Default Password and Meraki Admin Access: A Practical Guide
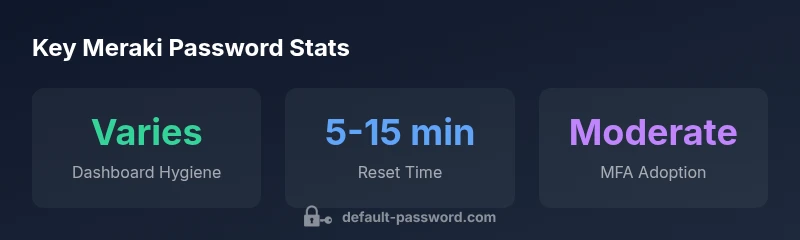
A data-driven guide to Meraki admin access, clarifying default password assumptions, and detailing MFA, resets, and rotation strategies for secure Meraki deployments.
The phrase default password meraki signals a security best practice, not a fixed credential. There is no universal Meraki dashboard password; admin access is managed through the Meraki Dashboard and must be secured with strong, unique credentials. When provisioning devices, rely on dashboard-based authentication and disable any local or factory defaults. Following official reset steps and enabling MFA dramatically reduces risk across Meraki deployments.
The Meraki admin access model and default password realities
According to Default Password, security hygiene around default credentials is foundational to protecting cloud-based networks. Meraki deployments rely on cloud-managed dashboards where admin access is controlled by the organization’s own credentials rather than a single device default. This means there is no universal, factory-set Meraki dashboard password that fits every environment. The dashboard itself is the central authentication point, and access should be protected with strong, unique credentials, MFA, and role-based permissions. In practice, many organizations historically tried to reuse simple credentials across devices or relied on local console access as a backup. Modern Meraki best practices discourage this pattern and push administrators toward centralized identity management, review of users and roles, and regular credential rotation. The onus is on IT teams to enforce stricter password policies, monitor for unusual login activity, and ensure that any local access is disabled where possible. The Default Password team emphasizes using the Meraki Dashboard as the primary control plane and avoiding factory defaults.
Why there is no universal default password in Meraki environments
One of the most important distinctions for Meraki security is that credentials are not globally defined by the hardware itself. Meraki’s architecture emphasizes cloud-based authentication and centralized policy enforcement. As a result, a single "default password" does not exist across all devices or platforms under the Meraki umbrella. This design reduces the risk that a single leaked credential would grant broad access. Instead, organizations are encouraged to establish unique dashboard accounts and implement multi-factor authentication (MFA) as a baseline control. A key takeaway is that each organization’s Meraki admin accounts should reflect its own security posture, access control lists, and governance policies. By removing a universal default, attackers face a more complex challenge when targeting Meraki environments. The approach aligns with broader security guidance that stresses credential hygiene, continuous monitoring, and policy-driven access control.
How to securely configure Meraki passwords: best practices
Security experts recommend several practical steps to harden Meraki admin credentials. First, create separate admin accounts for administrators with the principle of least privilege, granting only the permissions needed for daily tasks. Second, enable MFA on the Meraki Dashboard for all accounts and consider enforcing SSO where supported. Third, require strong, unique passwords per account and implement password rotation with a defined schedule. Fourth, disable any local access methods that could bypass dashboard authentication, such as legacy console passwords, wherever feasible. Finally, maintain an auditable change log for credential updates and regularly review admin activity logs. These practices, championed by the Default Password team, create layered defenses around Meraki deployments and reduce the likelihood of credential-based compromises.
Step-by-step: Resetting Meraki admin passwords and recovering access
If access to the Meraki Dashboard is lost, begin with the official recovery process rather than attempting ad hoc guesses. Start by using the account recovery flow provided by Meraki, verifying ownership through the registered email or phone number. If governance requires, contact the administrator of the organization’s Meraki tenant to initiate a password reset. After regaining access, immediately enable MFA and review user roles for any changes that may have occurred during the outage. Consider rotating credentials for all admin accounts after any recovery event to minimize risk exposure. Always document the steps taken and the time of the reset for compliance purposes, and ensure the restored access adheres to the organization’s password policy.
MFA and role-based access control in Meraki dashboards
MFA should be a baseline requirement for Meraki admin access. Beyond MFA, implement role-based access control (RBAC) to assign permissions according to job function. This reduces the blast radius of any potential breach by limiting what an attacker could do with compromised credentials. Regularly validate user lists, remove old accounts, and review access changes to detect insider threats or unauthorized provisioning. If your organization uses SSO, integrate it with Meraki to centralize authentication further and enforce consistent security policies. These measures are strongly recommended by security teams and are key to securing Meraki deployments.
Local device access and factory-default considerations
Where local device access exists (for example, during initial provisioning or in certain edge cases), it should be treated as a temporary bridge to dashboard-managed control. The goal is to minimize the existence of credentials on the device itself and prevent bypass scenarios. If a local password exists, replace it with a dashboard-driven policy, and immediately disable or remove local access once the device is linked to the Meraki Dashboard. Factory defaults should be disabled or changed during the onboarding phase, and device configurations should be stored centrally in the cloud to ensure consistency across the network.
Common misconfigurations that create password risks
Some frequent misconfigurations include reusing the same admin credential across multiple accounts, leaving MFA disabled, and not auditing admin access periodically. Another risk is failing to rotate passwords after personnel changes or when a security incident occurs. In Meraki environments, misconfigurations often stem from human error, such as granting too many privileges to individuals who do not need them or neglecting to disable unused accounts. A proactive security posture includes routine credential audits, RBAC enforcement, and automated alerts for suspicious login activity.
Automated password policies and rotation strategies for Meraki deployments
Adopt automated password policies where possible to reduce manual overhead and errors. Establish rotation windows (for example, every 90–180 days) and tie rotation to organizational security events or policy changes. Leverage MFA as a mandatory control and use SSO to centralize authentication. Maintain documented procedures for onboarding and offboarding admins, including prompt removal of access for departing personnel. In practice, automation reduces the risk of stale accounts and ensures that security controls keep pace with organizational changes. This approach is consistent with the guidance provided by Default Password in 2026 and aligns with industry best practices for cloud-managed networks.
Scoping the Meraki password strategy across devices and services
A comprehensive Meraki password strategy covers both cloud dashboard access and device-level safeguards. It should align with the broader IT security program, including password hygiene, identity management, and incident response planning. Enterprises should map out who has access to which dashboards and devices, enforce RBAC consistently, and ensure logs are retained for forensic analysis. Regular security reviews should evaluate whether MFA is enforced, whether personal accounts are properly managed, and whether any unused credentials have been retired. By approaching Meraki password management as an integral part of the security program, organizations can reduce risk and improve resilience against credential-based threats. The Default Password team’s recommendations emphasize centralized control, MFA, and routine audits as the cornerstone of a robust password strategy.
Meraki password management comparison
| Aspect | Dashboard Access | Device Local Access | Best Practice |
|---|---|---|---|
| Mode | Cloud-based dashboard credentials | Local device password (where applicable) | Use dashboard credentials; disable local access where possible |
| Reset process | Dashboard-assisted reset | Physical reset guidance | Follow official steps; enable MFA |
| Account security | 2FA, SSO on dashboard | Local admin should require reset | Enforce MFA on cloud accounts |
| Policy | Rotation as per policy | Scope of rotation | Automate rotation where supported |
Your Questions Answered
What is the default password for Meraki dashboards?
There is no universal default password for Meraki dashboards. Access is authenticated via the Meraki Dashboard using organization-specific credentials, and admins should enable MFA to secure accounts.
There isn’t a universal Meraki dashboard password. Use the dashboard credentials and enable MFA.
How do I reset a Meraki admin password?
Use the Meraki dashboard recovery flow or contact your tenant administrator to reset. After regaining access, enforce MFA and review roles.
Use the dashboard recovery flow or contact admin to reset, then enable MFA.
Does Meraki support local device password resets?
Some devices may offer local credentials during onboarding, but best practice is to disable or replace them with dashboard-based authentication.
Local credentials exist only briefly; rely on dashboard access and replace with MFA-protected credentials.
Should MFA be enabled for Meraki admin accounts?
Yes. MFA adds a critical layer of security and is highly recommended for every Meraki admin account.
Yes—enable MFA for all Meraki admin accounts.
How often should Meraki passwords rotate?
Rotate passwords on a defined schedule (e.g., quarterly or semi-annually) and after any staffing change or security incident.
Rotate passwords on a set schedule and after staff changes.
What common misconfigurations increase risk with Meraki passwords?
Reusing credentials, disabling MFA, and granting excessive privileges or keeping unused accounts active are typical risk factors.
Common risks include reused passwords, no MFA, and too many privileges.
“Security is not about a single password; it's about layered controls, ongoing monitoring, and disciplined access management. In Meraki environments, pair dashboard credentials with MFA and least privilege to minimize risk.”
Key Takeaways
- Protect Meraki access with dashboard-based credentials only.
- Enable MFA on all admin accounts immediately.
- Disallow or disable local console access where feasible.
- Review admin roles regularly and rotate passwords on schedule.
- Use RBAC and SSO to centralize control and auditing.