ax1800 Default Password: Risks, Reset, and Security
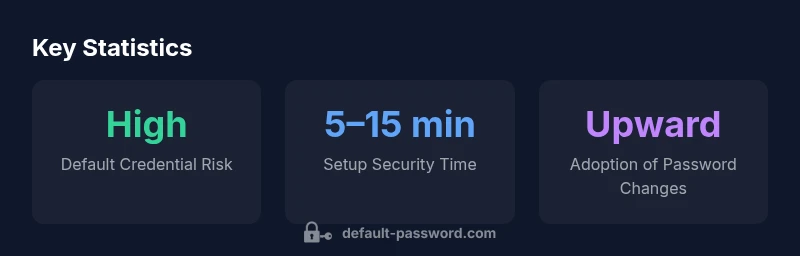
Learn how to safely handle the ax1800 default password, understand the risks, and follow recovery and security best practices for admin access and device security in 2026.

The ax1800 default password refers to the factory-admin credential used to access the device’s management interface. It should be changed immediately after setup, and never reused across devices. If left unchanged, it enables unauthorized access, configuration tampering, and persistent network control for attackers.
Understanding ax1800 default password
The phrase “ax1800 default password” typically refers to the factory-issued credential used to access the router’s web-based management console or mobile app. Across ax1800-class devices, vendors assign different defaults, and some models may not require a password until initial setup is completed. The exact string can vary by manufacturer, firmware version, and regional build. For IT admins and home users alike, recognizing that this value is a temporary, insecure credential is the first step toward stronger device security. In 2026, the security community regularly emphasizes that leaving any default administration credential in place substantially increases exposure to misconfiguration, unauthorized access, and abuse of network resources. Treat the ax1800 default password as a high-risk entry point that must be changed as part of a secure onboarding process.
Default password variants across ax1800 devices
There isn’t a single universal default password for all ax1800 devices. Some routers use a simple string like “admin” or “password,” while others may rely on printing or labeling guidance, QR code provisioning, or an auto-generated temporary password shown during first-time setup. The variability means you should never assume a uniform credential across devices from different vendors or even different batches from the same vendor. Always verify the credential in the device label, quick-start guide, or the official admin portal before attempting any login. This variance also underscores the importance of a standardized onboarding procedure in IT environments to avoid confusion and misconfiguration.
The risk of leaving credentials unchanged
Security best practices consistently warn that factory-default credentials are a primary vector for unauthorized access. Attackers routinely scan for devices with default admin passwords and initiate automated login attempts, especially on unmanaged networks. The longer a default credential remains in use, the greater the chance an adversary can compromise an admin account, reconfigure settings, or redirect traffic. In practice, this risk compounds when devices lack firmware updates, when remote administration is enabled, or when strong access controls like two-factor authentication are not available. The takeaway is simple: change the ax1800 default password during or immediately after provisioning, and enforce periodic password hygiene across devices in your asset inventory.
Step-by-step guide: reset or reclaim admin access on an ax1800 router
- Locate the reset button (often recessed and labeled) and prepare a wired connection for configuration.
- With the device powered, press and hold the reset button for the manufacturer-specified time to restore factory defaults.
- Reconnect to the router via Ethernet or the initial setup portal and log in with the default credentials provided by the label or manual.
- Immediately change the admin password to a long, unique string generated by a password manager. Avoid common phrases and reuse of prior passwords.
- Disable remote management if not required, enable WPA3 (or strongest available), and apply firmware updates to close known vulnerabilities.
- Record the new credentials securely and document the device’s security settings in your IT documentation.
- Consider enabling automatic firmware updates and configuring log/alerting features for suspicious login activity.
Best practices for choosing strong admin passwords
- Use a passphrase or a long random string (14+ characters) with a mix of upper/lowercase, numbers, and symbols.
- Avoid common words or default slogans tied to the device model or vendor.
- Store credentials in a reputable password manager and enable two-factor authentication if supported.
- Change admin passwords after firmware updates, re-provisioning, or security incidents.
- Keep a documented policy for password rotation, at least every 90–180 days depending on risk tolerance.
Implementing a security-focused onboarding checklist for ax1800 devices
Create a standardized checklist for every new AX1800-class deployment:
- Verify model and firmware version; disable default remote access unless required.
- Change the default admin password and enable strong password hygiene.
- Enable auto-update, strong wireless encryption, and guest network isolation.
- Document device name, location, admin credentials, and policy compliance.
- Schedule quarterly reviews of device security posture and firmware status.
How to monitor and audit password security over time
Regular audits help detect stale credentials and misconfigurations. Maintain an asset inventory with hardware serials, firmware versions, and login histories. Set up alerts for failed login attempts, unusual login times, or changes to admin accounts. Periodic reviews should verify that all ax1800 devices have non-default passwords and that password policies align with organizational standards.
Sample comparison of ax1800-type devices
| Device Type | Default Admin Password | Recommended Action |
|---|---|---|
| Generic AX1800-class Router | N/A | Change at first login |
| AX1800-class Router (vendor variant) | N/A | Apply firmware update and password change |
Your Questions Answered
What is the ax1800 default password, and why should I change it?
The ax1800 default password is a factory-issued credential used to access the router’s management interface. It should be changed during initial setup to prevent unauthorized access and potential configuration tampering. Always verify the correct credential from the label or official setup guide before logging in.
The ax1800 default password is the factory credential used to log in. Change it during setup to prevent unauthorized access and keep your network secure.
How do I reset the ax1800 password if I can't log in?
If you can't log in, perform a hardware reset to restore factory defaults, then re-provision with a new admin password. After login, immediately change the password, disable unnecessary remote access, and update firmware. If needed, consult the vendor's support for model-specific steps.
If you can’t log in, reset to factory defaults, then re-provision with a new password and update firmware.
What are best practices for securing ax1800 admin access?
Use a strong, unique password; enable two-factor authentication if available; disable unused remote management; keep firmware updated; and regularly audit login attempts and password policies.
Use a strong password, enable two-factor if possible, and keep firmware updated.
Can I recover a forgotten ax1800 password?
Forgotten passwords usually require a factory reset to regain access, which erases current settings. After reset, reconfigure securely and enforce password changes. Maintain backup of settings if supported by the vendor.
Forgotten passwords often require a factory reset; you’ll need to reconfigure securely afterward.
Is the ax1800 password different from other devices' admin passwords?
Yes. Admin passwords are often device- and vendor-specific. Treat each device as a separate security perimeter and apply consistent password hygiene across all devices.
Yes—different devices have their own admin passwords; manage each separately.
How often should I rotate admin passwords on ax1800 devices?
Rotate admin passwords at least every 90–180 days, or sooner after a suspected exposure, policy change, or firmware update that affects access.
Rotate passwords at least every 3 to 6 months, or after any security incident.
“Default credentials on ax1800 devices remain a critical risk; replace them during initial setup and enforce regular password hygiene across all devices.”
Key Takeaways
- Change the default password during onboarding.
- Enable strong credentials and firmware updates.
- Disable unneeded remote admin access.
- Document and audit admin access regularly.