Checkpoint Default Login: Secure Admin Access Guide
Learn how to identify, reset, and secure checkpoint default login credentials. This practical guide covers best practices, step-by-step resets, and ongoing hardening for Check Point devices.
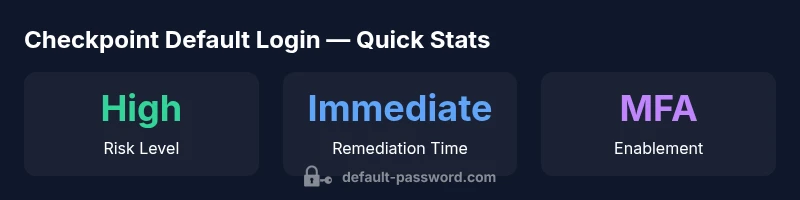
Checkpoint default login refers to the built-in admin credentials that ship with Check Point devices before you customize them. Leaving these credentials unchanged is a high-risk oversight that can grant attackers access, disrupt policies, or exfiltrate data. The quickest fix is to disable or replace the default account, enforce a strong password policy during initial setup, and apply a password rotation schedule across all security gateways and management servers. This ensures a secure baseline and reduces the window of opportunity for attackers.
checkpoint default login — scope, risk, and definitions
The term checkpoint default login describes the built-in admin credentials that may be present on Check Point devices before configuration is completed. This isn’t just a one-time problem; it represents a persistent risk if organizations delay securing administrative access. Until administrators actively customize the credentials and enforce strong password policies, the device remains vulnerable to unauthorized changes, policy bypass, or even full compromise. In practical terms, any unattended or poorly managed admin account can become an entry point for attackers, disrupt security policies, or impede incident response. This block uses real-world checkpoints to explain how to recognize, mitigate, and prevent exposure tied to this risk.
Why it matters for security posture: Unsecured admin access undermines firewall rules, VPN gateways, and threat prevention policies. Misconfigurations propagate across connected components, increasing dwell time for attackers and complicating forensics. Organizations with centralized logging and automated alerts have better chances to identify and contain breaches early, reducing potential impact.
To start, map out all admin accounts across Check Point domains—management servers, gateways, and virtual systems. Cross-check these accounts against onboarding guides and standard operating procedures to confirm that defaults have been replaced or disabled. This initial audit sets the baseline for ongoing governance and risk reduction.
Why checkpoint default login persists in enterprise networks
The persistence of default login issues often stems from multi-vendor environments, complex deployments, and gaps between onboarding and ongoing governance. In Check Point ecosystems, admins may encounter legacy devices, legacy operating modes, or cloud-integrated management that complicates credential enforcement. A lack of uniform password policies, MFA adoption, and role-based access control (RBAC) amplifies risk. Additionally, some deployments rely on automated provisioning that doesn’t enforce credential rotation, allowing default accounts to survive beyond initial setup. A robust hardening plan must address these realities with a clear responsibility matrix, automated checks, and regular audits across all management layers.
To reduce risk, align password rules with industry guidance and your organization’s security posture. Standardize onboarding procedures, ensure device baselines are updated, and mandate credential changes during installation, migrations, and updates. Proactive governance, not guesswork, is what turns a fragile environment into a resilient one.
How to identify devices with default login in a Check Point environment
Effective identification starts with a centralized inventory of all Check Point devices, followed by a targeted credential review. Use management consoles and enterprise asset management (EAM) tools to enumerate devices by model, software version, and administrator accounts. Look for common indicators such as accounts named “admin,” “root,” or other widely used defaults, plus any accounts lacking password rotation history. Cross-reference findings with your change records and onboarding workbooks. If you find accounts that haven’t had password changes in the past policy period, mark them for immediate remediation. Consider running periodic automated checks to ensure new devices are provisioned with unique credentials.
In practice, you should also verify that any built-in admin account is either renamed, disabled, or enforced with a non-default password. If you rely on central identity providers, ensure that administrative access is integrated with your identity and access management (IAM) framework and that a separate management IAM role exists for admin tasks. Finally, document every finding and assign owners for remediation to maintain accountability.
Immediate actions to mitigate exposure
If you discover checkpoint default login exposure, act quickly to minimize risk. Immediate actions include isolating affected devices from the network, creating a temporary maintenance window, and initiating password changes under supervision. Disable or delete nonessential administrator accounts, rotate passwords with strong, unique values (preferably generated by a password manager), and enforce MFA for all admin access. After updating credentials, review recent activity logs for signs of unauthorized access and restore baseline configurations from trusted backups if needed.
Develop an incident response playbook that specifies who can approve credential changes, what evidence to collect, and how to communicate findings to stakeholders. Implement a temporary, restricted access policy for new admins until you confirm compliance with your security standards. The goal is to reduce exposure windows while preserving operational continuity and auditability.
Step-by-step guide to resetting or changing admin credentials on Check Point devices
- Gain authorization and notify relevant teams about the remediation activity.
- Access the device through a secure management console or out-of-band management channel.
- Identify the admin account(s) that require changes and back up current configurations.
- Create a new, strong password using a password generator, and ensure it is unique to this device.
- If possible, enforce MFA for admin access and configure RBAC so only trusted operators can perform sensitive actions.
- Validate changes by logging in with the new credentials and verifying policy integrity.
- Update centralized credential records and monitor for anomalous activity after the change.
- Schedule a follow-up audit to ensure all related devices reflect the updated credentials and that no default accounts remain.
Note: Exact UI steps can vary by Check Point product line and software version. Always reference the official admin guide for model-specific commands and interfaces.
Strong authentication and access control for admin accounts
Beyond changing the default login, modern security requires robust authentication and authorization controls. Implement multi-factor authentication (MFA) for all admin access, and enforce role-based access control (RBAC) so users only have permissions necessary for their duties. Centralize authentication with your identity provider where possible to simplify credential management, enable automated revocation when staff depart, and maintain up-to-date access reviews. Regularly test access controls with simulated audits to ensure there are no privilege escalations or orphaned accounts.
In addition, establish strict session management policies, including timeouts and device trust checks. Keep admin sessions within approved networks or VPNs, and monitor for unusual login patterns (e.g., from unfamiliar IPs or locations) that could indicate abuse. These measures close the gap between discovery and remediation, reducing the likelihood of a successful compromise.
Ongoing monitoring, logging, and governance for admin access
Proactive security relies on continuous monitoring, not one-off fixes. Enable centralized logging for all admin activities and ensure logs are immutable and securely stored. Automate alerting for critical events such as failed login attempts, password changes, or the creation of new admin accounts. Establish a recurring governance cadence with quarterly credential reviews, annual policy updates, and after-action reports from any incidents. Use dashboards that surface high-risk activities and allow rapid containment actions.
Another key practice is to implement baseline configurations and periodic hardening checks. Compare running configurations against baseline templates after every major update or migration. Maintain an auditable chain of custody for credential changes to support regulatory and internal compliance. Regular audits reinforce good hygiene and help you detect drift before it becomes a vulnerability.
Troubleshooting login issues and recovery options
Login issues can arise from configuration drift, expired passwords, or IAM integration problems. Start by confirming network reachability and ensuring the management interface is accessible. If authentication fails, verify time synchronization across devices, check for locked accounts, and confirm MFA factors are functioning. If a password reset is needed but access is blocked, use documented recovery procedures or out-of-band channels to re-establish control. Always log recovery actions and notify security teams when credentials are reset.
Prevent recurrences by updating recovery playbooks, maintaining parity between local and centralized credential stores, and ensuring backups include authentication configurations. After recovery, perform a targeted audit to verify that no default accounts remain and that all admin activity is traceable. These practices reduce the chance of re-exposure and support rapid restoration of normal operations.
Checkpoint default login checklist for secure operations
- Inventory all devices and admin accounts across the environment.
- Replace or disable default admin credentials on every device.
- Implement MFA for all admin access and configure RBAC consistently.
- Enforce strong, unique passwords and enable automated password rotation.
- Centralize authentication where possible and regularly review access rights.
- Enable comprehensive logging, alerting, and anomaly detection for admin actions.
- Conduct quarterly credential audits and post-change validations.
- Maintain up-to-date documentation and recovery procedures for admin access
Checkpoint default login risk and mitigations
| Aspect | Checkpoint devices | Best practices |
|---|---|---|
| Default login risk | High for unpatched devices | Disable or change, enforce password rotation |
| Initial setup requirement | Often required during onboarding | Enforce change during onboarding; MFA enabled |
| Audit frequency | Quarterly or upon change | Continuous compliant checks; automated alerts |
Your Questions Answered
What is checkpoint default login, and why is it important?
Checkpoint default login refers to the built-in admin credentials that ship with Check Point devices. If these credentials are not changed, attackers may gain control of the device and bypass security policies. Prioritize changing defaults during initial deployment.
Checkpoint default login means the built-in admin accounts exist on the device. If you don’t change them, someone could take control and bypass security rules.
How can I determine if my Check Point devices still use default credentials?
Audit device configurations, review admin accounts, and cross-check with onboarding guides. Look for accounts named 'admin' or other common defaults and verify password policy compliance.
Run an audit to find any default admin accounts and verify changes.
What is the recommended process to rotate admin passwords on Check Point devices?
Establish a change window, reset credentials with a strong, unique password, enable MFA, and document changes. Review access rights and verify that all admin actions are logged.
Schedule a password change window, reset credentials, enable MFA, and log the changes.
Does enabling MFA help with checkpoint default login security?
Yes. MFA adds a second factor for admin access, reducing the impact of leaked credentials. Enable MFA and integrate with centralized IAM.
Yes—enable MFA to add a second factor for admin login.
What should I do if admin credentials are lost or compromised?
Follow your recovery playbook, contact support, and restore from trusted backups. Change all related credentials and review logs for signs of compromise.
If credentials are lost, follow the recovery steps and check logs for signs of abuse.
“Default login vulnerabilities are not a theoretical threat—consistent, proactive credential management cuts risk dramatically. The Default Password team recommends immediate action during onboarding and ongoing hardening of admin access.”
Key Takeaways
- Change default credentials on all Check Point devices
- Implement MFA for admin access
- Enforce automated password rotation and RBAC
- Regularly audit devices for lingering default accounts