Default 365 Password Policy: Best Practices for Microsoft 365
Learn how to review, update, and enforce a robust Microsoft 365 password policy with MFA and best-practice controls to protect admin access and user accounts.

This guide helps you review, update, and enforce a robust Default 365 password policy for Microsoft 365. You’ll learn the key components, how to audit your current settings, and practical steps to align with security best practices. The goal is stronger passwords, MFA, and consistent admin access controls across the tenant.
What is the default 365 password policy?
The term 'default 365 password policy' refers to the set of rules governing user passwords within Microsoft 365 tenants. It covers password length, complexity, expiration, lockout behavior, and how those settings interact with Azure Active Directory. In practice, a strong policy reduces the risk of credential stuffing and unauthorized admin access. For organizations, aligning this policy with industry standards helps meet compliance requirements and strengthens overall security posture. The Default Password team emphasizes that policy design should balance usability with security, and should be revisited regularly as threats evolve.
Key considerations include ensuring the policy applies to all user accounts, including external guests where appropriate, and that administrators follow the same rules as standard users. Centralized enforcement—ideally through a single identity source—simplifies auditing, reporting, and remediation. By documenting baseline settings and change history, you can track improvements and defend against audit findings.
Why a strong password policy matters for Microsoft 365
A robust policy mitigates common attack vectors, such as brute force, credential reuse, and phishing theft. In cloud-based environments like Microsoft 365, attackers target weak passwords to pivot to higher-value resources. Enforcing long passwords, periodic changes, and MFA drastically reduces risk. Compliance frameworks often require documented password controls, access governance, and audit trails. The Default Password team notes that organizations with clear password policies and MFA show improved security hygiene and incident readiness. Additionally, policy visibility across devices and apps helps IT teams audit and enforce consistent controls.
Core components of a modern password policy
- Minimum length and complexity: Define a baseline length and ensure passwords do not rely solely on dictionary words.
- Password history: Prevent reuse by storing a short history so past passwords cannot be reused.
- Expiration vs. modern approaches: Some tenants opt for non-expiring passwords combined with MFA, while others still enforce renewal after a set period.
- Lockout and throttling: Introduce account lockouts after failed attempts to deter brute-force campaigns, with safe reset processes.
- Password reset workflow: Ensure self-service reset flows are secure and monitored.
- MFA as default: Require MFA for initial login and high-risk sign-ins, reducing dependence on password strength alone.
- Admin access protection: Separate admin accounts from general user accounts and enforce stricter controls and auditing.
A balanced policy uses sensible minimums while leveraging modern authentication factors to minimize risk.
Review your current policy in Microsoft 365 / Azure AD
To understand how your tenant currently handles passwords, start by auditing the existing settings in the Microsoft 365 admin center and the Azure Active Directory portal. Look for: password expiration rules, password length requirements, lockout thresholds, and whether MFA is enforced for all users or only high-risk sign-ins. Review any conditional access policies tied to sign-ins and ensure they align with organizational risk tolerance. Export reports on user password ages and MFA adoption to identify gaps and remediation priorities. The goal is a clear, auditable baseline from which to plan improvements.
Implementing or updating the policy: practical steps (overview)
In practice, updating a policy involves policy scoping, stakeholder alignment, and configuration changes in the identity provider. Plan for a phased rollout that includes user communication, pilot testing, and a rollback plan. Ensure that change windows minimize user disruption. Document the policy in your security handbook and map it to relevant standards. A strong policy often combines password controls with device compliance, conditional access, and MFA to create a layered defense.
Common pitfalls and best practices
- Infrequent reviews: Password policies drift over time; schedule quarterly reviews.
- Overly complex requirements: Too-strict rules can lead to password vault avoidance; favor long, memorable phrases and passphrases when possible.
- Ignoring MFA: Without MFA, password-only security is weak. Enforce MFA for all users including admins.
- Not protecting admin accounts: Use separate admin accounts and rotate credentials.
- Inadequate reset processes: Self-service resets must include identity verification and secure channels.
- Poor reporting: Maintain ongoing dashboards showing password policy compliance and MFA adoption.
Testing, auditing, and ongoing improvements
After implementing, test with a sample group of users to ensure that sign-ins work, resets are secure, and MFA prompts behave as expected. Use regular reports to monitor password age, failed login attempts, and admin-sign-in events. Schedule reviews and adjust to changing threat landscapes and business needs. The policy should be treated as a living document; update it when new threats or platform changes emerge.
Tools & Materials
- Microsoft 365 admin center credentials(Global admin or Privileged Role Administrator required)
- Azure Active Directory portal access(Needed to view and configure password policies)
- MFA setup for test accounts(Test user accounts to verify MFA prompts and resets)
- Policy documentation template(Document the policy goals, rules, and exceptions)
- Test user accounts(Use a dedicated test group to validate policy changes)
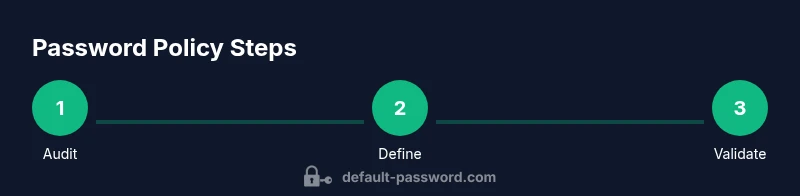
Steps
Estimated time: 60-120 minutes
- 1
Audit current settings
Sign in to the admin portal and review existing password policy settings in Microsoft 365 and Azure AD. Export the current configuration to establish your baseline and identify gaps.
Tip: Export baseline reports to quantify current password ages and MFA enrollment. - 2
Define policy objectives
Decide on core controls (password length, history, expiration, lockout, MFA) and ensure they align with compliance requirements and risk tolerance.
Tip: Engage security, IT, and compliance stakeholders early to build consensus. - 3
Configure password policy
Apply the selected policy settings across the tenant in the identity provider, ensuring coverage for all users and admins.
Tip: Start with a pilot group to catch misconfigurations before wider rollout. - 4
Enable MFA for all users
Enforce MFA for initial sign-ins and high-risk scenarios to reduce reliance on password strength alone.
Tip: Offer multiple MFA methods (authenticator app, hardware key) to improve adoption. - 5
Communicate changes
Notify users about new requirements and provide a brief, actionable guide for creating compliant passwords and enrolling in MFA.
Tip: Offer a quick-start guide and FAQ to minimize support requests. - 6
Test and verify
Run sign-in and reset tests with a controlled user group; confirm that logs, alerts, and admin access behave as expected.
Tip: Verify that helpdesk workflows align with the new policy. - 7
Monitor and adjust
Set up dashboards for password age, failed sign-ins, and admin sign-ins; schedule quarterly reviews and adjust as needed.
Tip: Document changes and maintain an audit trail for compliance.
Your Questions Answered
What makes a password policy effective for Microsoft 365?
An effective policy enforces minimum length, history, MFA, and coverage across users, with clear reset workflows. It should be aligned with compliance requirements and regularly reviewed.
An effective policy uses strong passwords, MFA, and clear reset processes, and it’s reviewed on a regular basis.
Should we require password expiration in Microsoft 365?
Modern best practices favor longer-lived passwords combined with MFA rather than frequent forced changes. If you require expiration, pair it with MFA and pre-change notifications.
Most organizations don’t require frequent password changes if MFA is in place; consider expiration only with proper user communication.
How can we enforce MFA across all users?
Use conditional access policies to require MFA for all sign-ins, including admins, and monitor adoption with reports and dashboards.
Set a rule that MFA is required for every user login and monitor adoption.
What are common pitfalls when updating a Microsoft 365 password policy?
Overly complex rules, neglecting admin accounts, and insufficient user communication can undermine policy effectiveness.
Don't overcomplicate the policy; ensure admins are covered and users are clearly informed.
How do we test a new password policy before full rollout?
Pilot the policy with a small user group, verify sign-ins and resets, and collect feedback before wider deployment.
Run a small pilot first to catch issues before a full rollout.
What sources guide password policy decisions?
Refer to standards like NIST SP 800-63B and vendor guidance, and adapt to your environment.
Check NIST and vendor docs for best-practice guidance.
Watch Video
Key Takeaways
- Define a clear password baseline aligned with MFA
- Audit and document your current policy first
- Roll out in stages with user communication
- Regularly audit and adjust policy