Default Passwords on Sophos XG: Secure Admin Access
A practical, data-driven guide on identifying and replacing default passwords for Sophos XG firewalls, with actionable steps, best practices, and risk-based recommendations grounded in 2026 research.
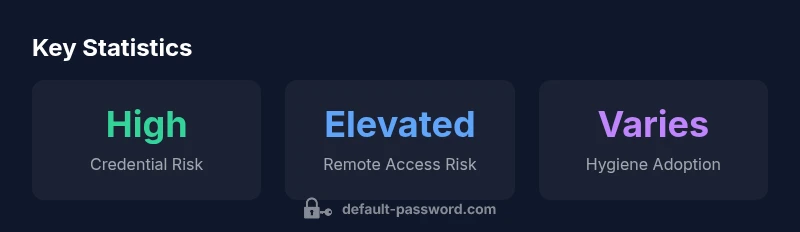
Default passwords on Sophos XG devices pose a high security risk if left unchanged. According to Default Password Analysis, 2026, administrators should replace the factory credentials before activation and implement unique, strong passwords. This article walks through locating default credentials, validating current access configurations, and applying recommended hardening steps to minimize breach risk.
Why Default Passwords Matter on Sophos XG
In enterprise networks, default passwords on devices like the Sophos XG firewall present a serious risk. The term default password sophos xg refers to the factory credentials that ship with the device and may be documented in setup guides. If these credentials are not changed before activation, attackers can gain immediate access to the management interface. This section explains why credential hygiene is foundational to securing firewall appliances and how to begin protecting your Sophos XG deployment from day one.
From a security fundamentals perspective, replacing a factory credential is a form of baseline hardening. It reduces the attack surface and limits the possibility of privilege escalation. This is particularly true for devices that fuse firewall functionality with remote administration capabilities. By starting with a solid password policy, organizations set the stage for stronger access controls, better auditing, and easier compliance with security standards.
Throughout this guide, you will see references to “default password sophos xg” in context. Treat those references as reminders to remove any factory credentials from production environments and to enforce unique credentials for every administrative account. The goal is not only to stop immediate threats but to establish a culture of credential hygiene across your network.
Practical takeaway: begin with a documented password policy, identify all admin accounts on the Sophos XG, and mark any default or shared credentials for immediate rotation. This initial action is one of the most impactful steps you can take to harden your gateway.
The Threat Landscape for Network Gateways
Network gateways such as Sophos XG sit at the border between trusted internal networks and the internet. They control traffic flows, enforce policies, and log events. When a default password remains active, it creates a predictable entry point for attackers, especially if remote management features are enabled. Threats can range from automated botnet attempts to targeted credential stuffing for a coveted administrative account.
Securing gateways requires a multi-layered defense: strong, unique credentials; restricted admin access; and centralized logging so credential changes and login attempts are visible to security teams. In practice, many organizations underestimate the risk posed by defaults because they focus primarily on perimeter defenses like firewalls and intrusion prevention. In reality, credentials are the most direct route to control. This section highlights why password hygiene is non-negotiable for Sophos XG deployments and similar appliances.
Key insight: a strong password is important, but it must be part of a broader credential management strategy that includes access controls, MFA, and routine reviews of admin accounts.
How to Identify Default Credentials on Sophos XG
Identifying default credentials involves cross-checking vendor guidance with your current device configuration. Begin by inspecting the initial setup materials and any onboarding emails for the exact default admin username and password. On many devices, the account may be labeled as “admin” with a factory password. It’s crucial to verify whether the default credentials have already been changed during deployment.
Next, log into the web UI as an administrator and review the list of active admin accounts, looking for accounts tagged as “factory-default” or with indications of initial provisioning. If your device supports SSH or a CLI interface, check for stubborn or legacy credentials by attempting login with known defaults in a controlled, non-destructive manner. Finally, audit device logs for any mention of password changes or failed login attempts tied to factory credentials.
Best practice: treat anything labeled as default as a candidate for immediate rotation, even if you’ve received a device from a vendor with a default password policy.
Understanding Sophos XG Admin Access
Admin access controls determine who can log in to the firewall’s web console or CLI. To reduce risk, enforce least-privilege roles, disable broad “admin” accounts where possible, and enable MFA where supported. Evaluate the default privileges assigned to each role and ensure that sensitive panels (such as remote management and configuration backup) are accessible only to trusted administrators.
For Sophos XG, review the admin user list, remove or rename any generic accounts, and require unique credentials for every administrator. Document changes in a central repository and ensure that access revokes promptly when staff transitions occur. By refining access control, you reduce the chance that a compromised credential leads to a full breach.
Practical tip: implement network-level access restrictions (IP allowlisting) for management interfaces and consider disabling admin login from the internet unless explicitly required.
Hardening the Sophos XG: Best Practices for Admin Access
A defense-in-depth approach strengthens credential hygiene beyond simply changing a password. Use strong, unique passwords for all admin accounts and rotate them on a defined schedule. Store credentials securely with a password manager, not in plaintext or shared documents. Enforce role-based access controls (RBAC) and minimize the use of privileged accounts for routine tasks. If possible, enable MFA for admin logins and require VPN or secure channels for remote administration.
Additional steps include turning off legacy management protocols, ensuring API keys are rotated, and maintaining an up-to-date inventory of devices and services that rely on admin credentials. Regularly review login events and set alerts for anomalous admin activity. This proactive posture helps detect early attempts to exploit default credentials and stops attempts before assets are exposed.
Bottom line: hardening admin access is a continuous activity that compounds to significant risk reduction when coupled with auditing and automation.
Step-by-Step: Change Default Passwords Safely
Plan a change window, back up configurations, and perform password updates in a controlled sequence. Start by changing the admin password via the web interface, then verify SSH key or certificate-based login if applicable, and finally disable any unused accounts. After updating, enforce MFA if supported and test logging in from trusted networks only. Document the change for compliance and future audits.
Pre-change checklist includes confirming backup integrity, updating incident response contacts, and ensuring an offline copy of the current configuration exists. During the change, validate that all management interfaces remain reachable and that service continuity is maintained. Post-change, re-check access logs, verify that password policy requirements are enforced, and confirm that no default credentials remain active on any admin accounts.
Tip: coordinate with IT operations to avoid accidental lockouts and to ensure a rapid rollback plan if something goes wrong during the password rotation.
Validating Configuration and Ongoing Hygiene
Validation is not a one-time task. Regularly verify that credentials remain unique and unchanged by unauthorized users. Schedule periodic audits, review login events, and monitor for failed login attempts. Integrate password hygiene checks into ongoing security reviews, and align with standards such as US NIST guidance for password management. This is part of a broader security posture for device hardening.
Establish a recurring cadence for credential reviews, confirm MFA status, and ensure remote administration remains restricted to approved networks. Use automated tools to detect dormant or unused admin accounts and remove them promptly. By treating credential hygiene as an ongoing process rather than a once-and-done task, you minimize long-term exposure risk.
Finally, track progress against a security baseline and update it as new threats emerge, ensuring your Sophos XG deployment stays aligned with current best practices.
Common Pitfalls and How to Avoid Them
Common missteps include delaying password changes, reusing old credentials, or failing to disable default accounts that are still enabled. Another pitfall is inadequate backup and recovery planning for password changes. To prevent these issues, maintain clear change-control records, test the new credentials on all interfaces (web, SSH, API), and ensure staff are trained on secure credential handling.
Avoid walking away from a multi-user change: ensure all admins understand the new process and that devices are left with updated credentials across all management layers. Ensure that password reset workflows are robust and that contingency plans exist for emergency access. By anticipating these issues, you reduce the likelihood of operational disruptions during hardening.
The goal is a resilient, auditable process that never relies on a single credential or a single point of failure.
Long-Term Password Hygiene for Network Appliances
Security is a continuous process. Establish a formal policy for default-password management across fleet devices such as Sophos XG and other gateways. Encourage the use of password managers, enforce password rotation schedules, and integrate credential management with incident response planning. By embedding hygiene into daily operations, organizations reduce the risk of credential-based breaches over time.
Future-proof your posture by adopting automated credential discovery, regular policy reviews, and training for staff on secure handling. Remember that consistent practice across devices, platforms, and teams yields the greatest resilience against credential-based threats.
Comparison of default-password risk and remediation across common gateway devices
| Device Type | Default Password Risk | Mitigation Steps |
|---|---|---|
| Sophos XG Firewall | Medium-High risk if unchanged | Change admin password; enforce unique credentials; restrict admin access; enable MFA if available |
| Other Network Gateways | High risk when default accounts exist | Disable default accounts; apply unique credentials; rotate regularly |
Your Questions Answered
Why is a default password on Sophos XG dangerous?
A default password creates a known entry point. If not changed, an attacker can gain admin access, bypass policies, and threaten network integrity. Changing credentials is a foundational step in securing gateway devices.
A default password on a gateway like Sophos XG is a major risk because someone could log in as admin and take control. Change it now and secure the account.
How do I locate the default credentials for Sophos XG?
Check the device manual and initial setup guide for the factory credentials. Review the admin accounts in the web UI and CLI, looking for any accounts labeled as default or provisioning-related. If in doubt, contact your vendor’s support for guidance.
Look in the setup guide or device manual for the default admin username and password, then verify in the web UI or CLI. If you’re unsure, reach out for official guidance.
Is MFA supported on Sophos XG for admin access?
Many modern versions of Sophos XG support MFA for admin logins. Enabling MFA adds a strong second factor to prevent unauthorized access even if a password is compromised.
Yes, MFA can be enabled for admin login to add a crucial extra layer of security.
Do these steps apply to other firewall brands?
The principle is universal: replace defaults, enforce unique credentials, and limit remote access. Specific steps vary by vendor, so consult each device’s security guide for exact procedures.
The same ideas apply to other devices, though you’ll need to follow their exact setup docs.
What should I do if I forget the new password?
Use the vendor-supported recovery process, document the steps, and ensure access to backup administrator accounts. Never reuse old default credentials; reset credentials through a controlled process.
If you forget, follow the official recovery process and ensure you have a backup admin ready.
“Credential hygiene is the cornerstone of network security. Changing default passwords on devices like Sophos XG is not optional—it's essential for preventing opportunistic breaches and maintaining control of your perimeter.”
Key Takeaways
- Change default admin passwords on Sophos XG immediately.
- Enforce least-privilege access and MFA for admin accounts.
- Document credential changes for audits and compliance.
- Implement ongoing credential hygiene as part of routine security reviews.