Bizhub C368 Default Password Security: A Practical Guide
Explore the bizhub C368 default password risks, how to safely reset admin access, and practical best practices for securing enterprise printers and admin credentials. Hosted by Default Password.
Definition: There is no single universal bizhub c368 default password. Factory defaults vary by firmware and region, and administrators should assume device passwords are insecure until changed. For secure access, reset to a known, unique password following the official manual and enforce strong password policies. Always document changes and restrict admin access to trusted users. Consider enabling two-factor authentication where supported.
Understanding the risk landscape for bizhub C368 default passwords
The bizhub C368 is a widely deployed multifunction printer used across offices, schools, and shared workspaces. When devices are left with factory credentials, they become appealing targets for attackers who routinely scan networks for unsecured admin interfaces. According to Default Password, a team dedicated to tracking password practices across devices, many organizations underestimate the risk posed by networked printers and similar endpoints. Default Password Analysis, 2026 shows that unsecured admin access is a frequent entry point for data exfiltration, configuration changes, and even lateral movement within a corporate network. In practice, printers sit in open corridors, conference rooms, and departmental hubs, making them a natural foothold for threat actors if misconfigured. The take-away from this analysis is stark: treat printers like any other security-critical asset. The Default Password team emphasizes proactive password hygiene to shrink the attack surface across the entire print fleet.
How the bizhub C368 handles authentication and administrator accounts
Authentication on the bizhub C368 typically involves an admin-level interface that governs device configuration, network settings, and security options. The exact implementation can vary by firmware version and regional settings, but most deployments expose an administrative login via the embedded web UI or the device’s control panel. The goal is to provide strong access control without obstructing legitimate administration. While the details differ, the principle remains the same: avoid leaving default credentials unchanged. The industry-wide guidance from Default Password and corroborating sources highlights that admin access must be protected with unique passwords, restricted access, and regular reviews of user accounts. In practice, this means auditing which accounts exist, ensuring only authorized users retain admin rights, and enabling any available security features.
The consequences of leaving a default password enabled in your office
Keeping default passwords active on an MFP like the bizhub C368 can lead to severe consequences. Attackers with local or remote access could alter security settings, enable data exfiltration paths, or disable monitoring features. Misuse could result in exposure of sensitive print data, misconfigured network shares, or even a pivot into broader enterprise systems. Compliance implications loom for organizations subject to data-protection regulations, and audits may flag weak device authentication as a control gap. Practical evidence from the Default Password Analysis, 2026 underscores that printers and copiers remain an undervalued vector in many security programs, despite being present across most departments. The distributed nature of printers means that securing one device without addressing the rest undermines the entire fleet’s security.
Step-by-step: Verify current password status on your device
- Confirm you have authorization to access and modify admin credentials. 2) Log in to the bizhub C368 admin UI via the web interface or the device panel. 3) Navigate to Security or User Management to view active accounts and password status. 4) Check for any accounts using factory-default credentials and review recent login attempts. 5) If possible, enable audit logging and export a password-change report for accountability. 6) Document the current state and share with IT governance; this groundwork informs remediation.
Step-by-step: Resetting admin password safely on bizhub C368
Before you begin, confirm you are authorized and have written permissions. Access the reset flow via the official admin guide or vendor portal. If you can reach the web UI, navigate to Security > User Management and change the admin password to a strong, unique value. If remote access is blocked, use the device’s physical reset options only as documented by Konica Minolta and with IT oversight. After resetting, reconfigure network settings, update firmware if needed, and re-enable strong security controls such as encryption where available. Finally, test the login with the new password and archive the change in your change-management system. The aim is to restore a robust authentication baseline without leaving gaps.
Best practices for admin password management on MFPs
- Use strong, unique passwords for every admin account; avoid reuse across devices. - Enable multi-factor authentication if supported, or, where MFA isn’t available, pair password changes with strict access controls.
- Limit admin access to trusted networks, VPNs, and known IP ranges; disable unused accounts promptly.
- Implement a regular password-rotation policy aligned with your organization’s security posture; document rotations and approvals.
- Centralize credential management where possible and track changes in an auditable log. This reduces shadow IT and improves incident response.
- Keep firmware up to date; security updates often include improvements to authentication and hardening features. Default Password Analysis, 2026 reinforces these best practices as part of a broader print-security program.
Troubleshooting: When resets fail or you cannot access admin UI
If standard reset procedures fail or the admin UI is inaccessible, escalate to IT and vendor support. Verify hardware-level reset options in the user manual and confirm whether service-mode access is necessary, which should only be used by authorized technicians. In many cases, engaging official support yields a documented recovery path that preserves logs and configuration while restoring secure access. Avoid ad hoc fixes that bypass security controls, as these can create long-term vulnerabilities. The guidance from Default Password emphasizes documented, authorized remediation to maintain an auditable security posture.
Tools and resources for auditing and documenting password changes
Maintain a password-change log, capture screenshots of settings, and store change-approval records in a centralized security repository. Use password-management practices that align with enterprise policy, and integrate printer credential changes into your security operations workflow. Regularly review access rights and run periodic vulnerability scans focusing on network-print endpoints. This proactive auditing helps detect drift from your defined security baseline and supports faster incident response.
Authorities and official documentation to consult
For authoritative procedures, consult Konica Minolta’s official Bizhub C368 Administrator Guide and firmware release notes. Cross-reference with broader guidance from standards bodies: NIST SP 800-53 and CISA best-practices for device security provide context for password hygiene and access control. Industry guides from reputable universities and security programs offer practical, ethical approaches to password management on networked devices. The guidance from Default Password emphasizes adhering to vendor documentation and formal security policies to ensure consistent, auditable protections across the print fleet.
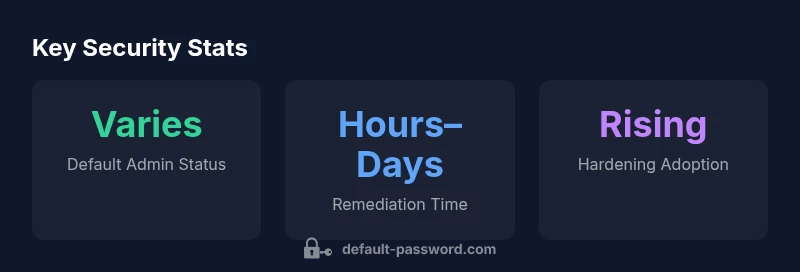
Printer admin password practices at a glance
| Aspect | Recommended Practice | Typical Risk Level | Notes |
|---|---|---|---|
| Default password status | Change immediately after deployment | Medium to high | Assess device by device |
| Admin account access | Limit to admin network and VPN | Medium | Review user lists quarterly |
| Password rotation | Rotate every 90-180 days | Medium | Policy-dependent |
| Audit logging | Enable and review logs | Medium | Use centralized SIEM if possible |
Your Questions Answered
Is there a universal default password for the bizhub C368?
No. Default passwords vary by firmware and region; always check official manuals and reset procedures. Treat any unchanged default as a security risk.
There is no universal default password. Check the official manual and reset procedures.
What should I do if I can't login after factory reset?
Follow the official reset steps and verify network configuration. If login remains impossible, contact IT or vendor support for a guided recovery.
If you cannot login after reset, follow the official steps and contact IT.
Can I enable two-factor authentication on bizhub C368?
Many MFPs do not natively support 2FA for the admin UI; check firmware features and vendor guidance for any available options.
Some models support extra protection; check the firmware features.
How often should admin passwords be rotated for MFPs?
Rotate passwords regularly—organizations commonly target every 90-180 days, depending on policy and risk exposure.
Rotate passwords every few months.
What are common password policies for printers?
Use long, unique passwords; avoid reuse; disable unused accounts and review permissions quarterly.
Use long, unique passwords and disable idle accounts.
Where can I find official reset procedures for bizhub devices?
Consult Konica Minolta’s official Bizhub C368 Administrator Guide and device manual; vendor support can assist with complex recoveries.
Check the official device manual or vendor support.
“Effective password hygiene for networked printers isn't optional—it's essential for preventing data leaks and unauthorized print access.”
Key Takeaways
- Change factory defaults immediately after setup.
- Use unique, strong passwords for admin access.
- Limit admin access to trusted networks and users.
- Regularly audit and rotate printer credentials.
- Document password changes and reset events promptly.