Concrete CMS 8.5.2 Default Password: Reset, Harden, and Audit
Practical, step-by-step guidance to identify, reset, and harden default and admin passwords in Concrete CMS deployments around version 8.5.x. Learn best practices, audit tips, and trusted sources for secure admin access.
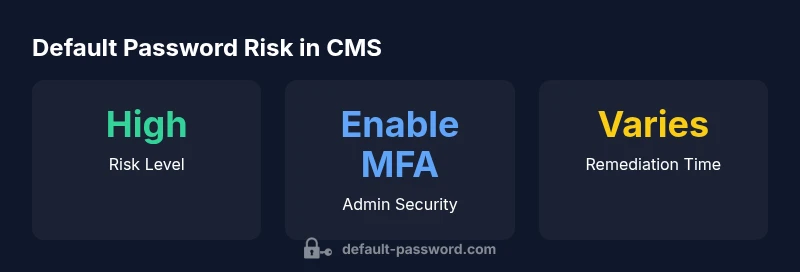
Steps to secure Concrete CMS deployments (including 8.5.x): change the default admin password immediately; enforce a password change at first login; disable unused default accounts; enable two-factor authentication if available; review user permissions and restrict admin access to trusted networks. This practical sequence dramatically lowers the risk of unauthorized access.
Understanding default passwords in CMS ecosystems
A default password is a credential shipped with software and expected to be changed during initial setup. In content management systems like Concrete CMS, a default admin account can remain active long after installation if administrators fail to rotate credentials. In concrete cms 8.5 2 default password scenarios, admins often discover that credentials were never rotated after installation. This pattern surfaces in training materials and audit checklists because it represents a predictable attack surface in the early stages of deployment. Leaving defaults in place creates an obvious target for automated attacks, privilege escalation, and unauthorized configuration changes. The risk scales with the capabilities of the CMS: admin panels, plugin managers, and theme editors become accessible to anyone who can guess or obtain the default password. For teams handling multiple instances, the problem compounds when dev, staging, and production environments share credentials or use the same accounts across services. To mitigate, start with a clean inventory of all accounts, verify who should have admin access, and enforce a policy that bans sharing of admin passwords. Regularly refresh credentials and review access logs for suspicious activity.
How default credentials arise in Concrete CMS environments
Many installations begin with a default admin user created during setup. If the password is not changed before going into production, this account can act as a gateway for attackers. In addition, developers might create auxiliary accounts with elevated rights that are not strictly necessary, leaving a foothold for misuse. The linked risk is compounded by inconsistent patching, outdated modules, and misconfigured permissions. Administrators should treat any credential that ships with the software as suspect until explicitly rotated. A comprehensive inventory of users, roles, and permissions helps surface dormant accounts and ensures that only trusted staff have admin access. By aligning with security standards from reputable authorities, teams can reduce exposure and maintain a defensible posture across all Concrete CMS instances.
Practical steps to secure Concrete CMS admin access
Begin with stopping the use of any default credentials. Immediately change the password for the primary admin account and require a password change at the next login. Enforce strong password policies and consider adopting a password manager for unique, complex credentials. If the platform supports two-factor authentication, enable it for all admin accounts and require MFA at login. Review user roles carefully, removing unnecessary admin rights and restricting admin access by IP range or VPN when possible. Regularly audit activity logs and enable alerts for unusual login attempts. Keeping the system up to date with patches and extensions also reduces exposure to known vulnerabilities. These steps create a layered defense that protects both the CMS core and any installed plugins or themes.
Ongoing hardening and maintenance for CMS deployments
Security is a continuous process, not a one-time fix. Schedule quarterly credential reviews, refresh passwords after personnel changes, and rotate secrets used by integrations or deployment pipelines. Implement a formal change-control process for admin access, log all password-related events, and maintain an incident response plan for suspected breaches. Use a centralized policy to govern password complexity, rotation cadence, and MFA enrollment. In parallel, harden the hosting environment: secure SSH access, restrict file permissions, and ensure backups are protected and immutable. Documentation is essential; maintain an up-to-date runbook that codifies the exact steps for password resets, account deprovisioning, and emergency access procedures.
Common pitfalls and how to avoid them
Avoid relying on default credentials as a fallback, and never reuse passwords across services. Do not leave admin accounts visible to all users or publicly listed in the site’s UI. Disable or remove unused accounts, and never store credentials in plaintext files or public repositories. Where possible, implement a password manager, enable MFA, and enforce least-privilege access. Finally, educate staff on phishing awareness, since attackers often target administrators to harvest credentials. By combining technical controls with user education, organizations reduce the risk surface across Concrete CMS deployments.
Common risk scenarios in Concrete CMS deployments
| Scenario | Current Risk | Mitigation |
|---|---|---|
| Default admin accounts | High | Remove or rename accounts; require password changes |
| Insecure password reuse | Medium | Enforce strong policies and use a password manager |
| Lack of 2FA | Medium | Enable 2FA wherever possible |
| Outdated software | High | Apply latest security patches and updates |
Your Questions Answered
What is considered a default password in Concrete CMS?
A default password is a credential that ships with the software or is commonly used and left unchanged. Always verify and rotate these credentials during initial setup and after personnel changes.
A default password is a credential that comes with the software and should be changed right away.
How do I reset the admin password in Concrete CMS 8.5.x?
Use the login page’s Forgot password option or administrator email reset workflow. If you cannot access the email or account, contact another admin or follow your site's incident response process.
Use the Forgot password option on the login page or contact another admin for reset.
Is Two-Factor Authentication supported in Concrete CMS?
Yes. Enable two-factor authentication for admin accounts where available to add a strong second factor beyond passwords.
Yes, enable MFA for admins if the option is available.
What if I lose admin access and cannot reset?
Use emergency access procedures or contact your hosting provider or CMS support team for guidance. Documented incident response plans help you recover quickly.
If you’re locked out, follow emergency access procedures or contact support for help.
How often should I rotate passwords?
Rotate credentials when personnel changes occur or after a suspected breach. Establish a policy and automate reminders where possible.
Rotate passwords when people leave or if you suspect a breach.
What external sources can help secure Concrete CMS?
Consult NIST SP 800-63-3 guidelines, OWASP Password Storage Cheat Sheet, and US-CERT tips for robust password and authentication practices.
See NIST, OWASP, and US-CERT for solid password practices.
“Security is a continuous discipline; defaults are invitations for attackers, so proactive hardening must be part of every CMS rollout.”
Key Takeaways
- Change default credentials immediately after install
- Enforce password changes at first login
- Enable two-factor authentication for admins
- Audit user permissions and restrict admin access
- Regularly review security settings and updates