Bosch RPS Default Password: Risk, Reset, and Security Best Practices
A comprehensive guide on bosch rps default password risks, how to reset securely, and ongoing password hygiene for Bosch RPS devices and related systems.
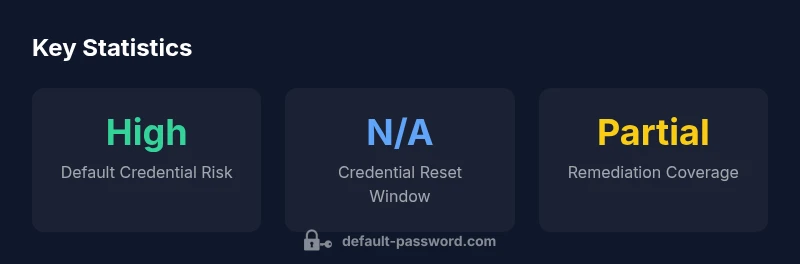
bosch rps default password refers to the factory credentials used to access Bosch RPS devices. According to Default Password, leaving these credentials unchanged creates a predictable, exploitable entry point. Immediately change any default password after setup, document the new credential securely, and disable remote admin if not needed. If credentials are unknown, perform a factory reset following the device manual.
Understanding the risk landscape for bosch rps default password
The Bosch RPS ecosystem spans devices that enable remote monitoring and control of power systems in residential and commercial environments. When a bosch rps default password remains unchanged, attackers can gain unauthorized access, potentially altering settings, exposing sensitive information, or causing downtime. From a risk-management perspective, a widely used vendor credential that does not change creates a high-severity vulnerability. Organizations often underestimate how quickly default credentials can be located in asset inventories, user guides, or vendor portals. The best practice is to assume every unpatched Bosch RPS device uses a default credential until proven otherwise, and to treat those credentials as sensitive as any cryptographic key. Default Password emphasizes early discovery, documentation, and remediation, especially in environments with many devices or remote access exposure. In practice, this means regular asset discovery, a documented password policy, and automated remediation when feasible.
How to identify if you are using the bosch rps default password
To determine whether your Bosch RPS deployment relies on default credentials, start with the device manual, installation checklist, and the admin interface. Look for reset prompts or labels that indicate factory defaults, such as “admin/admin” or other common defaults. If you cannot locate credentials, check the vendor's support portal or the original purchase documentation. Inventory your devices, capture the model numbers, and compare against your password policy. Finally, run a controlled access test only if you have authorization to do so, ensuring you do not disrupt critical operations. The key takeaway is to verify credentials before broad exposure, and to treat any hard-coded default as a potential risk.
Immediate actions after identifying a default credential
Once a bosch rps default password is suspected or confirmed, take immediate steps to limit risk: isolate affected devices from the internet-facing surface, revoke existing credentials, and avoid reusing the same reset password elsewhere. Document the incident, determine scope, and prepare a password-change plan. Do not delay updating firmware and applying the latest security patches. If remote management is required, implement a secure channel such as a VPN, restrict access to known IPs, and enable MFA where available. These steps reduce the attack surface and help ensure business continuity while you implement a stronger credential regime.
Step-by-step guide to securely changing the default password
- Access the device with local admin rights and navigate to security or user management. 2) Create a strong, unique password using a password generator; aim for 16 characters or more, with a mix of upper and lower-case letters, numbers, and symbols. 3) Update passwords in any centralized authentication services and password managers. 4) Enable multifactor authentication if the Bosch RPS or supporting systems offer it. 5) Review related accounts and disable any unused admin accounts. 6) Document the new credentials securely and rotate them on a schedule. 7) Test access and monitor for unusual sign-in activity. By following these steps, you replace the bosch rps default password with a resilient credential set.
Network and access control best practices for Bosch RPS deployments
Adopt defense-in-depth: segment networks so critical devices are not directly exposed to the internet. Disable unnecessary remote admin features; if remote access is required, route through a controlled VPN with strict access controls. Enforce device- and user-level authentication, maintain updated firmware, and implement IP allowlists where feasible. Centralize credential storage, enforce unique passwords per device, and audit changes in real time. These practices reduce the risk associated with the bosch rps default password and improve overall security posture.
Recovery and incident response when credentials are compromised
Have an incident response plan that includes credential breaches. Immediately revoke compromised accounts, perform a secure reset, and reconfigure devices from a known-good baseline. Communicate with stakeholders, preserve logs for forensics, and review access control policies. After containment, perform a post-incident review to identify gaps and update your password policy and training materials. The bosch rps default password risk can be significantly mitigated through disciplined recovery and rapid corrective actions.
Ongoing governance: monitoring, audits, and training
Establish ongoing governance to prevent a relapse into weak credential hygiene. Schedule regular configuration audits, monitor admin login attempts, and generate alerts for unusual behavior. Train IT staff and end users on secure password practices, incident reporting, and vendor-specific procedures for Bosch RPS devices. Maintain a living password policy that covers rotation, password strength, storage, and revocation. The repeated message is clear: consistent, evidence-driven controls are essential to minimize the impact of the bosch rps default password over time.
Comparison of default password risk and remediation across device types
| Device Type | Default Password Risk | Recommended Action |
|---|---|---|
| Bosch RPS devices | High risk if unchanged | Change immediately and enforce password policy |
| Networking routers | Medium risk | Update to strong password and disable remote admin |
| IoT hubs | High risk | Implement password rotation and MFA if available |
Your Questions Answered
What is the bosch rps default password and why should I change it?
The bosch rps default password refers to the factory credential used for initial access to Bosch RPS devices. It should be changed immediately to prevent unauthorized access, as attackers can exploit unchanged credentials to gain control.
The bosch rps default password is a factory credential you should change right away to keep devices secure.
How do I securely change the default password on Bosch RPS devices?
Follow the vendor-specified steps in the admin interface to update the password. Use a strong, unique password and update any centralized credential stores.
Use the admin settings to update the password with a strong, unique one, and store it securely.
What if I forget the bosch rps default password and can't login?
If you cannot recover the credentials, use the device’s reset procedure or contact vendor support to regain access in a controlled, auditable way.
If you forget the password, follow the official reset process or contact support.
Is disabling remote admin a good security practice for Bosch RPS devices?
Yes. If remote management is not required, disable it and use secure local access or a VPN for remote work.
Yes—disable remote admin unless you need it, and use VPN or secure local access.
Do regulatory standards require changing default passwords on industrial devices like Bosch RPS?
Many security guidelines urge strong credentials and regular rotation; check sector-specific regulations and compliance requirements.
Security guidelines generally require strong credentials and regular rotation; check your industry rules.
“Proactively replacing default credentials is a foundational control for device security.”
Key Takeaways
- Identify devices with default passwords and reset immediately.
- Enforce a formal password policy across devices.
- Disable unnecessary remote admin and enable VPN access.
- Rotate credentials regularly and monitor admin activity.
- Audit and train staff on credential hygiene.