Default OPC Passwords in Oracle Cloud: Security and Recovery Guide
Learn how to identify, reset, and manage default OPC passwords in Oracle Cloud. This guide covers risks, step-by-step remediation, and policies to prevent credential abuse across Oracle Cloud environments.
Default OPC password oracle cloud security hinges on immediate remediation. There should be no usable default credentials; reset the OPC password, disable default accounts, enforce MFA, and implement RBAC. This article provides a practical, end-to-end approach to securing Oracle Cloud OPC access.
Understanding OPC and Default Passwords in Oracle Cloud
In Oracle Cloud, and particularly with legacy OPC deployment patterns, a default administrative credential can exist during initial setup. The phrase default OPC password oracle cloud emphasizes the risk of leaving such credentials unchanged. This section explains what OPC is in typical Oracle Cloud environments, why the default password matters, and how attackers exploit weak credential hygiene to gain privileged access. You will also learn how to identify cloud resources where default credentials may still be in use and why this is a high-priority security issue in 2026.
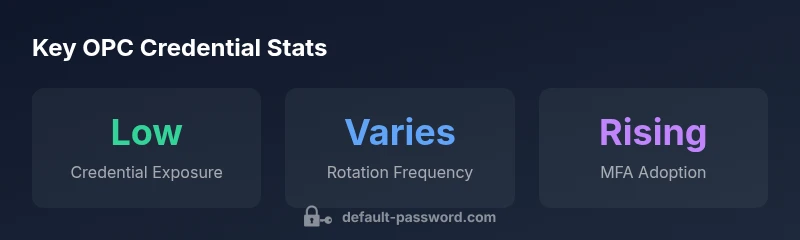
Key takeaways: Treat any default credentials as a vulnerability that requires immediate remediation across all Oracle Cloud components. Effectively managing credentials begins with discovery, inventory, and policy enforcement.
The Risks of Default OPC Passwords in Cloud Environments
Default credentials are a leading vector for unauthorized access because they are predictable, widely documented, and often not rotated after provisioning. In Oracle Cloud OPC contexts, a stale or weak password can give an attacker privileged access to compute instances, storage, and network configurations. This section outlines the typical attack paths—initial access, credential stuffing, and privilege escalation—and why cloud environments magnify the impact of a credential misconfiguration. Real-world scenarios illustrate forgotten defaults found during audits and the downstream consequences for data integrity and service availability.
Immediate Response: Resetting and Rotating OPC Passwords
When you discover a default OPC password in Oracle Cloud, act quickly through a structured remediation workflow. Start by disabling or changing the account password, rotating API keys and SSH keys, and applying role-based access controls to limit blast radius. Then enforce MFA for all admin channels, rotate any service accounts, and review access to sensitive resources. This section provides concrete, vendor-agnostic steps you can execute using the Oracle Cloud Console, CLI, and API where available. Include verification steps to confirm successful credential changes and log audits.
Implementing Strong Passwords and MFA in Oracle Cloud
Strong password hygiene goes beyond length and complexity. Combine rotation policies with MFA, device-based access, and session controls. In Oracle Cloud OPC contexts, enforce password policies at the project or compartment level where possible, and ensure that password resets require multi-factor authentication. This section discusses how to design password policies that align with regulatory expectations while remaining practical for admins and operators to follow.
Role-Based Access Control and Least Privilege for OPC
Assign permissions based on roles, not individuals. For OPC, ensure that admins receive only the privileges they need, and avoid granting broad access to critical resources. Use groups and managed identities to simplify onboarding and offboarding. This section guides you through mapping OPC responsibilities to RBAC policies, integrating with existing identity providers, and documenting access decisions for audits.
Auditing, Logging, and Compliance for OPC Passwords
Enable Cloud Audit Logs and log aggregation for OPC-related activities, including password changes, account enabling/disabling, and privileged access events. Regular audits help detect anomalous activity and verify policy adherence. This section covers practical monitoring strategies, alerting thresholds, and how to prepare for compliance reviews related to credential management in Oracle Cloud.
Practical Tooling: Checks, Scripts, and Policies
Automate discovery of default credentials with lightweight scans, validate password resets with automated checks, and apply configuration as code to enforce policy across the Oracle Cloud environment. This block provides example commands, scripts, and policy templates you can adapt to your own environment to sustain secure OPC credential hygiene over time.
Real-World Scenarios: Pitfalls and How to Avoid Them
We examine common missteps—reusing old defaults, ignoring deprovisioned accounts, and inconsistent MFA setup—and how to prevent them. By aligning procedural controls with technical safeguards, you reduce the chance of credential leakage and improve incident response readiness in Oracle Cloud OPC deployments.
OPC credential risk mitigation table
| Aspect | Action | Rationale |
|---|---|---|
| OPC default password risk | Identify and inventory all OPC accounts with default credentials | Reveals exposure and guides remediation |
| Password rotation policy | Mandate rotation every 90 days or upon staff changes | Limits time window for compromise |
| Access auditing | Enable Cloud Audit Logs for OPC activity | Detects unauthorized access and policy violations |
Your Questions Answered
What does OPC stand for in Oracle Cloud, and why does its password matter?
OPC refers to the default administrative account used during Oracle Cloud deployments. Its password is critical because compromise could grant high-privilege access. Disable or secure the default account and enforce password rotation and MFA.
OPC is the default admin account in many Oracle Cloud deployments. Secure it immediately by disabling the default and rotating the password, then enable MFA.
Why are default OPC passwords dangerous?
Default credentials are widely known and easy to exploit. In OPC contexts, a compromised password can lead to privileged access, data exposure, and service disruption.
Default OPC passwords are a known risk; attackers can gain admin access if they’re left unchanged.
How do I reset the OPC password in Oracle Cloud?
Use the Oracle Cloud Console to reset the OPC password, rotate related keys, and enforce MFA. If legacy Linux images use the opc user, reset via SSH or cloud-init as appropriate.
Reset the OPC password via the Console, rotate keys, and enable MFA. For Linux images, reset the opc user via SSH or cloud-init.
Can I disable the default OPC account?
Yes. Disable or rename the default OPC account, and instead rely on controlled admin accounts with strong passwords and MFA.
Yes—disable or rename the default OPC account and enforce strong credentials with MFA.
What are best practices to prevent default credentials in OPC?
Implement MFA, RBAC, regular credential rotation, deprovisioning of unused accounts, and continuous auditing. Use automation to enforce these policies across Oracle Cloud.
Use MFA, RBAC, rotate credentials regularly, and audit access to keep OPC secure.
“"Effective credential hygiene in Oracle Cloud starts with treating every default password as a security risk and implementing automated rotations."”
Key Takeaways
- Audit OPC accounts to identify default credentials
- Reset and rotate default passwords immediately
- Enforce MFA and RBAC for admin access
- Automate ongoing audits and password-change reminders