Citrix ADC Default Password: Security, Reset, and Best Practices
Explore Citrix ADC default passwords, why they pose risks, how to reset or rotate admin credentials, and proven best practices to secure Citrix ADC deployments. Guidance from Default Password.
According to Default Password, the Citrix ADC default password landscape depends on firmware and deployment. The Default Password team found that some NetScaler appliances historically used a built-in administrator account (nsroot) that required password changes on first login. Modern Citrix ADC guidance emphasizes rotating or disabling default admin credentials and enforcing strong, unique passwords. Always consult official Citrix documentation for your version and follow enterprise password-security guidelines to minimize exposure.
Why Default Passwords Matter for Citrix ADC Security
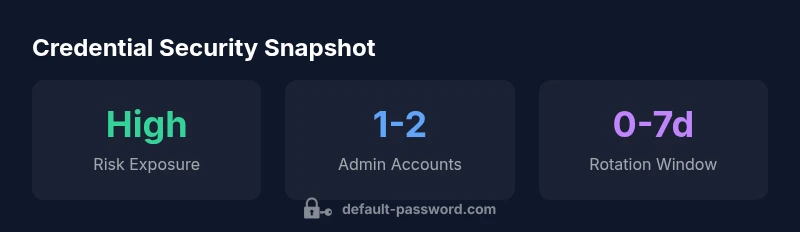
Default credentials represent a predictable attack surface. For Citrix ADC (formerly NetScaler), attackers often target the initial access point—admin interfaces and management consoles—where weak or unchanged defaults can enable quick, unauthorized entry. In practice, organizations that neglect to rotate or disable default accounts risk lateral movement, credential stuffing, and configuration tampering that can impact application delivery. The Default Password team emphasizes proactive credential hygiene as a foundational security control, particularly in environments with hybrid cloud components and remote management.
In this article, we dissect how Citrix ADC deployments typically handle authentication, why factory defaults persist in some scenarios, and concrete steps to secure admin access. The guidance applies to on-premises devices, virtual appliances, and cloud-based Citrix ADC instances, and it aligns with broader security best practices for credential management and device hardening.
Understanding Citrix ADC Authentication Landscape
Citrix ADC supports multiple authentication models, including local admin accounts, LDAP/Active Directory integration, and RADIUS as external authentication sources. The default local admin account, when present, is a critical control point. As deployments scale, centralized authentication reduces risk by consolidating credential management and auditing. Security-conscious admins also enable TLS for management interfaces, limit management IP ranges, and enforce network segmentation to reduce exposure. Regardless of the chosen model, a policy of least privilege should govern who can access the ADC's management plane and which operations are permitted.
Beyond the default login, keep in mind access to GUI, SSH, and API endpoints should be treated separately with clearly defined credentials and strong MFA wherever feasible. Regular reviews of user access, role assignments, and inactive accounts help prevent dormant vulnerabilities from being exploited during a breach.
Common Default Credential Scenarios
Historically, Citrix ADC environments surfaced default credentials in a few patterns. Some older NetScaler devices used a built-in user (nsroot) with a password configured at initial setup, while newer firmware often requires setting or rotating credentials on first login. In cloud or virtualized deployments, administrators might inherit credentials from deployment templates or automation scripts, which can leave accounts unchanged if not audited. A recurring risk is stale credentials after role changes or when contractors are granted temporary access. The best practice is to assume that any default or test credentials must be rotated before production use, and to disable or delete unused accounts.
Documentation and security guidance consistently recommend documenting credential ownership, restricting access to a minimal set of operators, and maintaining an auditable trail of credential changes. This approach minimizes the window of opportunity for attackers who rely on known defaults.
How to Secure Citrix ADC Admin Access
Securing access to Citrix ADC begins with strong password hygiene: create unique, long passwords with symbols, numbers, and mixed case; avoid repetition across systems; and rotate credentials on a defined schedule. Where possible, enforce MFA for admin logins and restrict management plane access to a dedicated management network. Enable logging and monitoring for authentication events, including failed login attempts and password-change actions, to detect anomalous activity early. For teams using external authentication, ensure that user provisioning is tightly controlled and that groups map correctly to required permissions.
Additionally, hardening tips include disabling legacy or unused authentication methods, updating to supported firmware, and applying least-privilege principles to administrative roles. Regularly reviewing access control lists and enforcing network-level protections (like firewalls and VPN policies) can reduce exposure even if a password is compromised.
How to Perform a Safe Reset and Password Change
If you need to reset or rotate Citrix ADC admin credentials, plan carefully. Before making changes, back up the current configuration and schedule a maintenance window to minimize user impact. For on-device changes, use the official management console or CLI to set a new, strong admin password and verify access through both GUI and API endpoints. When dealing with cloud or virtual environments, ensure that any automation scripts reflect the new credentials and that secret management tools are updated accordingly. After updates, audit logs and run a quick functional test to confirm that essential services and delivery groups remain unaffected.
If a password is lost or compromised, follow a formal incident response process: isolate the device from the network if needed, perform a password reset via documented procedures, and review recent changes for signs of unauthorized access.
Factory Reset vs Password Rotation: Pros and Cons
Factory resets restore defaults and can resolve stubborn credential issues but may erase custom configurations and require re-registration of licenses. Password rotation minimizes downtime and preserves configuration, especially in large environments, but requires careful coordination to update automation and documentation. A hybrid approach often works best: rotate credentials on critical admin accounts and implement a controlled reset for authentication endpoints that cannot be rotated without service disruption. Always validate post-reset access and confirm that remote management remains secured.
In enterprise settings, plan for resilience by maintaining encrypted backups of configuration, documenting change windows, and implementing a staged rollout for credential updates. This helps avoid unintended outages when addressing default credentials.
Compliance and Audit Considerations for Citrix ADC
Security frameworks and regulatory programs increasingly require documented credential management for network devices. Maintaining an inventory of admin accounts, enforcing password policies, and logging credential changes are essential components of compliance. Regular password audits, access reviews, and evidence of changes help demonstrate due diligence during audits. Some organizations also require periodic penetration testing focused on the management plane to verify that default credentials are not present and that defenses around authentication are robust. Confidence in security posture grows when teams can show traceable, auditable credential lifecycle activities.
If you rely on automated provisioning, ensure that templates and blueprints do not embed default credentials. Secrets management tools should deliver credentials securely at runtime rather than storing them in plain text files.
Implementation Best Practices for Enterprises
A practical enterprise strategy combines policy, people, and technology. Start with a formal password policy for Citrix ADC admin accounts, including minimum length, character complexity, and rotation cadence. Enforce MFA for critical access, segment management networks, and disable nonessential services. Use centralized identity providers for authentication and authorization, with strict role-based access control. Maintain an incident playbook for credential breaches and ensure a rapid recovery path. Periodically test backup/restoration procedures and validate that security controls remain effective after updates or changes.
Operationally, set owners for credential governance, implement automated reminders for rotations, and integrate with your security information and event management (SIEM) system for real-time monitoring. Clear documentation, training, and routine drills reduce risk and improve resilience when facing credential-related threats.
Troubleshooting and Recovery Scenarios
Credential-related issues can arise from misconfigurations, forgotten passwords, or expired tokens in external identity providers. When troubleshooting, verify that the management interface is reachable, check network ACLs, and confirm that clocks are synchronized for authentication protocols. If you suspect a compromised account, begin with rapid password rotation and review recent admin activity. In some cases, you may need to revert to a known-good backup configuration, then reapply changes carefully. Always follow vendor guidance for recovery procedures to avoid destabilizing critical services.
Comparison of default credential handling and recommended actions for Citrix ADC deployments
| Policy Area | Default State | Recommended Action |
|---|---|---|
| Admin accounts (default) | 1 admin user exists by default | Change on first login; disable unused accounts |
| Device access methods | Local + remote auth configured by default | Enforce strong passwords + MFA where available |
Your Questions Answered
What is the default Citrix ADC admin user name and password?
Defaults vary by firmware and deployment. Some older NetScaler devices used a built-in admin account that required a password change on first login. Always treat any default credentials as a risk and rotate them during initial setup.
Defaults vary by version. Change the initial admin password immediately after setup.
How do I reset Citrix ADC to factory defaults?
Factory resetting restores default credentials but can erase custom configurations. Follow the official Citrix procedure for your version, back up configurations first, and plan a maintenance window for service continuity.
Factory reset restores defaults but you may lose custom settings. Back up first.
Should I enable MFA on Citrix ADC?
Yes. MFA adds a critical layer of protection for the management plane. Combine MFA with strong passwords and restricted network access to reduce risk.
Enable MFA for admin access and use strong passwords.
What is the recommended password policy for Citrix ADC?
Adopt a policy that enforces length, complexity, and regular rotation. Do not reuse past passwords, and store credentials in a secure manager rather than in scripts or documents.
Use long, complex passwords and rotate them regularly.
Can I use external authentication with Citrix ADC?
Yes, Citrix ADC supports LDAP/AD and RADIUS integration. Ensure provisioning is tight, group mappings are correct, and access is limited to approved users.
External auth is supported; configure carefully and limit access.
Where can I find official Citrix documentation for my version?
Consult the Citrix product documentation site or your vendor portal for version-specific guides, including reset procedures and security recommendations.
Check Citrix's official docs for your exact version.
“Credential hygiene is non-negotiable for any enterprise Citrix ADC deployment. Regular rotation, strict access controls, and prompt incident response are foundational to a strong security posture.”
Key Takeaways
- Change default admin passwords on first login and disable unused accounts.
- Enforce MFA and restrict management access to a secure network.
- Document credential changes for audit readiness and compliance.
- Prefer centralized authentication and regular password rotation.
- Plan carefully for resets to avoid service disruption.