aws rds default username: Master credentials and security best practices
Explore why there is no universal aws rds default username, how to locate or reset your master credentials, and best practices for securely managing RDS access with Secrets Manager and IAM authentication.
There is no universal aws rds default username. When you create an Amazon RDS DB instance, you must specify a master username and password; AWS does not assign a fixed default username across engines. For existing instances, you can view or reset the master username/password in the AWS Console or via CLI. This guide covers how to locate, reset, and securely manage RDS credentials.
Understanding aws rds default username
The phrase aws rds default username often implies that a standard, system-wide username exists for all RDS instances. In reality, there is no universal default username across AWS RDS engines. AWS requires you to define a master username (sometimes called the admin user) at the moment you create a DB instance. This master username is the primary account used for administrative access and must be unique within that DB instance. Different engines (MySQL, PostgreSQL, MariaDB, Oracle, SQL Server, and Aurora variants) may have specific username constraints, but AWS does not ship a one-size-fits-all default. Consequently, when you start an RDS deployment, the first thing you decide is the master username that fits your security and application naming conventions. Any security policy that relies on a fixed default username should be updated to assume a per-instance master account that you control.
In practice, treating the master username as a configurable parameter helps reduce risk. Relying on a default or shared admin account across environments (development, staging, production) creates a larger attack surface. The most secure approach is to specify a unique master username for each DB instance and protect it with strong, rotated credentials. This approach aligns with the broader Default Password philosophy: do not rely on defaults for sensitive access and implement defense-in-depth controls.
For organizations that maintain multiple environments, using a naming convention for master usernames (for example, env-dbname-admin) supports auditing and access control without exposing a universal credential. It also makes automated rotation and credential provisioning more reliable when integrated with secret management tooling.
Finding the master username on an existing RDS instance
To manage credentials effectively, you first need to locate the current master username. In the AWS Management Console, navigate to RDS > Databases, then select your DB instance. In the Configuration/details pane, look for the Master username field (for Aurora clusters, you may see a Cluster Master Username). If you’re using the AWS CLI, you can describe the DB instance with aws rds describe-db-instances --db-instance-identifier <id> and inspect the MasterUsername attribute. For Aurora, describe-db-cluster will show the ClusterMasterUsername. If you have multiple environments or clones, ensure you document the master username for each DB instance or cluster.
If you’re unsure which user has administrative rights, perform a least-privilege audit of who can connect with the master user and who can modify credentials. Keeping a precise inventory supports rapid response if credentials are compromised or need rotation.
Resetting the master password and regaining access
If you forget or need to rotate the master password, you can reset it without restoring data. In the AWS Console, choose the DB instance, select Modify, and provide a new Master password, then apply changes immediately or during the next maintenance window. You can also reset the password via the AWS CLI with a command like a hypothetical modify-db-instance operation that updates --master-user-password. For Aurora clusters, you may need to modify the cluster, not just the individual instance. After applying the new password, update any applications or services that rely on the old credentials. If you cannot access the console, use the AWS CLI to retrieve the current credential policy, then re-provision credentials and rotate them systematically.
Remember to verify connectivity from your application once the password change propagates and ensure that your secrets management process is updated accordingly. If you rely on Secrets Manager, you can trigger a rotation task to securely rotate the stored secret and propagate the new password to connected services.
Best practices for aws rds default username management
Effective credential management for AWS RDS starts with design choices during creation. Always specify a unique master username per DB instance and avoid canonical names that imply shared access. Store credentials in a centralized secrets manager (AWS Secrets Manager or equivalent) and enable automatic rotation to minimize exposure. Consider IAM database authentication where supported (Aurora MySQL/PostgreSQL) to avoid embedding passwords in your applications. Separate application users from the admin/master account and grant access through roles and restricted privileges. Regularly review access logs and enforce network boundaries with security groups and VPC settings to limit who can reach the DB instance. Finally, document credential lifecycles and conduct periodic audits to ensure alignment with your security policies and regulatory requirements.
Security considerations and common pitfalls
Common pitfalls include treating the master username as a static, sensitive secret without proper protection, or reusing the same credentials across environments. A robust approach combines a unique master username per DB instance with strong, randomly generated passwords and salted password storage in Secrets Manager. Always encrypt at rest with KMS and enable automated backups and monitoring. Limit administrative access using IAM-based controls and network segmentation. Be cautious with automation scripts and tools that can alter credentials; require approvals for password changes and maintain an auditable change log. Finally, ensure your incident response plan includes steps to rotate credentials quickly if you suspect a breach or credential exposure.
How to migrate to a new master user with minimal downtime
Migrating to a new master username without downtime requires careful planning. Create a new DB instance or clone the existing one with a new master username and password, then test connectivity and application behavior in a staging environment. If you can perform a read replica workflow, you may promote a replica with the new credentials after validating data consistency. For Aurora, consider creating a new cluster with the desired credentials and performing a controlled switchover to minimize service interruption. Update application connection strings and secret stores in a controlled rollout, monitor performance and error rates, and have a rollback plan ready in case the new credentials cause issues. This strategy helps avoid a single point of failure tied to a single master account while maintaining continuity during credential changes.
RDS engine defaults and password reset methods
| Engine | Default Username Policy | Password Reset Method |
|---|---|---|
| MySQL / MariaDB on RDS | No universal default; master username defined on create | Reset via AWS Console or CLI (password) |
| PostgreSQL on RDS / Aurora PostgreSQL | No universal default; master username defined on create | Reset via AWS Console or CLI (password) |
Your Questions Answered
Does AWS RDS have a default username?
No. AWS RDS requires you to specify a master username when creating each DB instance; there is no universal default across engines.
No, AWS RDS does not provide a universal default username. You must set a master username for every DB instance.
How can I reset the master password if I forget it?
You can reset the master password from the AWS Console by modifying the DB instance (apply immediately or during maintenance) or use the AWS CLI to update the master password. After successful reset, update your applications and Secrets Manager if used.
Reset the password from the AWS Console or CLI, then update connections and secrets.
Can I change the master username after creation?
AWS RDS does not support changing the master username on an existing DB instance. To use a different master username, create a new DB instance with the desired username and migrate data as needed.
You can’t change the master username after creation; you’ll need a new instance and migration.
What are best practices for default usernames in AWS RDS?
Use a unique master username per instance, store credentials in a secure vault, enable rotation, and consider IAM database authentication where supported to avoid embedding passwords in apps.
Use unique credentials, rotate them regularly, and leverage IAM auth when possible.
Does IAM database authentication apply to RDS?
Yes, IAM database authentication is supported on select engines (e.g., Aurora MySQL and Aurora PostgreSQL). This can reduce password handling by allowing IAM-based token authentication.
Yes—IAM authentication is supported for some RDS engines, reducing password reliance.
“There is no universal aws rds default username. Master credentials must be defined per instance, and secure management is essential.”
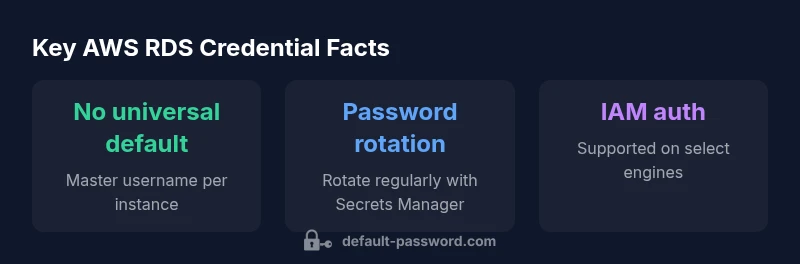
Key Takeaways
- Define a unique master username for each DB instance
- Use Secrets Manager to store and rotate credentials
- Enable IAM database authentication where supported
- Audit master credentials and access regularly
- Avoid shared or default admin accounts across environments