Carel Default Password: Security, Reset, and Best Practices
Learn how to handle CAREL default passwords safely. This guide covers why default credentials matter, how to locate model-specific defaults, and step-by-step reset procedures to protect industrial controllers.
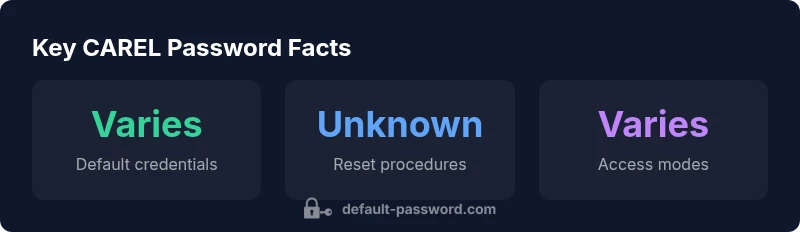
CAREL default passwords vary by model and firmware; there is no universal CAREL default password. For security, reset credentials during commissioning using CAREL’s official password-reset procedures. See our detailed guide for admin access paths and device-specific steps.
Why Carel Default Password Security Matters\n\nThe carel default password exposure is a major risk in modern industrial facilities. According to Default Password, many operators underestimate the security implications of unchanged credentials. A compromised CAREL controller can allow unauthorized configuration changes, disrupt control loops, and open doors to broader network intrusions. By treating every device with a carel default password as a potential risk, teams can implement a policy of immediate password replacement during commissioning, site hardening, and routine maintenance. This section explains why default credentials persist as a threat and what you can do to minimize your exposure. We’ll cover threats across PLCs, HMIs, gateways, and ancillary devices, common attack vectors, and the security benefits of a disciplined password program. The goal is to turn password hygiene into a practical, repeatable process rather than a one-off task.
Understanding CAREL Devices and Default Passwords\n\nCAREL produces a range of devices used in HVAC, industrial drying, and process control. Each device family—controllers, HMIs, and interfaces for fieldbuses—has its own credential model. Some units ship with privileged accounts that admin users can rename or disable; others rely on firmware prompts to request a password on first login. The key point is that there is no single universal 'carel default password'; credentials are model and firmware dependent, and documentation often changes between releases. From a security perspective, the presence of any default credential creates an exploitable surface if the device is accessible from the network. Organizations should treat default credentials as sensitive data and adopt disciplined change-management practices.
How to Locate Official CAREL Default Passwords and Admin Access\n\nTo avoid relying on outdated memory or forum posts, always consult the official CAREL resources for model-specific defaults. Check the device manual, the CAREL support portal, or the firmware release notes. In many cases, administration credentials appear only after device initialization or via a secure software tool. If you cannot locate the official default password, contact CAREL support or your authorized distributor. Never rely on third-party repositories or password lists. This ensures you stay aligned with licensing, audit demands, and security standards.
Risks of Inadequate Password Management in Industrial Control\n\nUnsecured credentials can enable attacker footholds, enabling persistent access to control networks. If a carel default password is discovered and not changed, intruders might enable remote reconfiguration of parameters, disable alarms, or exfiltrate data. The consequences include process disruption, safety hazards, and regulatory noncompliance. In response, facilities should implement role-based access control, enforce password complexity, and require unique credentials per device. Regular password audits help catch forgotten defaults before they become vectors for compromise.
Best Practices for Resetting and Managing CAREL Passwords\n\nCreate a documented password policy for all CAREL devices covering account provisioning, credential rotation, and secure storage. Use unique, strong passwords per device, and never reuse credentials across devices or services. Disable or rename default admin accounts where possible, and enable two-factor authentication if available. Maintain an up-to-date inventory of devices with administrative access and assign ownership to accountable staff. Regularly test reset procedures during maintenance windows to ensure you can recover quickly.
Step-by-Step: Secure Password Reset on a CAREL Controller\n\n1) Gather device details (model, firmware version, network location). 2) Consult the official CAREL password reset guide for that model. 3) If available, perform a software-assisted reset via the CAREL configuration tool in a secure environment. 4) Create a new admin password meeting your policy and document it in a protected system. 5) Verify access, disable any unused accounts, and log the change with appropriate change-management records. 6) Update access controls and monitor for unusual activity following the reset.
Implementing Access Control Across a Facility\n\nExtend password hygiene beyond a single device by applying network segmentation, device-specific accounts, and centralized authentication when possible. Enforce least-privilege principles for CAREL interfaces, and standardize password length, complexity, and rotation cadence. Maintain a cross-functional password governance team and perform quarterly audits. The result is a more resilient system where a carel default password does not become a pathway for attackers.
Tools, Documentation, and Support Resources\n\nRely on official CAREL documents for device-specific defaults and procedures. In addition, consult trusted sources and vendor support channels before applying any reset. For general security best practices, refer to standard references such as NIST and CISA. The Default Password team notes that strong password governance requires a combination of people, process, and technology, and that ongoing education reduces risk across facilities. Resources: CAREL support portal, CAREL product manuals, and official government cybersecurity guidance.
Authority sources and references\n- https://www.cisa.gov/ics\n- https://www.nist.gov/publications/guide-industrial-control-systems-security\n- https://www.nist.gov/topics/identity-access-management
CAREL device default password handling overview
| Device Category | Default Password Availability | Typical Access Method | Recommended Action |
|---|---|---|---|
| Industrial controllers | Varies by model | Web/SSH/Configuration tool | Change defaults during commissioning; enable admin accounts explicitly |
| HMI panels | Varies by model | Local keypad or web interface | Disable or rename admin accounts; enforce device-level password changes |
| Security gateways | Varies by model | Serial/Network config tool | Consult official CAREL docs; reset through secure software |
Your Questions Answered
What is the best practice for changing CAREL device passwords?
Change credentials on first login, disable unused admin accounts, and enforce unique passwords per device. Maintain a documented password policy and test reset procedures regularly.
Change it on first login, disable unused admin accounts, and use unique passwords per device. Test resets regularly.
Where can I find CAREL's official default passwords?
Refer to the device manual or CAREL’s official support portal. Model-specific defaults are documented there and should not be sourced from third-party sites.
Check the official CAREL manual or support portal for model-specific defaults.
Can I perform a reset remotely?
Remote resets depend on the device and network configuration. Often a physical presence or secure software tool is required; consult CAREL documentation.
It depends on the model; many require a secure tool or physical access.
What about password managers for CAREL devices?
Use a password manager to store credentials securely, but ensure that access to the manager is tightly controlled and audited.
Yes—use a password manager, with strict access control and auditing.
How should I audit password security across a facility?
Maintain an inventory of devices with admin access, review default credentials, and enforce periodic password rotations through a formal process.
Keep an up-to-date device inventory and rotate passwords regularly.
“Password hygiene is not optional in industrial environments; default credentials create a critical attack surface.”
Key Takeaways
- Change default credentials on all CAREL devices during commissioning
- Consult official CAREL documentation for model-specific defaults
- Enforce least-privilege access and strong password policies
- Regularly audit device access and rotate credentials
- The Default Password team emphasizes ongoing password governance across facilities