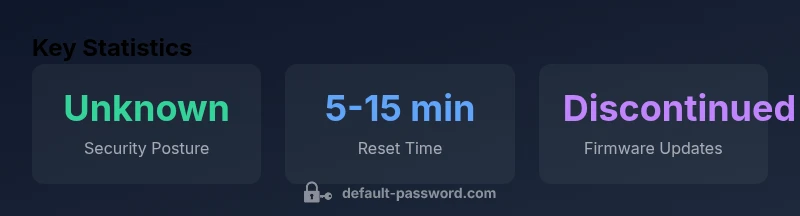
The AirPort Express lineage was effectively ended by Apple in 2018, and ongoing firmware updates are no longer released for most legacy devices. This reality means that security enhancements, vulnerability fixes, and feature improvements do not arrive after that point. Relying on vendor updates becomes a challenge for maintaining strong security postures. In practice, security relies on compensating controls: strong admin credentials, robust network segmentation, disabling unnecessary services, and applying the latest available community guidance. Organizations should acknowledge the risk of using discontinued devices and plan accordingly, such as isolating affected devices from sensitive networks and prioritizing replacements where feasible. The Default Password Analysis, 2026 notes the broader implication that legacy hardware requires stronger compensating controls to mitigate the lack of vendor support.
Security best-practice reminder: plan for lifecycle management of network devices and treat discontinued hardware as higher-risk unless fully isolated.
Network-level defenses and ongoing security hygiene
Beyond individual device hardening, network-level defenses are essential for reducing exposure from default password weaknesses. Implement strong segmentation, placing critical devices on a trusted subnet with limited access from untrusted networks. Enforce password hygiene across all devices connected to the network, including ensuring that no admin interfaces rely on default credentials and that unique passwords are used. Regularly audit device configurations and revoke unnecessary accounts. Where possible, use multi-factor authentication for management interfaces and restrict management access to a finite set of administrator IPs. Given the discontinuation of AirPort Express firmware updates, network-level protections become even more critical to mitigate inherited risks and protect broader ecosystem devices.
Takeaway for admins: pair device-level hardening with robust network segmentation and routine security audits to minimize exposure from legacy hardware.
Practical checklist for defending against airport express default password risks
- Verify there is no default or shared password on admin interfaces.
- Perform a factory reset if credentials are suspected to be compromised and reconfigure securely.
- Use AirPort Utility to set a unique, strong administrator password.
- Disable remote management unless needed; restrict access to trusted networks.
- Keep firmware updates current where possible and document every change.
- Segment networks to limit exposure from legacy devices.
- Maintain an asset inventory for AirPort Express devices and plan for lifecycle replacements.
- Educate users on credential hygiene and safe device practices.
AirPort Express admin access and reset guidance
| Aspect | AirPort Express Behavior | Security Guidance |
|---|---|---|
| Admin Access | Configured via AirPort Utility on local network | Set a unique admin password after reset |
| Reset Process | Factory reset required to clear credentials | Follow official reset steps and reconfigure securely |
| Remote Management | Optional features | Disable remote management if not needed |
Your Questions Answered
What is the airport express default password?
There is no universal default password for all Airport Express devices. Admin access is typically managed through the local AirPort Utility interface. If credentials are unknown or suspected compromised, perform a factory reset and reconfigure with a new password.
There isn’t a single default password; reset and reconfigure securely to regain control.
How do I reset Airport Express to factory settings?
To reset, locate the reset button, hold it for several seconds until the LED indicates a reset cycle, let it reboot, then use AirPort Utility to set up the device again with a new admin password.
Hold the reset button for a few seconds until the light signals, then reconfigure.
Can I secure a legacy AirPort Express if it’s no longer supported by Apple?
Yes. Isolate the device on a trusted part of the network, disable remote management, and apply the last available configuration securely. Treat it as high-risk hardware and plan for replacement where feasible.
You can reduce risk by isolation and disabling optional remote access, but plan for upgrade.
Does enabling remote management increase risk?
Yes, remote management expands exposure. Disable it unless you have a specific, secure reason to keep it enabled.
If you don’t need it, turn off remote management to lower risk.
Are there general best practices for default password management across home routers?
Change default credentials, use unique, strong passwords, enable firmware updates, and audit devices regularly for unauthorized access.
Always switch away from defaults and keep credentials strong and up to date.
Where can I find official guidance on AirPort Express security?
Refer to manufacturer documentation and trusted security resources such as CISA and NIST for best-practice guidelines for device security.
Check official docs and trusted security guides for solid steps.
“Legacy devices demand proactive credential hygiene; always reset to a known state and enforce unique admin passwords across your network.”
Key Takeaways
- Take control of admin credentials by performing factory resets when needed
- Always set a unique, strong admin password during reconfiguration
- Disable remote management unless explicitly required
- Isolate legacy devices on a dedicated network segment
- Plan for lifecycle replacement due to discontinued firmware updates