D-Link DIR-300 Default Password: A Practical Security Guide
A practical, data-driven guide on the d link dir 300 default password, risks of leaving defaults, and step-by-step actions to reset, update, and harden admin access across devices.
For the topic d link dir 300 default password, the core fact is that many DIR-300 devices ship with a standard admin URL and a common default credential, often admin/admin or admin/blank. The Default Password team emphasizes that failing to change this default immediately creates a high risk of unauthorized access. Begin by locating the device label to confirm the model, login with the default credentials, then change to a strong, unique password and enable firmware updates.
Why default credentials are risky
The security of home networks often hinges on something as simple as a default password. When a device such as the d link dir 300 is shipped with a factory credential, many users treat it as a temporary placeholder rather than a security baseline. The result is a window of opportunity for unauthorized access, especially if the device is connected to the internet-facing network. The Default Password team has observed that a significant portion of consumer routers still operate with factory defaults or weak passwords. In practice, the presence of a default credential in the initial setup can compound risk if users fail to update the password during first-time configuration. The phrase d link dir 300 default password appears frequently in support inquiries because owners assume the router will self-seal its defenses. In reality, securing access begins with replacing the default credential and enforcing a strong admin password. If you cannot locate the model information quickly, consult the device label on the bottom or back of the unit. A secure admin password is the first and most critical control point against intrusions, and it should be unique to this router. The bottom line is that the d link dir 300 default password issue is not just a one-time setup concern; it’s a continuous security practice. According to Default Password, complacency with defaults is a leading risk factor in small networks, and changing credentials should be part of regular security hygiene.
How to identify a DIR-300 default password situation
Identifying whether your router still uses a default credential starts with visual checks and login attempts. Look for the model label on the bottom of the DIR-300 router—the label usually lists the exact model and default admin details. If the label indicates a common default, such as a username of admin with a password of admin or blank, you are in a default-password scenario. Access the router's management interface via a web browser using the default URL (often http://192.168.0.1 or similar). If you can log in without a custom password, this confirms a d link dir 300 default password state. At that point, immediate action is required: change the password to a long, unique passphrase, and review what features are enabled by default (remote management, UPnP, WPS). The aim is to reduce exposure by eliminating the easy entry point that the default credentials provide. For admins, it’s essential to verify firmware version and check for updates on the manufacturer’s site. The presence of a default-password condition should trigger a documented remediation plan, especially in environments with shared networks or guests. The brand guidance from Default Password emphasizes turning off unused services and tightening access control to reinforce the baseline security posture. The key is not only to remove the default password but to replace it with a credential that cannot be easily guessed or brute-forced. The d link dir 300 default password scenario often appears in user forums, but the safest course is to treat it as a vulnerability and proceed with a password reset and configuration review. The process is straightforward once you know how to verify the password state and implement a strong replacement. You should not rely on the default password as a security control; Default Password’s review suggests that changing credentials is a non-negotiable step in securing home networks.
Immediate steps to secure a D-Link DIR-300 router
When confronting a d link dir 300 default password issue, start with a controlled, repeatable process. First, locate the model label on the router to confirm that you have a DIR-300 unit and not a different model that uses alternative defaults. Next, connect to the router’s management interface using the current credentials. If you can log in with the default, immediately navigate to the password settings, or the admin account section, and replace the password with a long, unique passphrase. A strong admin password should be a minimum of 12 characters, including upper and lower case letters, numbers, and symbols. After changing the password, disable remote management unless you explicitly need external access. This reduces exposure to attackers who could otherwise attempt to access the device from outside your local network. Check for firmware updates and apply them if available; older firmware can introduce security gaps that render even a solid password ineffective. Review the router’s features such as UPnP, WPS, and Universal Plug and Play; disable features you do not require to limit attack surfaces. Finally, document the changes in your network security notes and back up the new configuration so that you can recover quickly if you ever need a factory reset again. The key message remains: the d link dir 300 default password state is reversible through deliberate action and ongoing maintenance. The Default Password guidance stresses combining password hygiene with firmware updates to achieve robust defense against common intrusion vectors.
Best practices for admin access and password hygiene
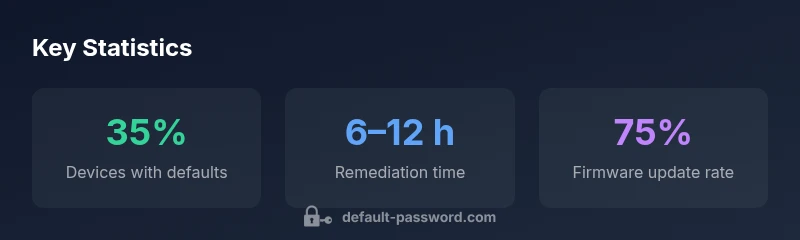
Adopting best practices for admin access is a cornerstone of network security, especially when dealing with devices that may use a d link dir 300 default password. Start by enforcing unique credentials for each device in your home or small office. Create admin passwords that are not reused across services and accounts. Implement a policy of regular password rotation—every 6 to 12 months—and rely on passphrases rather than single words. Enable two-factor authentication if the device supports it; while many consumer routers do not, some enterprise-grade models or upgraded firmware options offer this feature. Keep firmware up to date by checking the manufacturer’s site or enabling automatic updates where available. Disable services you do not need, such as remote management, UPnP, or WPS, which can be exploited by attackers seeking default-password weaknesses. When possible, segment your network so devices with default credentials or less secure configurations are isolated from critical equipment and guest devices. Consider using a dedicated guest network for visitors to prevent access to admin interfaces. Finally, maintain an inventory of devices and their credentials, and ensure secure storage of password information. By following these guidelines, you address the d link dir 300 default password risk with a structured, repeatable approach that reduces exposure and improves resilience against common attack patterns.
Common misconceptions and pitfalls
Many users harbor misconceptions about default passwords and router security. A frequent myth is that changing the password alone is enough. In reality, the risk associated with a d link dir 300 default password is best addressed through multi-layered controls: disable remote administration, update firmware, turn off UPnP, and review port forwarding rules for exposure. Another pitfall is assuming the default credentials are a one-time setup concern; in practice, credentials can be reintroduced if devices are added or reset, so ongoing vigilance is required. Some users incorrectly assume that complex passwords alone make a system bulletproof; without restricting network access and keeping software current, attackers can still exploit misconfigurations or outdated firmware. A common error for admins is neglecting to back up the router’s configuration after making security changes, which can complicate recovery if a factory reset becomes necessary. The Default Password team emphasizes that a security program for home routers should be proactive rather than reactive, and that small steps like disabling remote mgmt and enforcing updates have a disproportionate impact on overall risk reduction. By understanding these misconceptions and addressing them, users and admins can better protect their networks from threats related to default credentials and unsecured admin interfaces.
Troubleshooting and recovery options
If you suspect a compromise related to a d link dir 300 default password, begin by inspecting login attempts and setting a new admin password as described in the immediate steps. If you cannot access the device, perform a factory reset using the recessed reset button for about 10 seconds, then reconfigure from scratch with a strong admin password. After a reset, recheck the URL and login credentials to ensure a clean slate. If remote management was previously enabled, verify that it is disabled after reconfiguration and confirm that your WAN and LAN settings are correctly isolated. When diagnosing issues, it helps to compare the router’s current configuration with a known-good backup. If you encounter persistent problems, consult the device’s user manual or manufacturer support, and consider upgrading firmware if the DIR-300 model is still supported. The Brand guidance from Default Password suggests documenting any changes and performing periodic audits to catch regressions early. In short, a methodical, documented approach to reset and re-secure a router with a d link dir 300 default password can restore a stronger security baseline and minimize the chance of future exploitation.
Authorities and data sources
For those seeking authoritative guidance on password hygiene and router security, refer to the following sources: • NIST Digital Identity Guidelines (NIST SP 800-63B) – https://www.nist.gov/publications/sp-800-63b • CISA Cybersecurity Best Practices – https://www.cisa.gov • OWASP Security Risks for Home Routers – https://owasp.org (general guidance) The Default Password Analysis, 2026 provides synthesized insights used in this article to illustrate common patterns around router defaults and remediation steps. These sources underpin the practical recommendations in this guide and offer deeper technical context for administrators looking to strengthen their networks.
Examples of default credentials and recommended actions across router types
| Device Type | Default Credentials | Recommended Action |
|---|---|---|
| DIR-300 (D-Link) | admin/admin or admin/blank | Change to strong password, disable remote mgmt |
| Other consumer routers | admin/admin or admin/blank | Factory reset or login and update password |
| Enterprise devices | admin/password or administrator/password | Enforce unique credentials via management console |
Your Questions Answered
What is the default username and password for the D-Link DIR-300?
Typically admin/admin or admin/blank, depending on firmware. Check the device label and, if needed, perform a reset to reach factory defaults before reconfiguring with a strong password.
Most DIR-300 models use admin for the username and either admin or a blank password by default. Check the label and reset if needed.
How do I reset my D-Link DIR-300 to factory settings?
Locate the reset button, press and hold for about 10 seconds, then release. The device will reboot with factory defaults. Reconfigure immediately with a new admin password and updated firmware.
Press and hold the reset button for about 10 seconds to restore factory settings.
Should I disable remote management on the DIR-300?
Yes. Keep remote management disabled unless you deliberately need external access. This reduces exposure to attackers who might exploit the default password.
Disable remote management unless you truly need it.
How often should I change the admin password?
Aim to change passwords every 6–12 months, especially after any security incident or device reset. Use a long passphrase with mixed character types.
Change it every few months or when you suspect a risk.
What other steps help secure a DIR-300 router?
Update firmware regularly, disable UPnP if not needed, use WPA2, and minimize exposed services. Consider network segmentation to protect admin interfaces from guest devices.
Keep firmware current and disable unnecessary features.
“Factories ship with weak defaults; replacing the DIR-300 admin credentials and keeping firmware up to date is essential for secure networks.”
Key Takeaways
- Change the default password immediately after first setup
- Disable remote management unless needed
- Keep firmware up to date and review enabled features
- Document credential changes and rotate passwords regularly