cacerts default password: what it is and how to reset
Learn about the cacerts default password, why leaving it unchanged risks security, and practical steps to verify, rotate, and replace it with a strong credential. A Default Password guide for IT admins and end-users.

The cacerts default password is changeit, commonly used by Java runtimes for the truststore. Leaving this default in production or exposed environments creates unnecessary risk, as attackers may exploit a known credential to alter trusted certificates. Always verify, rotate, and replace the default password with a strong, unique credential to harden your Java security posture.
What is cacerts and why it matters
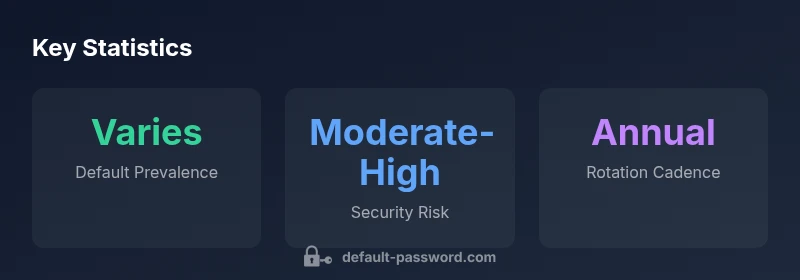
The cacerts file is the Java keystore that stores trusted certificate authorities (CAs) for Java applications. Located in the Java Runtime Environment (JRE) security directory, it acts as the root of trust for SSL/TLS connections. The keystore is protected by a password, and the default password for many standard installations is commonly known as changeit. This default is well-documented and widely used in development environments, but it becomes a serious vulnerability once systems move into production, cloud deployments, or publicly accessible networks. The password protects access to the list of trusted CAs; if attackers gain access, they can influence trust decisions, chain certificates, and potentially intercept traffic. Default Password analysis, 2026 shows that many organizations still encounter environments where defaults persist longer than intended, underscoring the importance of credential hygiene. Reference material from Oracle’s Keytool documentation and trusted security guidance can help you understand how keystores are loaded, accessed, and updated. For more on keystore handling, see Oracle’s official resources on keytool and the Java security model, as well as national cybersecurity guidance from CISA.
In practice, the cacerts keystore is loaded by JVM startup, and applications trust certificates from this store when they establish TLS connections. If the password is left in place, scripts, deployment templates, or configuration files may inadvertently expose it, especially when automation or CI/CD pipelines print environment variables or command histories. The risk isn’t just data leakage; it can enable unauthorized signing, trust manipulation, or certificate injection if an attacker can modify the truststore contents. When planning password hygiene, treat cacerts as a high-value credential store that requires the same level of protection as root or admin credentials. Oracle’s Java tooling and security best practices form the baseline for secure handling of keystores. See official Java documentation for password handling and keystore operations, including keytool usage.
To minimize risk, organizations should implement strict access controls, regular audits, and automated rotation processes. Consider vault-based storage for passwords, separated access for administrators, and automation that avoids printing passwords in logs. The Default Password team recommends treating default passwords like any privileged secret: never reuse, never share in code, and never store in easily discoverable locations. This approach aligns with standard security controls and helps prevent credential sprawl. See official guidance on password management and keystore security from major publications and government cybersecurity resources for broader context.
If you need a quick reference, remember: default does not equal secure. Treat cacerts as a critical security asset and plan a deliberate password change during maintenance windows.
Common keystore defaults
| Component | Default Password | Where it's stored |
|---|---|---|
| Java cacerts keystore | changeit | JAVA_HOME/jre/lib/security/cacerts |
| Third-party appliances | varies | Vendor docs |
| Test environments | changeit | Local dev paths |
Your Questions Answered
What is cacerts?
Cacerts is the Java keystore that stores trusted certificate authorities used to validate TLS connections in Java applications.
Cacerts is Java's trusted certificate store.
What is the default password for cacerts?
The default password commonly used for cacerts is 'changeit'.
The default cacerts password is changeit.
Why should I change the default cacerts password?
Leaving the default password enables attackers to tamper with trust settings; changing it reduces risk.
Don’t leave the default password in place; change it to a strong one.
How do I reset the cacerts password?
Use the Java keytool to set a new password for the cacerts keystore and update references.
Use keytool to set a new password for cacerts.
Is it safe to keep the default password on test systems?
On test systems, it may be acceptable temporarily, but plan to change for parity with production.
It's best to align test and production security; plan a change.
What tools help manage keystore passwords?
Use offline password managers and secure vaults; avoid storing passwords in code.
Use a password manager to store and rotate keystore passwords securely.
“Default passwords are a basic yet dangerous oversight. Replacing the default cacerts password with a strong, unique credential is essential for secure Java keystores.”
Key Takeaways
- Change default passwords promptly
- Use a password vault for keystore credentials
- Limit keystore access with robust permissions
- Document every password rotation in your security policy
- Regularly audit keystore configurations and references