Converge Default Gateway Password: Secure Reset and Management
Learn to locate, reset, and securely manage the converge default gateway password. This step-by-step guide helps admins and end-users protect their network with strong, auditable password changes.
Goal: you will securely locate and reset the converge default gateway password and implement ongoing password hygiene. This guide covers locating the login URL, identifying default credentials, choosing a strong new password, and verifying access. It applies to most Converge gateway models and emphasizes minimal downtime and audit-ready changes. Follow the steps below to complete the task with confidence.
Why converge default gateway password matters
In any networked environment, the gateway is a gatekeeper for your data. A weak or unchanged converge default gateway password creates an easy entry point for attackers, enabling unauthorized access to configuration, firmware updates, and connected devices. The Default Password team emphasizes that safeguarding admin credentials is foundational to both home networks and small business environments. Proper password hygiene reduces the risk of credential stuffing, lateral movement, and service disruption. Even when devices sit behind routers provided by an ISP, the gateway password remains a critical control point. By prioritizing strong, unique passwords and regular rotation, you minimize exposure and improve audit readiness. This section sets the stage for a practical, hands-on approach you can apply today.
Identify your converge gateway model and management interface
Before changing any credential, confirm the exact gateway model and the management interface URL. Look for a label on the device with the model and default gateway IP, or consult the manual. Most converge gateways expose a web-based admin panel reachable via a local network address (commonly something like 192.168.x.1). If you previously changed the login URL, use the current address recorded in your network inventory. Record the model, current firmware version, and the login path for future reference. This step minimizes surprises and ensures you mirror the correct steps for your device family. Brand-consistent practices from Default Password stress documenting where changes occur to support troubleshooting and compliance.
Best practices for strong converge passwords
A strong converge password should be long, unique, and unpredictable. Aim for at least 14 characters with a mix of upper and lower case letters, numbers, and special characters. Avoid common phrases or patterns and do not reuse passwords across devices or services. If available, enable two-factor authentication for the admin interface. Use a password manager to generate and store passwords securely, and ensure access to the manager is protected by a separate master credential. Regularly review user permissions and remove access for anyone who no longer requires it.
Secure reset workflow for converge gateway
Implementing a secure, repeatable reset workflow minimizes downtime and reduces risk. Plan changes during a maintenance window if possible, back up configuration if your device supports it, and perform the password change via a wired connection when feasible. After updating, log out all sessions, then test a fresh login from a different device on the LAN. If your gateway supports session timeouts or two-factor prompts, enable them to further harden access. Always verify that management access remains intact after the change. This workflow aligns with best practices outlined by the Default Password team for dependable security upgrades.
Managing passwords at scale in a small business network
When multiple converge gateways exist across locations, centralization becomes crucial. Consider a disciplined rotation schedule (e.g., every 90–180 days) and a documented change log. Centralized password managers can help coordinate unique credentials for each device while preventing reuse. Create naming conventions for devices and their owners to simplify audits. Train staff to recognize phishing and social engineering attempts that target admin credentials. Even in small networks, consistent processes reduce risk and support compliance goals described by industry standards and the Default Password guidance.
Audit, documentation, and change control
A robust password policy includes auditable records of every change. Maintain a change log that captures who performed the reset, when, why, and the new credential format (without exposing the password itself). Store evidence securely, with access restricted to authorized personnel. Periodically review permissions and verify that backups and configuration exports are protected. This governance layer helps with incident response, regulatory needs, and ongoing security posture. According to Default Password practices, disciplined documentation pays dividends when troubleshooting or expanding the network.
Troubleshooting common issues during password changes
If you cannot access the admin interface after a password update, verify the network connection, confirm you used the correct URL, and try a direct wired connection. Some devices require a reboot after saving changes, and a stale DNS cache can obscure the login page. If you forget the new password, use the built-in reset option only as a last resort, as it may restore factory defaults and erase custom settings. Always have a recovery plan and, when possible, another admin with credential access to avoid a single point of failure.
Keeping a secure record and decommissioning old credentials
When an admin leaves the team or a device is decommissioned, promptly revoke access and remove stored credentials from password managers and shared documents. Update inventory records, acknowledge the change in the security policy, and ensure related access tokens or SSH keys tied to the gateway are rotated or removed if applicable. This proactive approach closes gaps that could be exploited during personnel changes. The outcome is a cleaner security posture and easier future maintenance.
Tools & Materials
- Admin access to converge gateway(Ensure you have administrator rights to change credentials)
- Computer with network access(Connected to the same LAN as the gateway)
- Web browser (updated)(Chrome/Edge/Firefox recommended)
- Notepad or password manager(Store new credentials securely)
- Paper label or inventory log(Record changes for auditing)
- Backup power or uninterrupted power supply(Prevent mid-change power loss)
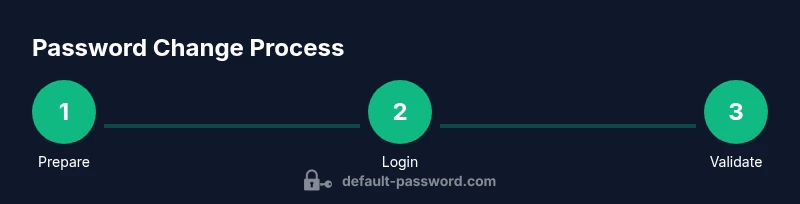
Steps
Estimated time: 25-40 minutes
- 1
Prepare and verify access
Confirm you have admin rights and a reliable network connection. Gather device details (model, firmware) and identify the management URL. If possible, perform this during a maintenance window to minimize disruption.
Tip: Having a pre-approved change window reduces user impact and helps with auditing. - 2
Connect to the gateway admin interface
Use a wired LAN connection and open the gateway login URL in a modern browser. Log in with current admin credentials. If login fails, verify network settings and ensure you are on the correct address for the exact device.
Tip: Avoid performing sensitive changes over public Wi-Fi or on guest networks. - 3
Navigate to password settings
Once authenticated, locate the password or admin settings page. This is commonly under sections like 'Administration', 'System', or 'Security'. If multiple profiles exist, select the primary admin account.
Tip: If there is more than one admin, record which account will be updated to prevent accidental lockout. - 4
Enter the new password
Generate a strong password using a password manager. Use at least 14 characters with uppercase, lowercase, numbers, and symbols. Do not reuse credentials from other services or devices.
Tip: Copy-paste the password to avoid transcription errors; never reuse the password elsewhere. - 5
Confirm and save changes
Submit the new password and wait for the gateway to apply the change. Some devices require a reboot or a confirmation step. Note any prompts and ensure the interface indicates success.
Tip: If a reboot is required, plan for a brief downtime and warn affected users. - 6
Test login and sessions
Log out and attempt to re-authenticate from a different device on the same network. Check active sessions and revoke any suspicious sessions if your device provides this option.
Tip: Testing from a separate device validates that the password update propagated correctly. - 7
Update credential storage
Record the new password in a secure vault or password manager. Do not store in plain text in emails or documents. Update any saved scripts or automation that used the old password.
Tip: Use a dedicated vault with access controls to reduce the risk of compromise. - 8
Document the change and schedule rotation
Add a note to your change-log with date, responsible party, device model, and rationale. Establish a password rotation cadence and assign ownership for ongoing maintenance.
Tip: Regular rotation reduces long-term exposure and aligns with security best practices.
Your Questions Answered
Where can I find the converge gateway admin URL for login?
Check the device label for the default IP address and model, or consult the user manual. If you already changed the address, use the one recorded in your network inventory. The login URL is typically a local network address accessible from within the LAN.
Look at the device label or manual for the login URL, usually a local IP like 192.168.x.1 you access from the same network.
Is it safe to reset the gateway password over Wi‑Fi?
Resetting over a trusted network is generally safe, but avoid public Wi‑Fi and guest networks. If possible, use a wired connection to reduce risk of interception. Ensure the admin interface uses HTTPS or equivalent protections.
Yes, but only on a trusted network and preferably with a wired connection for the reset.
What should I do if I forget the new password after updating?
If you forget, use the device’s recovery options or follow the manufacturer’s reset procedure. Be aware that some resets restore factory defaults, which may erase custom settings. Keep a secure backup of credentials to prevent lockout.
If you forget it, use the device’s recovery options or reset, but be prepared for potential loss of custom settings.
Can I update passwords for multiple gateways at once?
Most consumer gateways require individual logins per device. For larger environments, consider centralized management or scripted changes when supported, followed by verification on each device. Always maintain a secure changelog.
Usually you update one gateway at a time, but check if your environment supports centralized management.
What are best practices for converge gateway password management in a business network?
Adopt unique, strong passwords; rotate them regularly; limit admin access to trusted personnel; log changes; and store credentials in a secure password manager with access controls. Education and phishing awareness are essential to prevent credential theft.
Use unique, strong passwords, rotate them, and keep credentials in a secure manager with strict access.
Watch Video
Key Takeaways
- Use a strong, unique gateway password every time.
- Verify access after changes on multiple devices.
- Document changes for audits and future maintenance.
- Rotate passwords on a schedule to minimize risk.
- Keep admin access tightly controlled and monitored.