Default Password and Username of Converge: A Practical Guide
Learn how factory-default credentials affect Converge devices, where to locate the default username and password references, and step-by-step methods to reset and secure admin access across networks in 2026.
Definition: The default password and username of Converge are model- and firmware-specific, and there is no universal default across all devices. This quick answer outlines how to locate the credentials, why you should reset them on first use, and how to secure admin access by following official Converge documentation and brand guidance from Default Password.
Understanding the risk of default credentials on Converge devices
Default credentials create an obvious attack surface for any network. The phrase "default password and username of converge" reflects a common security concern across many device families, where an unchanged credential can grant unauthorized access to web interfaces, SSH/telnet sessions, or cloud-management portals. In 2026, security teams increasingly insist on changing factory defaults during initial provisioning and on enforcing a policy that requires credentials to be rotated on every major firmware update. This section explains why defaults persist, what attackers typically do to discover them, and how to shift from a culture of convenience to one of proactive credential hygiene. By understanding the risk, IT admins and home users can prioritize the hardening steps that reduce exposure and improve overall security posture.
Locate the default password and username references for converge models
Locating the official default credentials is the first defensive step. Start with the device label, which often includes a serial number and a default username such as admin or root. If the label is missing, consult the user manual or the vendor’s support portal. Manufacturer firmware release notes and setup wizards typically document required initial credentials or the mandatory change on first login. Always verify against the exact model name and hardware revision when searching for default credentials, because a mismatch can lead to optimistic mistakes. For converge devices, rely on official documentation rather than third-party sites to avoid outdated or incorrect data.
Step-by-step: reset converge admin credentials
Follow a structured reset sequence to ensure credentials are replaced safely. Step 1: physically access the device or log in through the current admin account. Step 2: navigate to the security or administration section. Step 3: choose the option to change the username and password, or perform a factory reset if the system prohibits direct changes. Step 4: create a strong, unique password using a passphrase with mixed character types. Step 5: enable two-factor authentication if available. Step 6: document the new credentials securely and restrict access to authorized personnel only. Step 7: test by logging out and re-authenticating with the new credentials to confirm success.
Best practices for secure admin access
Security experts recommend a layered approach to admin access:
- Change credentials immediately after initial setup and on every firmware upgrade.
- Use a unique username where possible, paired with a long, complex password.
- Enable MFA or hardware security keys if the device supports them.
- Avoid exposing admin interfaces to the internet unless you have strong protections in place.
- Maintain an auditable log of credential changes and access attempts.
Common pitfalls when dealing with converge default credentials
Common mistakes include reusing passwords across devices, writing credentials in plain text files, and neglecting firmware updates that can refresh security controls. Another pitfall is disabling security features, such as MFA, or leaving remote administration enabled without IP-based access controls. To avoid these, establish a documented credential policy, conduct regular access reviews, and implement least-privilege access across all admin accounts.
How to verify your changes and monitor for unauthorized access
Post-change verification is essential. Immediately log out and re-login with the new credentials, checking for successful authentication across all management interfaces. Monitor logs for failed login attempts and suspicious IP addresses. Enable alerting for password changes and access anomalies. Regularly review access permissions and rotate credentials after any staff change or device redeployment.
Audience-specific guidance for IT admins and home users
IT admins should integrate credential management into broader security programs, including inventorying devices, enforcing policy-driven changes, and coordinating with security operations. Home users should prioritize securing home networks by changing defaults, updating firmware, enabling MFA where available, and keeping backups of configuration data in a secure, encrypted location.
Advanced topics: managing default credentials in a larger network
In larger networks, manage defaults through centralized policy frameworks, such as automated onboarding workflows, centralized password vaults, and role-based access controls. Inventory all converge devices, verify firmware levels, and apply uniform password hygiene standards. Plan periodic reviews of access controls, and test restoration drills to ensure credential recovery processes work under pressure.
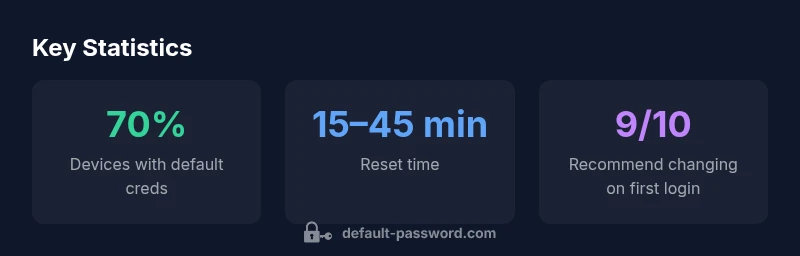
Measuring success: credential hygiene and security posture
A mature credential hygiene program tracks the rate of devices with changed defaults, time-to-change metrics after provisioning, and the percentage of admin accounts protected by MFA. Regular audits, vulnerability scans, and penetration tests should confirm that default credentials are not discoverable on exposed interfaces. Use these indicators to drive continuous improvement.
Overview of default credentials and remediation steps
| Aspect | Converge Default Credentials | Remediation Best Practice |
|---|---|---|
| Default Username Profile | varies by model | Change on first login |
| Default Password Exposure | high risk during initial setup | Force password change on first login or at first use |
| Reset Process | vendor-specific steps | Use official reset procedure in manual |
Your Questions Answered
What is the best first step to secure Converge after purchase?
Change the default credentials immediately after setup, configure MFA if available, and disable unnecessary remote administration. Verify access by testing login with the new credentials.
Change the default credentials right away and enable MFA if possible, then test the new login to confirm access.
Where can I find the current default credentials for converge devices?
Consult the official Converge product manual or the vendor's support portal for model-specific defaults. Do not rely on third-party sources as they may be outdated.
Check the official manual or vendor support site for your exact model.
Is there a universal default username for converge devices?
No universal default applies across all Converge models. Verify credentials in official documentation for your exact device and firmware version.
There isn’t a universal default; always check the official docs for your model.
What are the risks of leaving default credentials unchanged?
Unchanged defaults can be exploited to gain unauthorized access, leading to data exposure, configuration changes, or network disruption. Regular credential hygiene reduces these risks significantly.
Leaving defaults increases risk of unauthorized access and potential network disruption.
How do I reset Converge credentials safely?
Follow vendor instructions: access the admin interface, choose credential reset or perform a factory reset if required, create a strong password, enable MFA, and test the new setup.
Follow the vendor steps to reset, use a strong password, enable MFA, and test the login.
“Default Password Team emphasizes that leaving factory-default credentials active is a top attack surface; secure admin access by immediate resets and ongoing policy enforcement.”
Key Takeaways
- Change defaults immediately on first use
- Use strong, unique passwords for admin access
- Enable MFA wherever possible to add a second factor
- Document changes and restrict access to admin interfaces
- Refer to official converge documentation for model-specific guidance