CyberPower Default Passwords: A Practical Guide for Securing UPS Devices
Learn how to identify, reset, and manage default passwords on CyberPower UPS devices. A practical guide for end-users and IT admins to secure admin access.
CyberPower UPS devices often ship with default login credentials, creating an immediate security risk if left unchanged. The quickest mitigation is to locate the default password for your model, reset it to a strong, unique value, and enforce regular password changes for all admin accounts. This guide covers generic reset steps, interface-specific methods, and best practices for hardening CyberPower admin access.
The risk of leaving cyberpower default password unchanged
Leaving a default password in place on CyberPower UPS devices is a conspicuous risk vector. Admin interfaces — whether accessed through a web GUI, a local console, or a remote management portal — can become gateways for unauthorized control if credentials are not updated. In practice, many deployments overlook this step during initial setup, assuming the device is isolated or managed by a small team. However, the reality is that default credentials are a common target for automated scans and opportunistic attackers. The consequences can range from subtle configuration changes to full takeover of power-management features, potentially disrupting critical services, provisioning schedules, or even enabling a foothold into connected networks. Organizations of all sizes should treat credential hardening as a first-priority security control and embed it into onboarding checklists, asset inventories, and change-management processes. The best defense is a documented password policy applied consistently across every CyberPower device and firmware version in use.
In addition to changing the password, administrators should verify that any remote management features are only accessible from trusted networks or via VPN, and that admin accounts are audited for unusual activity. A misconfigured UPS can be a blind spot in a security program, so it’s essential to pair password hygiene with device-hardening practices and routine firmware updates.
CyberPower device families and where credentials live
CyberPower produces a range of power protection devices, including uninterruptible power supplies (UPS), network-grade power distribution units, and management cards. Each product family provides its own administrative entry point, documentation, and credential lifecycle. Credentials are typically configured through the web interface (GUI) or, in some models, via a console/CLI or a dedicated management card. For enterprise deployments, credentials may also be linked to centralized identity providers, depending on the device’s capabilities and firmware. Regardless of the model, the credential lifecycle follows a common pattern: (1) locate the default login, (2) create a strong admin password, (3) rotate and revoke unused accounts, and (4) monitor access attempts. Understanding where to look in your specific model helps prevent misconfigurations during initial setup and later maintenance.
Finding the default password for your model
To locate the default password for a CyberPower device, start with the model documentation that came with the unit or the official CyberPower support site. If the documentation is not readily available, check physical labels on the device for default credentials or the admin interface’s login screen, which often documents the initial username and password. For devices with network management cards or integrated web interfaces, search for the model number in conjunction with terms like “default password” or “admin login.” Where a persistent default password is provided by the vendor, it may be model-specific and firmware-dependent. If a password is not visible, assume there is a predefined credential and proceed to reset as a precaution. Always ensure you have access to the management console or recovery options before attempting changes.
Resetting or changing the default password
Resetting or changing the default password typically involves these general steps, though exact menus may differ by model:
- Log in to the web GUI or console with the current credentials.
- Navigate to the Admin or User Management section.
- Select the admin account and choose to change the password.
- Enter a new strong password that meets your organization’s policy (length, complexity, and history requirements).
- Save the changes and log out, then log back in with the new password to verify.
If the device supports SSH/CLI, you may also reset passwords through command-line commands, but this option is model-dependent. After updating, enable audit logging and restrict access to trusted IPs or VPNs. Keep firmware up to date to ensure compatibility with stronger authentication methods.
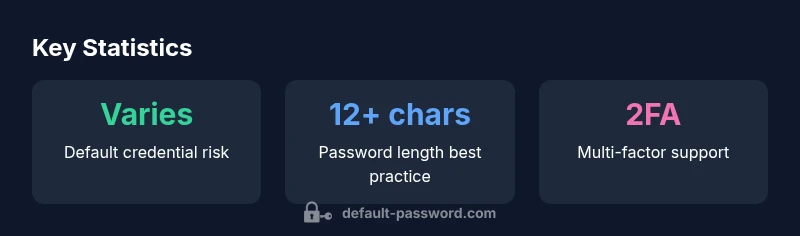
Practical hardening steps you can implement today
- Change default credentials immediately after setup and ensure all admin accounts use unique, non-default passwords.
- Enforce a password policy with minimum length (at least 12 characters), complexity, and rotation requirements.
- Disable remote admin access unless it is strictly necessary and protected by a VPN or IP allowlist.
- Enable multi-factor authentication (MFA) if supported by the device or management interface.
- Regularly update firmware and review security advisories for CyberPower devices.
- Maintain an up-to-date inventory of all CyberPower devices and check that each entry has a refreshed password after deployment or maintenance. -centralize password management through a dedicated tool when supported by the device ecosystem to avoid reused credentials across devices.
Example workflow for a new CyberPower deployment
- Inventory the devices and document model numbers and firmware versions.
- Review the default credentials in the vendor docs and prepare a secure password policy.
- Change all admin passwords during onboarding and enable MFA if possible.
- Disable unnecessary remote admin features and configure VPN-only access for remote management.
- Apply firmware updates to all devices and verify the changes with test logins.
- Create a password-rotation schedule and assign owners for ongoing governance.
- Monitor login events and set up alerting for failed attempts.
- Document the process and review annually for improvements.
Policy considerations for IT admins and security teams
From an organizational perspective, password hygiene should be integrated into security governance. Establish a formal policy that defines password length, complexity, rotation frequency, and the process for revoking access when personnel change roles. Align CyberPower device management with overall identity and access management (IAM) controls, including least-privilege access and network segmentation. Regular training and awareness for admins help reduce risky behaviors, such as writing passwords on sticky notes or sharing credentials. Automate credential-change workflows where possible, and require regular firmware reviews to benefit from security enhancements. A clear policy reduces the likelihood of inconsistent practices across devices and teams and supports compliance with broader cybersecurity standards.
Troubleshooting common issues and maintenance tips
- If you cannot log in after changing the password, use the device’s recovery options or factory reset only as a last resort, following vendor guidance.
- Ensure that the new password is saved in the correct location and that the device’s time is synchronized to avoid authentication issues related to time-based controls.
- Verify that your management interface is reachable only from trusted networks; misconfigured firewalls can block legitimate admin access.
- If multi-factor authentication is available, verify that MFA enrollment is functioning properly and backup codes are securely stored.
- Keep a change log and maintain a backup of configurations to minimize downtime if a password needs to be reset again in the future.
Authoritative sources and next steps
For authoritative guidance on password security, refer to standards such as NIST SP 800-63 and related cybersecurity best-practice resources. Industry bodies and government agencies provide foundational principles that apply to device management, including password hygiene, identity assurance, and secure configuration baselines. Always consult the official CyberPower documentation for model-specific instructions and keep abreast of firmware advisories.
Sources and further reading (example)
- CyberPower official manuals and support pages for your model
- NIST SP 800-63 Digital Identity Guidelines (https://www.nist.gov/publications/sp-800-63-3-digital-identity-guidelines)
- Cybersecurity and Infrastructure Security Agency (CISA) password hygiene resources (https://www.cisa.gov)
- Federal trade commission guidance on passwords (https://www.consumer.ftc.gov/articles/passwords-are-not-just-letters)
CyberPower default credential landscape
| Aspect | Default Credential State | Recommended Action |
|---|---|---|
| Web GUI Access | Common defaults like admin/admin or user/password; varies by model | Change during initial setup; verify password policy |
| Remote Access | Often enabled by default on some models | Disable if not required; enable VPN or IP whitelisting |
| CLI/SSH | Optional on some models | Disable or require keys or strong passwords if enabled |
Your Questions Answered
What is the default username on CyberPower devices?
The default username varies by model and firmware. Always check the device documentation or admin login page for the exact value and proceed to change it during onboarding.
The default username can vary by model; check the manual and change it during setup.
How do I reset the CyberPower admin password?
Access the device’s web GUI or console, navigate to Admin or User Management, and follow the reset or change password option. Save changes and test by logging in with the new credentials.
Go to Admin settings, choose change password, save, and test the new credentials.
What if I forget the administrator password?
Most CyberPower devices offer a password recovery option or recovery via support. If recovery is unavailable, a factory reset may be required, following official instructions.
Use the device’s recovery option or contact support; factory reset is a last resort.
Does CyberPower support two-factor authentication on admin interfaces?
Some models support MFA or two-factor methods for admin access. If available, enable MFA and store backup codes securely.
Check your model’s capabilities and enable MFA if offered.
How often should I rotate CyberPower admin passwords?
Adopt a rotation schedule aligned with your security policy, typically annually or after personnel changes. Maintain logs and enforce reuse restrictions.
Rotations annually or after staff changes, with no reuse.
Where can I find official CyberPower password guidance?
Refer to the model-specific manual and CyberPower support pages. For general guidance, consult reputable cybersecurity standards like NIST SP 800-63.
Check the official manuals and trusted cybersecurity references.
“Default passwords are the single most overlooked risk in power-management devices; changing defaults and enforcing strong admin access is foundational to security.”
Key Takeaways
- Change default credentials immediately after setup
- Enforce a strong, unique password policy across all admin accounts
- Disable or restrict remote admin unless protected by VPN
- Enable MFA where supported and keep firmware updated
- Document and enforce password rotation and access controls