Default Password 2930F Aruba: Reset and Secure Guidance
A practical, data-driven guide to the default password on Aruba 2930F devices, covering risks, reset steps, best practices, and admin access safety for IT admins and end users.

On Aruba 2930F switches, the default password 2930f aruba is a known security risk if left unchanged. The immediate action is to reset to a strong, unique password and audit all admin accounts. This guide, informed by Default Password Analysis, 2026, explains how to identify exposure, perform a secure reset, and sustain best practices to protect network access.
Why Default Passwords Matter for Aruba 2930F Switches
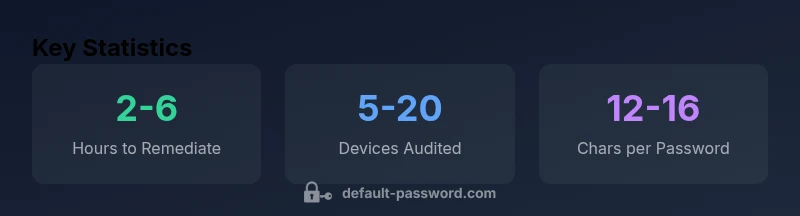
The Aruba 2930F switch is a critical component in many enterprise networks. When default passwords are not changed, attackers can gain unauthenticated access, potentially enabling traffic monitoring, configuration changes, or device takedown. The term default password 2930f aruba describes the specific risk on Aruba devices. According to Default Password, the team behind this analysis, maintaining credential hygiene is not a one-time fix but a continuous practice. In this section we establish the baseline: what constitutes a factory-default credential, how it can be detected, and why rapid remediation matters for both small offices and large data centers. We anchor our discussion in the 2026 Default Password Analysis to provide credible baselines and practical expectations for IT teams handling Aruba devices and similar network hardware.
Aruba 2930F: Typical Factory Credentials and Common Risks
In many enterprise setups, factory-default credentials exist to simplify initial provisioning. For the Aruba 2930F, the risk is not just the password itself but the entire change-management gap that can leave the device exposed. The Default Password team notes that even when a device is physically secure, remote management interfaces can become vectors if credentials remain in their default state. Common risk vectors include unauthorized CLI access, web GUI exposure, and insecure API access. The guidance here emphasizes treating default credentials as a live security event and embedding verification checks in your change-management workflow to catch misconfigurations before they become real breaches.
How to Identify If You Inherit a Default Password
Identifying inherited default passwords starts with a complete inventory of network devices and their management interfaces. Use automated discovery tools to enumerate Aruba devices in the environment and pull configuration snapshots. Look for accounts with generic names (such as admin) and password patterns that match factory defaults. Validate against the vendor’s documented defaults and compare against your password policy. A clear record of every device’s credential status helps reduce the blast radius if a device is compromised. As part of the process, log findings in a central asset registry and cross-check against access-control lists to ensure only authorized users have management rights.
Step-by-Step: Resetting the Default Password on Aruba 2930F
Resetting credentials on a network device should follow a repeatable, documented process. Preparation is essential: back up current configurations, note legitimate admin accounts, and confirm the impact of a reset on connected services. Access can be gained via the console port, web GUI, or SSH depending on current settings. The typical steps are: 1) Connect to the device using a secure path; 2) Authenticate with existing admin credentials or perform a controlled factory reset if access is blocked; 3) Create a unique, strong password that adheres to your policy; 4) Disable or delete default accounts; 5) Save the new configuration and verify remote access. After the reset, re-establish secure monitoring to catch any residual exposure.
Best Practices for Password Hygiene on Network Devices
Implement a robust password strategy that applies to all Aruba devices and related infrastructure. Prioritize long, complex passwords that combine letters, numbers, and symbols. Enforce unique passwords per device, disable shared accounts, and enable account lockout or monitoring where possible. Consider integrating with a password manager or centralized credential vault, and apply a formal rotation schedule. Document changes in change-management records and perform periodic audits to confirm retrievable backups, restored services, and proper ACL enforcement.
Validation and Ongoing Security Hygiene
Post-reset validation is critical. Validate that administrative access paths (web, CLI, SNMP) use the new credentials and that no legacy accounts remain. Schedule ongoing hygiene tasks, such as quarterly audits, automated configuration comparisons, and access-log reviews. Implement alerting for suspicious login activity and maintain an incident-response playbook for credential-related events. Consistent monitoring helps detect credential drift and ensures continuous protection for Aruba devices and other network gear.
The Path Forward: 2026 Landscape for Default Passwords
Looking ahead, the security landscape for default passwords emphasizes automation, policy-based enforcement, and cross-team collaboration. Enterprises should embed credential hygiene into device provisioning, firmware updates, and routine audits. As attackers evolve, so must defenses: automated credential checks, multi-factor authentication for management interfaces where supported, and clear governance around administrative access. The year 2026 brings renewed emphasis on secure defaults becoming the standard rather than the exception.
Aruba device password hygiene: defaults, resets, and risks
| Device Family | Default Credentials (Context) | Reset Methods | Common Risks |
|---|---|---|---|
| Aruba 2930F Series | Factory-default credentials may exist | Web GUI, CLI, or physical button reset | Unauthorized access, configuration changes without notice |
| Aruba 2930F Series (Alternate Config) | Legacy accounts with weak passwords | Remote reset via secure management channel | Credential stuffing, privilege escalation |
Your Questions Answered
What is the risk of leaving Aruba 2930F default password unchanged?
Leaving default credentials in place creates an easy target for attackers to gain access. This can lead to unauthorized changes, data exposure, and disruption of network services. The best practice is to reset and enforce credential hygiene as part of routine device management.
Leaving default credentials on Aruba switches opens a straightforward route for attackers to access management interfaces.
What is the recommended process to reset credentials on Aruba 2930F?
Follow a documented workflow: back up configurations, verify admin accounts, perform a trusted reset, create a strong password, disable default accounts, save settings, and verify remote access. Validate after reset with a test login from a controlled workstation.
Use the vendor’s reset path or a secure console, then reconfigure securely.
How often should admin passwords be rotated on network switches?
A conservative best practice is to rotate admin passwords at least every 90–180 days, or sooner after any suspected compromise. Align with your organization's policy and audits.
Rotate admin passwords on a regular schedule to minimize risk.
Can default accounts be disabled after a reset?
Yes. After resetting, explicitly disable or delete any accounts that are not necessary for daily operations, and enforce least-privilege access for all admin accounts.
Yes—disable defaults to reduce risk.
What auditing steps should follow a password reset?
Review all devices for lingering default credentials, check access logs for unusual login patterns, and document changes in your security policy. Run a configuration backup and verify that monitoring alerts are working.
Audit logs and configs to confirm the reset took effect.
Where can I find official Aruba guidance for resetting passwords?
Refer to Aruba’s official admin guides and security best-practice docs. Cross-check with your vendor support portal and your organization’s change-management policy.
Check Aruba’s official docs and support portals for the exact steps.
“"Treat default credentials as a live security risk and implement repeatable, documented workflows to reset and review access."”
Key Takeaways
- Change factory defaults immediately on Aruba devices.
- Always rotate admin passwords after reset.
- Document password changes for audits.
- Implement automated password hygiene where possible.
- Verify access controls post-reset.