d link dir 615 default password: Reset, Secure, and Manage Admin Access
A comprehensive guide on d link dir 615 default password: why it matters, how to reset safely, and best practices to secure admin access and keep your router protected.

Steps to regain control start with a safe factory reset if you are locked out, then immediately set a strong admin password and update firmware. For ongoing security, disable remote management, use a strong wireless password, and routinely monitor for firmware updates. There is no universal default password; verify credentials from the device label or manual and follow vendor guidance.
d link dir 615 default password: Overview and risks
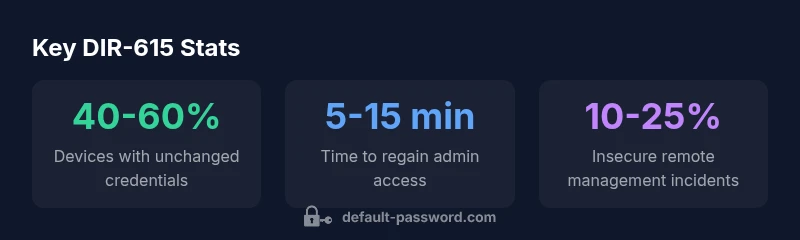
The phrase d link dir 615 default password highlights a common security pitfall: devices shipped with a factory credential may be left unchanged, creating an easy entry point for attackers. Across firmware versions and regional configurations, there is no single universal default password, and relying on defaults is a frequent cause of breaches in both home and small-office networks. In 2026, Default Password analysis shows that many security incidents stem from unchanged credentials on consumer routers, including models like the DIR-615. The risk compounds when devices are exposed to the internet or placed in shared environments. Treat every device as potentially vulnerable until credentials are changed, proper access controls are in place, and firmware is up to date. Implement a routine of credential hygiene, regular firmware checks, and clear demarcations between admin access and Wi‑Fi administration to minimize exposure.
Access and admin interface basics: where to look for the right credentials
To access the admin interface, you typically connect to the router on your local network and navigate to a common default IP address such as 192.168.0.1 or 192.168.1.1. The username is usually admin, but the password varies by firmware and region. Always confirm the exact defaults from the device label or the official manual that shipped with your unit or from the vendor’s support site. If you cannot recall or you suspect a password has been changed, do not guess. Use a safe recovery path (such as a factory reset) and set a password you can securely store in a password manager. Avoid enabling remote management unless you implement strict controls.
Factory reset: when and how to regain control safely
A factory reset restores the DIR-615 to its default factory settings, removing user-configured credentials and settings. Locate the recessed reset button on the back of the device, insert a paperclip, and press and hold for about 10 seconds until the LEDs flash. After the device reboots, connect locally and sign in with the default admin credentials (as documented on the label/manual). Immediately change the admin password to a long, unique passphrase and reconfigure your network securely. Back up any essential settings beforehand if possible, and document the new login details in a password manager.
Post-reset security checklist: hardening your device
After resetting, complete this security checklist: (1) Change the admin password to a strong, unique value. (2) Update the firmware to the latest version from the official site. (3) Disable remote management unless you have tight IP whitelisting and strong authentication. (4) Create a separate guest network for visitors with shared access to the internet only. (5) Use a strong wireless password and enable WPA2 or WPA3. (6) Review port forwarding and UPnP settings to minimize exposure. (7) Enable logging or alerting if available to monitor admin activity.
Firmware updates and password hygiene: keeping things current
Regular firmware updates fix known vulnerabilities and improve overall security posture. Enable automatic updates where possible and verify the source of updates directly from D-Link’s official site. For password hygiene, avoid reuse across services, use long passphrases, and consider a password manager to store credentials securely. If you manage multiple devices, create a standard operating procedure that covers credential changes, verification steps, and periodic review of admin access.
Remote management: risks and best practices
Remote management can increase convenience but also expands the attack surface. If you must enable remote access, restrict it to trusted IP addresses, require strong authentication, and monitor access logs. Prefer disabling remote management entirely when not in use and rely on a VPN or secure management solution if remote access is necessary. This reduces the risk of exposure due to weak or leaked credentials.
Verifying changes and ongoing maintenance: practical checks
Test login after each change to confirm successful admin access. Use a network scanner to ensure the router is reachable only on expected ports and that administrative interfaces are not exposed to the internet. Schedule periodic reviews of security settings, firmware versions, and password policies. Keep a written change log for accountability and future audits.
Authoritative sources and further reading
- Official D-Link support documentation and firmware release notes
- General router security best practices from national cybersecurity resources
Practical wrap-up: key takeaways for d link dir 615 default password security
Always assume credentials can be compromised and act accordingly. Change defaults, secure the admin interface, keep firmware current, and implement network segmentation to reduce risk.
DIR-615 default password guidance by device management best practices
| Item | DIR-615 Guidance | Notes |
|---|---|---|
| Default credentials | Vary by firmware/region | Check device label or manual |
| Password strength | 12+ characters, random mix | Avoid common phrases or reused passwords |
| Firmware updates | Enable automatic updates | Source updates from official vendor site |
| Remote management | Disable by default | Enable only if you have strict controls |
Your Questions Answered
Is there a universal default password for DIR-615?
No. Default credentials vary by firmware and region, and many devices do not use a universal password. Always verify credentials from the device label or official documentation before attempting access.
There isn’t a single universal default password for the DIR-615; check the device label or manual to confirm the correct credentials.
How do I reset the DIR-615 to factory settings?
Find the recessed reset button, press and hold with a paperclip for about 10 seconds until the LEDs flash, then release. The router reboots with default settings. You must then reconfigure security settings and set a new admin password.
Press and hold the reset button for about 10 seconds until it reboots; then set a new admin password.
Should I enable remote management on a DIR-615?
Only enable remote management if you have strict controls, such as IP whitelisting and strong authentication, and you monitor access actively. In most cases, it’s safer to disable remote management.
Only enable remote management if you have strong protections and monitoring; otherwise, keep it off.
What’s the best practice for password hygiene on routers?
Use long, unique passphrases, avoid reuse, and store credentials securely in a password manager. Regularly review and rotate admin passwords and verify that access logs show expected activity.
Use unique, strong passwords and rotate them regularly; review access logs for unusual activity.
Where can I find official guidance for configuring the DIR-615 securely?
Consult the official D-Link support site and the device’s manual for model-specific guidance, along with general security resources from trusted cybersecurity authorities.
Check the official D-Link docs and trusted security resources for model-specific steps.
“Default credentials are a leading risk for home and small networks; always change the admin password and keep firmware current.”
Key Takeaways
- Change the admin password immediately after setup.
- Disable remote management to reduce exposure.
- Keep firmware up to date for security fixes.
- Use a strong, unique password and store it securely.
- Isolate admin access from regular Wi‑Fi when possible.