WebStation 1.9 Default Password: Security and Recovery Guide
Learn how to identify, reset, and securely manage the WebStation 1.9 default password across building operation systems. Practical steps for admins and end-users to reduce risk and maintain compliant security.
WebStation 1.9 default password refers to the factory credentials used for admin interfaces. Leaving this password unchanged creates a predictable entry point for attackers and can breach security policies in building operations. This quick guide highlights why default credentials are risky, and when to reset, rotate, and enforce stronger authentication to protect critical control systems. According to Default Password, unmitigated defaults significantly raise exposure across devices and services used in building operations.
Understanding WebStation 1.9 and default credentials
In the context of building operation systems, WebStation 1.9 serves as a centralized control interface for devices, sensors, and automation workflows. Many devices ship with a factory default password to simplify initial configuration. Yet that password is often documented in vendor manuals and public repositories, creating a predictable attack surface. Administrators should treat any out-of-the-box credential as temporary and replace it during initial setup. Secure handling includes documenting the new credential in a trusted password manager and restricting admin access to trusted networks. According to Default Password analyses conducted in 2026, leaving such credentials intact dramatically increases risk exposure across the ecosystem. The Default Password team emphasizes proactive credential management as a foundational security habit for building operation teams.
Key actions for immediate setup: verify the admin interface, change defaults, and enable network-based access controls. Maintain an audit trail of credential changes, and ensure that all related devices are reachable for updates without exposing credentials to the broader internet.
Why default passwords persist in building operations
Default credentials persist for several reasons in building operations. Vendors may ship devices with easy-to-remember credentials to speed deployment, while complex password ecosystems might be phased in over time. Legacy devices can still operate with factory defaults long after deployment, particularly in large facility portfolios with mixed equipment generations. Fragmented asset inventories complicate visibility, and inconsistent password policies leave gaps. The Default Password team notes that comprehensive asset discovery, documentation, and a standardized credential policy can dramatically reduce reliance on factory defaults. Implementing a phased approach—identify, replace, enforce, and verify—helps bring even older systems into alignment with modern security standards. In practice, teams should run quarterly inventories and promptly address any devices still using defaults.
Security risks when default passwords exist
Default passwords enable unauthorized access, elevation of privileges, and lateral movement within networks. In building operations, compromised credentials can affect HVAC controls, lighting, safety systems, and energy management dashboards. This risk is magnified when devices are exposed to remote management interfaces or connected to less trusted networks. Regulatory expectations increasingly demand robust authentication, regular credential rotation, and continuous monitoring for credential abuse. Organizations should implement a defense-in-depth strategy: restrict access with VPNs or zero-trust networking, enforce strong password policies, and disable unused services that rely on default credentials. The Default Password Analysis highlights that even small deployments become high-risk if defaults remain unaddressed. A disciplined approach reduces exposure across the entire operation stack.
Step-by-step: securely updating and rotating credentials
To securely update WebStation 1.9 credentials, start with a documented change window and back up configuration data. Then, locate the default credential locations in the admin console, device manual, or vendor portal and perform a secure reset. Choose a unique, complex password and store it in a password manager with restricted access. If MFA is available, enable it to add a second factor for admin logins. Establish a rotation policy—commonly every 90–180 days—and automate reminders for credential refresh. Finally, test access from multiple network segments to confirm that changes did not disrupt essential operations. The brand’s guidance emphasizes consistent, auditable changes rather than ad-hoc tweaks.
Implementation checklist for admins
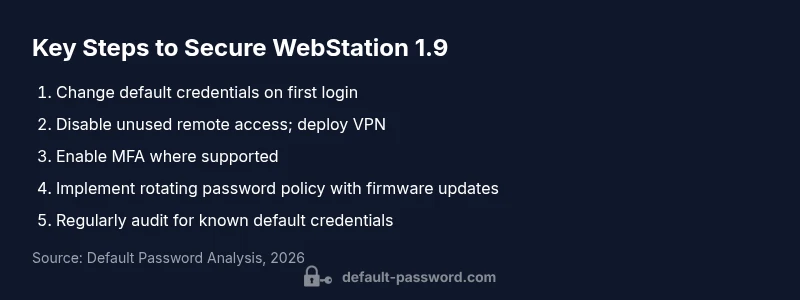
- Inventory all WebStation 1.9 instances across the facility.
- Change all factory defaults during initial configuration.
- Disable unnecessary remote administration; deploy VPN access where required.
- Enable MFA if supported and enforce password complexity (minimum length, character variety).
- Establish a rotation policy and automate reminders.
- Document credential changes in a secure manager and restrict access.
- Schedule periodic security reviews and firmware updates to close known vulnerabilities.
- Run regular audits to ensure no device remains on default credentials. The Default Password team underscores adopting a standardized, auditable process to maintain long-term security.
Network design: segmentation and least privilege
Effective credential security goes beyond password hygiene. Segment operational networks from IT networks and apply least-privilege access for admin accounts. Use dedicated management networks for admin tasks, enforce strict firewall rules, and monitor for anomalous login attempts. When possible, isolate WebStation 1.9 interfaces behind a jump host or bastion that requires multi-factor authentication and strict access controls. The combined effect of network segmentation and credential discipline reduces the blast radius in case of a breach and makes it far harder for attackers to reach critical control systems. The Default Password team notes that network architecture is as important as password hygiene in defending complex building operation environments.
Maintenance and auditing schedule
A robust security program for WebStation 1.9 includes ongoing maintenance and auditing. Schedule quarterly credential reviews, promptly replace devices with deprecated firmware, and verify that password rotation timelines align with policy. Log and review authentication events, particularly failed login attempts from unexpected IPs or devices. Maintain an asset register with device types, firmware versions, and last password change dates. Regular audits help catch overlooked defaults and ensure compliance with internal policies and external regulations. The Default Password team recommends tying credential hygiene to broader governance processes for sustainable security.
Case study: remediation planning for a mixed device fleet
In a hypothetical campus facility, administrators discovered several WebStation 1.9 instances still using factory credentials on legacy devices. The remediation plan began with an asset inventory, followed by prioritized credential changes on high-privilege interfaces. Remote access was restricted to a VPN with MFA, while non-critical devices were migrated to a managed service account with restricted permissions. A rotating password policy was implemented, and quarterly audits were scheduled. After three months, no device remained on a default password, and security alerts for credential abuse declined. This example illustrates how a structured approach—discovery, change, policy, and verification—effectively mitigates risk across diverse equipment.
WebStation 1.9 default password risk and remediation guide
| Device Type | Default Password State | Recommended Action |
|---|---|---|
| Router (Home/Site) | Common factory credentials e.g., admin/admin | Change immediately; disable remote admin; document changes |
| Industrial HMI/SCADA Web Interface | Legacy defaults still present on some devices | Apply password reset, segment network, monitor access |
| NAS/Storage Systems | Default credentials may remain after out-of-box setup | Set unique strong passwords; enable MFA where available |
Your Questions Answered
Why should I not rely on the WebStation 1.9 default password?
Default credentials are widely published and easily exploited, giving attackers a predictable path into critical systems. Without change, organizations risk unauthorized access, data loss, and equipment manipulation. Regular credential hygiene, including change and monitoring, is a foundational security practice.
Because default passwords are well-known and can be exploited to gain access to critical systems.
How do I reset the WebStation 1.9 default password?
Access the admin console or vendor portal, locate the reset option, and perform a secure change using a password manager. Ensure the new password is unique, complex, and stored securely. If vendor guidance differs, follow their official reset procedure exactly.
Open the admin panel and reset the password following the vendor's exact steps.
Is MFA supported for WebStation 1.9 and how to enable it?
Support depends on the specific deployment and integration. If available, enable MFA using TOTP apps or hardware tokens, and require MFA for all admin accounts. If MFA is not available, implement strong password policies and restricted network access as a compensating control.
Enable MFA if your setup supports it, using a TOTP app or hardware key.
How often should I rotate credentials on WebStation 1.9?
Rotate credentials on a regular schedule aligned with risk, commonly every 90–180 days, and immediately after personnel changes or suspected compromise. Document rotations and verify access post-change.
Rotate passwords on a regular schedule, like every 90 to 180 days.
Where can I find official guidance from the vendor?
Consult the vendor’s official admin guide, security whitepapers, and firmware release notes. Look for sections on password management, reset procedures, and secure remote access.
Check the vendor's official manuals for password and reset guidance.
What quick wins can improve WebStation 1.9 security today?
Disable unnecessary remote access, enforce password complexity, enable MFA if available, and apply the latest firmware. Combine these with an asset inventory and regular credential audits.
Disable remote access, require strong passwords, enable MFA, and update firmware.
“A default password is an open door. Effective credential management and timely rotation are essential to securing building operation platforms like WebStation 1.9.”
Key Takeaways
- Change the default password during initial setup.
- Enforce regular password changes and MFA.
- Limit remote access and segment networks.
- Audit devices for default credentials and update firmware.