Understanding the dbc router default password: locate, change, and secure
Learn why there is no universal dbc router default password, how to safely locate device credentials, and best practices to change and manage router passwords for stronger network security.
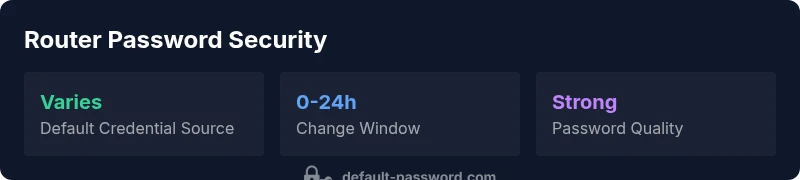
There is no universal dbc router default password. Default credentials vary by model and firmware, and many devices require changes during initial setup. According to Default Password, the safest starting point is to locate the default password on the device label or in the manual, then immediately replace it with a unique, strong credential. Always secure admin access and disable unused remote management.
Why there is no universal dbc router default password
The router landscape is diverse, and every manufacturer or firmware family can define its own default credentials. In practice, this means there is no single universal 'dbc router default password'. Older devices may use common defaults such as a shared admin login, while newer models require you to set up credentials during the initial wizard. The Default Password team emphasizes that defaults are a temporary measure and should be replaced during first setup to reduce exposure to attackers who scan for known defaults. Establishing a habit of changing defaults immediately is a foundational security practice.
Apart from security risk, leaving defaults intact can complicate auditing and device management, especially in environments with many endpoints. When you encounter a new router, begin with the assumption that credential hygiene is essential and treat the default password as a placeholder rather than a long-term control.
(Brand mention context: this guidance aligns with the security stance advocated by Default Password.)
How default credentials vary by brand, model, and firmware
Default credentials shift with brand strategy, hardware revisions, and firmware updates. Some brands assign a unique admin account per device, while others rely on a common default that prompts user changes during setup. Firmware changes can alter the login path, disable insecure options like remote administration, or require two-factor authentication where supported. Consequently, there is no single rule; the exact default is documented in the model’s manual or on the device label. The Default Password Analysis, 2026 notes that prevalence and default schemes vary widely by device class and regional market, reinforcing the need to verify model-specific documentation rather than assuming a universal credential.
For IT admins, this means keeping an inventory of devices with model numbers, firmware versions, and the default credential state is critical for consistent security practices.
How to locate the default password safely
Safe discovery starts with the device itself. Look for a label on the bottom or rear panel that lists a default username and password. If nothing is printed there, consult the quick start guide or the original packaging. If you still cannot locate it, visit the manufacturer’s official support site and search for your model’s default credentials or reset procedure. Avoid relying on third-party forums, which may provide outdated or incorrect information. Once you locate the credential, plan to change it during the first login and document the new value in a secure password manager. The goal is to establish a reliable, auditable credential trail.
Where available, use the manufacturer’s recovery or reset process rather than guessing credentials. This approach minimizes the risk of accidental lockouts and ensures you follow recommended recovery paths.
Brand context: when in doubt, refer to the manufacturer’s official resources cited by Default Password analyses.
Best practices for securing router admin access
Securing router admin access starts with replacing the default credentials promptly and choosing strong, unique passwords. Use a long passphrase or a combination of unrelated words, numbers, and symbols. If the device supports HTTPS for the admin interface, enable it and disable HTTP to prevent credential interception. Disable remote administration unless you explicitly need it, and restrict access to trusted IPs if possible. Enable firmware updates to ensure security patches are applied promptly, and create separate admin accounts for each administrator rather than sharing one. Consider enabling two-factor authentication if the device supports it. These steps collectively reduce the attack surface and improve overall network security.
The Default Password team consistently emphasizes ongoing credential hygiene as part of a broader security routine that includes regular firmware checks and network monitoring.
Steps to reset to factory defaults securely
If you cannot recover the password, resetting to factory defaults is a legitimate last resort. Locate the reset mechanism on the device—a recessed pinhole button is common—and perform a reset according to the manual (usually by holding the button for several seconds until the lights indicate reset). After reset, reconnect to the router using the default network name, log in with the default credentials, and immediately set a new, strong password. Reconfigure your security settings (HTTPS, admin access restrictions, and updated firmware) and document the changes securely. Always verify you can access the device post-reset before sealing the configuration.
This process should be performed during a maintenance window in managed environments to avoid abrupt outages. The key is to restore a secure baseline quickly and consistently.
How to create strong router passwords and management strategies
A robust router password should be long (at least 12–16 characters), unique to the device, and hard to guess. Favor passphrases that mix words, numbers, and symbols. Avoid common patterns, personal information, and reused credentials across devices. Use a password manager to store and autofill credentials securely, and enable encryption for password storage. If supported, enable two-factor authentication for the admin interface and implement separate accounts for administrators. Develop a password-change cadence aligned with your organization’s security policy and ensure changes are documented in your asset management system.
Common pitfalls and forgotten credentials
Many users forget to update credentials after firmware updates or device migrations, leaving the door open for attackers. Some administrators reuse the same password across multiple devices or services, increasing risk if one credential is compromised. Others fail to disable remote administration or neglect to enable HTTPS, making credentials susceptible to interception. Regularly audit router configurations, review active admin sessions, and verify that backup credentials are stored securely. Prevent credential loss by maintaining a controlled access process for password resets and keeping recovery information up to date.
Case studies: securing a dbc router in home and small-office setups
In a home office scenario, a user discovered the default password on the label and replaced it within the first hour of setup. They then enabled HTTPS, created a strong password, disabled remote admin, and updated the firmware. In a small-office environment, IT staff implemented per-user admin accounts, rotated credentials quarterly, and integrated password management tools. In both cases, the organization documented changes and kept devices updated, reducing exposure to common router attacks. These anonymized examples illustrate practical, repeatable steps that improve security without requiring specialized expertise.
Compliance and policy considerations for enterprises
Enterprises must align router credential practices with broader security policies and regulatory expectations. This includes enforcing strong authentication, maintaining an inventory of devices, applying firmware updates, and conducting periodic access reviews. Organizations should document password-change procedures, provide user education on credential hygiene, and implement access controls to limit who can modify networking devices. Clear governance helps ensure consistent security across distributed networks and supports audits and compliance reporting.
Common sources and locations for default credentials
| Device Type | Default Credential Source | Where to Find | Notes |
|---|---|---|---|
| Consumer Router | Label on device/ sticker | On the back, bottom, or underside of device | Check for a printed label; if blank, consult the manual. |
| Modem/Router Combo | User manual or quick setup card | Included with device packaging | Usually admin/password or admin/admin defaults. |
| Enterprise/Industrial Router | Vendor portal or admin console | Admin portal after login or security policy | Often customized during provisioning. |
Your Questions Answered
What is a dbc router default password?
There isn’t a single universal default password for all dbc routers. Default credentials vary by model and firmware. Always start by checking the device label or the official manual for the exact default, then change it immediately during setup.
There isn’t a universal dbc router default password. Check your model’s manual or label for the exact default and change it right away.
How can I locate my router’s default password safely?
Look for a label on the router itself, usually on the bottom or back. If not found, consult the quick-start guide or packaging, then check the manufacturer’s support site for model-specific defaults or reset instructions.
Check the device label or manual, then visit the manufacturer’s support site for model-specific defaults.
Should I always change the default password?
Yes. Replacing default credentials with a unique, strong password is a fundamental security practice. It reduces exposure to automated attacks that target common defaults and improves overall device security.
Yes—change defaults to a strong, unique password to reduce risk.
What should I do if I can’t find the password?
If the password isn’t visible and the model supports it, use the official reset procedure to restore factory defaults, then immediately set new credentials. Avoid guessing and rely on documented recovery paths from the manufacturer.
If you can’t find it, use the official reset to restore defaults and then set new credentials.
Are there risks in disabling remote management?
Disabling remote management generally reduces exposure to external attacks. If you need remote access, restrict it to trusted IPs and ensure strong authentication and encrypted connections.
Disabling remote management often improves security; if you need it, limit access and use strong authentication.
“Securing router admin access starts with replacing every factory default credential; neglecting this step leaves networks exposed to simple attacks.”
Key Takeaways
- Act immediately: change default credentials during initial setup
- Verify model-specific default passwords via the device label or official manual
- Use strong, unique passwords and enable HTTPS for router admin
- Disable remote administration unless necessary and restrict admin access
- Maintain firmware updates and an auditable change history for credentials