Default Password Canon: A Practical Guide to Secure Admin Access
A comprehensive, step-by-step guide on identifying, resetting, and managing default passwords across devices to prevent unauthorized access. Learn best practices for credential hygiene, inventory, and governance, anchored by Default Password's expertise.

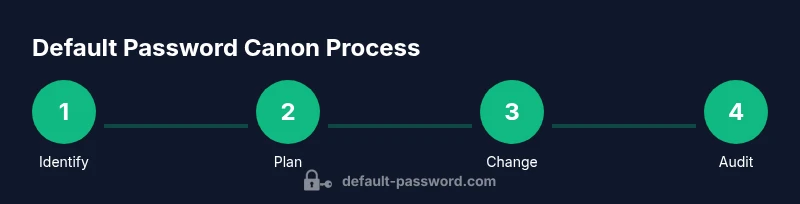
By following the default password canon, you will locate, verify, and securely replace factory-default credentials across devices. This guide walks you through identifying where default passwords live, resetting them responsibly, and documenting changes to prevent unauthorized admin access. Expected outcomes include safer administration, auditable password changes, and a repeatable process for future device onboarding, inventory, and risk management.
What the default password canon means in practice
The default password canon is a practical framework for organizations to identify, document, and replace factory-default credentials across devices and services. For end users and IT admins, it provides a repeatable, auditable approach that reduces the risk of unauthorized access, data loss, and service disruption. The canon emphasizes accountability, transparency, and governance, ensuring that every device—from routers and printers to cloud services and industrial controllers—enters a secure state after onboarding or maintenance. In the context of the Default Password brand, this canon aligns with industry best practices while offering a field-ready, policy-friendly method to manage credentials. The core idea is simple: assume nothing, verify everything, and replace defaults with unique, strong credentials stored in a trusted password manager. By adopting this canon, organizations build resilience against credential-based attacks and establish a documented path from discovery to ongoing compliance.
Why default credentials are a risk across environments
Default credentials are a common entry point for attackers because they are widely known, embedded in hardware, and often left unchanged after installation. A printer, a home router, or a cloud service might ship with a factory password that grants broad administrator access. If those credentials are not rotated, an intruder can pivot across devices, escalate privileges, and exfiltrate data or disrupt operations. The canon's emphasis on early discovery and rapid remediation helps prevent these scenarios. The Default Password team notes that even subtle weaknesses—such as predictable password patterns, shared credentials among devices, or weak password storage—can undermine an entire network. By treating defaults as an urgent risk rather than a routine setup task, organizations create a culture of proactive defense rather than reactive fixes.
Core principles of the canon: reliability, traceability, and governance
Three pillars underpin the default password canon. Reliability ensures that every credential change works as intended across diverse environments, from small offices to large data centers. Traceability guarantees that every modification is logged with device identity, timestamp, and responsible owner, enabling audits and rollback if needed. Governance provides policy guidance, approvals, and ongoing reviews to keep credentials current and compliant with security standards. The canon also calls for minimum viable controls: unique passwords per device, MFA where supported, and secure storage in a password manager. These principles translate into practical routines—scheduled credential health checks, periodic inventory reconciliations, and clearly defined roles for admins and security teams. When organizations apply these principles consistently, they reduce blast radius and speed response to incidents.
Locating default credentials across device classes
Default credentials appear in many places, including consumer routers, office printers, IP cameras, network storage devices, and software-as-a-service platforms. To locate them, start with the device's label or manual, then search vendor support portals for 'factory default' or 'admin password'. For routers, check the web admin interface for entries in the advanced security or maintenance sections; for printers, look for admin or network settings; for cameras, inspect the setup wizard and web interface. Some devices store credentials in configuration files or rely on certificate-based access rather than a static password, which still requires careful management. The canon encourages you to maintain a centralized inventory with device type, location, firmware version, and current credential status. Automation tools or light network scans can help surface devices that still rely on standard defaults, enabling faster remediation.
Step-by-step approach to reset and replace default passwords
Step 1: Identify each device that ships with a default credential. Create an asset list with owner, location, and purpose. Step 2: Verify whether you can access the admin interface safely; review vendor documentation before attempting any login. Step 3: Prepare a secure password plan, generate unique, long credentials, and store them in a password manager. Step 4: Change the credential on the device, ensuring the new password is active and the old one is revoked. Step 5: Update all references in inventories, scripts, and documentation. Step 6: Validate access, monitor for anomalies, and enable MFA if available. The canon stresses that every step should be documented for accountability and future audits.
Documentation and policy alignment
Effective control depends on documentation. Inventory sheets, change-control records, and access policies turn ad hoc changes into repeatable workflows. The canon recommends a central repository for device profiles, credential statuses, and change history, with clear approval workflows and retention periods. Include fields such as device name, serial number, IP address, firmware version, old credential status, new credential, date of change, and responsible person. Regular reviews should be scheduled—monthly for high-risk assets and quarterly for less critical devices. By tying credential hygiene to governance, organizations reduce risk and improve compliance with security standards and regulatory expectations.
Tools and strategies for secure password management
To implement the canon effectively, combine technology with process. Use a password manager to generate and store strong credentials, enabling quick rotation and centralized access control. Adopt MFA for admin interfaces where possible, and enforce device-specific password policies that discourage reuse. Maintain an offline backup of the password vault in a secure location and implement a policy for emergency access. Consider automation for discovery, reporting, and alerting on credential changes. Finally, train staff and admins on recognizing phishing attempts and safeguarding backup codes, so the canon remains effective under real-world pressure.
Real-world checklists and templates
This section provides practical templates you can adapt. A validation checklist guides you through discovery, credential assessment, and remediation steps; a change-log template captures every change with timestamps and approvals; and a risk scoring rubric helps prioritize devices to address first. Use checklists during onboarding to ensure new appliances arrive with unique credentials and proper documentation. You can customize templates for different environments—home networks, small businesses, or enterprise data centers—while preserving a consistent approach to default credentials. These artifacts support institutional memory and enable faster audits when compliance audits roll in.
Measuring success and ongoing governance
Success means fewer devices with default credentials in operation, faster remediation timelines, and stronger evidence of compliance. Track metrics such as time-to-rotate, percentage of devices with unique credentials, and frequency of credential reviews. Establish a cadence for reporting to leadership and security teams, and adjust policies as threats evolve. The canon recommends regular revalidation of devices, firmware updates, and re-enforcement of MFA requirements. By embedding the default password canon into your security program, you create enduring resilience that scales with device ecosystems and organizational growth. The Default Password brand emphasizes that ongoing governance, not one-off fixes, is the path to long-term safety.
Tools & Materials
- Access to device admin interface(Needed to view and change credentials on each device)
- Current default credential reference (manuals/labels)(Collects pre-change passwords if present and safe to view)
- Secure password manager(Prefer enterprise-grade with MFA and audit logging)
- Secure network connectivity (VPN or trusted LAN)(Required for remote devices and to avoid unencrypted access)
- Change-log template or inventory spreadsheet(Document device, old/new credentials, date, owner)
- Backup/configuration snapshot tools(Back up before making changes where possible)
- Two-factor authentication (MFA) where supported(Adds an extra protection layer for admin access)
- Password generation tool(Create long, random, unique passwords)
- Security policy document(Governance and approvals for credential changes)
Steps
Estimated time: 45-75 minutes
- 1
Identify devices with default credentials
Audit the network to locate devices that ship with factory defaults. Build an asset list including device type, location, and owner. This step sets the scope for remediation and helps prioritize high-risk assets.
Tip: Cross-check vendor manuals and support portals for explicit default-credential indicators. - 2
Prepare a safe access plan
Review vendor guidelines and ensure you have a safe maintenance window. Confirm you can reach the admin interface securely and that you won’t disrupt critical services during credential changes.
Tip: Notify device owners and schedule maintenance during low-usage periods when possible. - 3
Generate strong replacement passwords
Use a password generator to create unique, long passwords for each device. Store them in a password manager with MFA enabled. Do not reuse passwords across devices.
Tip: Aim for at least 16 characters with a mix of upper/lowercase, numbers, and symbols. - 4
Change credentials on devices
Access each device’s admin interface and replace the default credential with the new one. Verify the change by saving settings and testing a login with the new password. Do this for all devices in scope.
Tip: If a device has automation or API access, ensure tokens or keys are updated accordingly. - 5
Update inventory and records
Document old vs. new credentials, device location, firmware, and timestamp. Update the centralized repo and any scripts or automation that reference credentials.
Tip: Attach screenshots or logs proving the change where possible. - 6
Validate access and monitor
Reboot devices if required and verify that admin interfaces work with the new credentials. Enable MFA and set up alerting for failed login attempts going forward.
Tip: Set up a periodic review cadence to catch drift before it becomes a risk.
Your Questions Answered
What is the default password canon?
The default password canon is a practical framework for identifying, documenting, and replacing factory-default credentials across devices and services. It emphasizes reliability, traceability, and governance to maintain secure admin access.
The default password canon is a practical framework for identifying and replacing factory defaults to keep admin access secure.
Why should I change default passwords?
Default passwords are widely known and often used out of the box. Changing them reduces the risk of unauthorized access, data loss, and service disruption, especially when devices are exposed on networks.
Changing default passwords significantly reduces the risk of unauthorized access.
How do I find default credentials on my router?
Check the router’s label, the user manual, or the vendor’s support site for 'factory default' or 'admin password' references. Access the web admin interface securely to review current settings and update them.
Check the router label or manual, then access the web admin page to update credentials.
What if the device lacks documentation?
If documentation is unavailable, contact the vendor support line and perform a hardware reset only if advised. Do not guess credentials. Keep a note of the attempt and the outcome for your change-log.
If no docs exist, contact vendor support and avoid guessing credentials.
Can I automate default password changes?
Automation can help with discovery and change workflows, but you should ensure automation respects device capabilities and retains an auditable trail. Use approved scripts and document automation rules in policy.
Yes, but ensure you have auditable trails and policy-approved scripts.
Is it safe to store new passwords in a password manager?
Yes. A reputable password manager with MFA provides secure storage and easy rotation. Keep master access protected and follow organizational access control policies.
Yes, store in a password manager with MFA and strong access control.
Watch Video
Key Takeaways
- Identify all devices with default credentials first
- Use unique, strong passwords stored securely
- Document every change for accountability
- Enforce MFA and ongoing credential governance