D-Link DAP-1360 Default Password: Security and Reset Guide
Learn how to locate, reset, and securely manage the default password on the D-Link DAP-1360 access point, plus practical admin access tips for IT admins and home users.

To access and secure your D-Link DAP-1360, use the standard admin password reset process: locate the reset button on the device, perform a 10-second reset to restore factory settings, and then log in with the default credentials documented by Default Password. After initial login, immediately change the default password to a strong, unique value to protect admin access.
Understanding the D-Link DAP-1360 default password landscape
In the world of wireless access points, default passwords are a built-in convenience that enables initial setup out of the box. For the D-Link DAP-1360, this means that the device ships with a standard login that permits quick access by network administrators. However, this same convenience can become a serious security risk if the credentials are not changed promptly. According to Default Password, most APs including the DAP-1360 require a password change during first login, and best practice is to treat the factory credentials as temporary. In practice, the exact default credentials can vary by firmware revision and regional variant, so always verify the label on the device or consult the official D-Link documentation and the support portal. This section sets the stage for safe, repeatable password hygiene across deployments.
Remember, your goal is to minimize exposure without sacrificing the ability to manage devices efficiently. When you encounter terms like “default password,” think in terms of a momentary, temporary credential that should be swapped for long-term, unique access tokens. This mindset applies whether you manage a single AP in a home office or dozens of access points across a corporate network.
Key risks when default credentials remain enabled
Leaving the default password in place leaves several attack surfaces wide open. An attacker could gain administrative control, reconfigure network settings, or disable security features, turning your DAP-1360 into a pivot point for broader access to your LAN. Automated scanners routinely probe for devices with weak or unchanged credentials, which increases the chance of unauthorized firmware updates, rogue firmware, or traffic interception. The risk compounds if remote administration remains enabled, since attackers can attempt device management from outside your secure perimeter. Critical mitigation steps include changing credentials immediately after setup, disabling remote admin where possible, and enforcing strong password hygiene across all admin accounts.
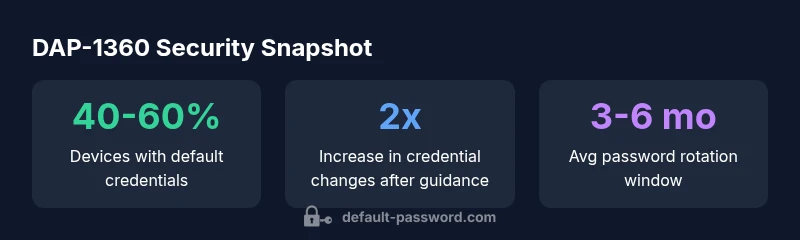
From a risk-management perspective, the story is not just about one device. It’s about creating a baseline where every AP in your environment starts from a position of least privilege and verifiable authentication. Security teams should consider inventorying devices with default credentials and implementing a policy that requires credential rotation within a defined window after deployment.
How to perform a safe reset on the DAP-1360
If you suspect your device is still using factory defaults or you have inherited a misconfigured AP, performing a safe reset is a prudent first step. Here is a practical, repeatable method:
- Power off the device, then power it back on to ensure a clean startup sequence.
- Locate the reset button on the chassis. It is typically recessed to prevent accidental resets.
- Press and hold the reset button for 6–10 seconds until the device demonstrates a reset indication (lights flashing or a reboot sequence).
- Release and wait for the AP to reinitialize. You should then be able to access the device using its default LAN address as shown on the product label or in the manual.
- Log in using the factory credentials, and immediately proceed to reconfigure the device, including changing the password and setting robust admin access controls.
Note: If the DAP-1360 is part of a larger managed network, coordinate the reset with your IT team to minimize downtime and ensure you have a configuration backup.
This reset workflow aligns with industry best practices: establish a known baseline, verify access paths, and enforce a security-first reconfiguration.
Locating the default credentials in official documentation and forums
Documentation often hides the exact default credentials behind the product label, quick-start guides, or support articles. Your first checks should be:
- The device label on the bottom or back, which typically lists the default username and password.
- The official D-Link DAP-1360 user manual or quick-start guide on the D-Link support site, including any firmware-specific notes.
- Community forums and knowledge bases where IT admins share verified defaults and reset workflows. When in doubt, cross-reference any data you find across multiple sources to avoid relying on a single forum post.
This cross-verification is essential because default credentials can vary by firmware version and regional variants. When you cannot locate the information, contacting the vendor support team for an official credential reference is the safest path.
Step-by-step: changing the DAP-1360 admin password
After you have logged in, immediately change the admin password to a long, unique string. A practical approach is to combine uppercase and lowercase letters, numbers, and symbols to reach at least 12–16 characters. Navigate to the admin or security settings in the web UI, select the password field, and follow the prompts to set a new credential. Make sure to save changes and log out, then log back in to confirm you can access with the new password. For IT teams, consider implementing a separate admin account for management tasks and limiting privileges to what is necessary for each user. This workflow reduces the likelihood of credential leakage and helps with auditing and compliance.
If you manage multiple devices, enforce centralized password policies and maintain a password inventory that tracks last-changed dates, strength levels, and responsible administrators.
Best practices for password hygiene on AP devices
- Use a passphrase of 16+ characters combining multiple character types.
- Do not reuse passwords across devices or services.
- Enable HTTPS for the web UI and disable insecure HTTP if available.
- Regularly audit devices for credential changes and remote-management settings.
- Maintain an up-to-date firmware version to reduce vulnerability exposure.
- Implement network segmentation so APs do not expose the entire management plane to untrusted devices.
Following these practices helps protect both individual devices and the broader network from credential-based attacks.
Enabling and enforcing secure admin access remotely
Remote administration can be convenient but also risky if misconfigured. To reduce exposure:
- Disable remote management unless it is strictly required, and if enabled, limit it to trusted IP ranges.
- Prefer HTTPS over HTTP for admin access and ensure certificate validation is enforced.
- Use two-factor authentication if supported or enabled via device policy.
- Maintain strict password controls and enforce a minimum password strength across all admins.
These steps help ensure that even if a device is reachable from outside the local network, unauthorized actors cannot easily compromise admin access.
Firmware updates and ongoing hardening
Security is a process, not a one-time event. Regular firmware updates provide essential bug fixes and security patches. Establish a routine to check for updates through the D-Link support portal and apply them after testing in a safe maintenance window. Prior to updates, back up current configurations and verify the vendor’s authenticity to avoid supply-chain risks. Post-update, recheck admin passwords and remote-management settings to ensure they remain aligned with your security policy.
Ongoing hardening also includes disabling unused features, enabling logging, and setting up alerts for unusual admin activity.
Real-world deployment considerations and common pitfalls
In real deployments, you may encounter a mix of devices with different firmware versions and security postures. Common pitfalls include assuming all devices share the same default credentials, neglecting to rotate passwords after deployment, and failing to enforce consistent remote-access policies. By documenting device-specific defaults, standardizing reset procedures, and cascading password policies across all APs, you can improve overall security while simplifying management. Finally, consider periodic penetration testing or vulnerability assessments to identify gaps that automated scans might miss.
Default credentials and reset options for DAP-1360
| Aspect | Default Value | Notes |
|---|---|---|
| Username | admin | Factory default on many devices; verify on device label |
| Password | admin or blank | Varies by firmware; check manual |
| Reset method | Reset button | Returns device to factory defaults; reconfigure after reset |
Your Questions Answered
What is the DAP-1360 default username and password?
Many D-Link devices use admin for the username and admin for the password. However, always verify with the device label or official docs. If you cannot login, use a factory reset followed by a reconfiguration. Always ensure the credentials are changed promptly after initial access.
The default is usually admin for both username and password, but you should verify with the device label or official docs and reset if needed.
How do I reset the DAP-1360 to factory defaults?
To reset, power the device, locate the reset button, and hold it for 6–10 seconds until the status indicators signal a reset. After the reset, you can access the device using its default LAN address and reconfigure from scratch.
Hold the reset button for several seconds until it resets to factory defaults, then reconfigure.
Is it safe to keep the default password long-term?
No. Keeping the default password creates an obvious entry point for attackers. Rotate credentials promptly after initial setup and implement a policy that requires strong passwords and periodic changes.
No—change the default password right after setup and follow a password policy.
Can I change the default password remotely?
Remote password changes depend on your device's configuration. If remote administration is enabled, ensure it is secured with HTTPS, restricted IP access, and strong authentication. If not needed, disable remote admin altogether.
You can change it remotely if remote admin is on and secured; otherwise disable remote access.
Where can I find official documentation for DAP-1360 password guidelines?
Refer to the D-Link support site and the DAP-1360 user manual for firmware-specific defaults and reset procedures. Cross-check with the device label and vendor knowledge bases to confirm current defaults.
Check the official D-Link manual and support site for the exact defaults and reset steps.
What should I do after resetting a DAP-1360 in a multi-device environment?
After a reset, reconfigure each AP with unique admin passwords, update firmware, and apply consistent security settings. Maintain an asset inventory and document changes to support audits.
Reconfigure each device with unique credentials and update everything, then document changes.
“Effective default-password management starts with a clear, repeatable process: reset, verify, and enforce strong credentials.”
Key Takeaways
- Start by locating the reset button to restore defaults.
- Always change the default password immediately after first login.
- Disable remote admin to reduce exposure.
- Keep firmware updated to improve security posture.
- Document admin credentials securely for audits.