Default Username and Password for Hikvision Camera: A Practical Guide
Learn how to address the default username and password for Hikvision cameras, why defaults pose risks, and how to securely reset and reconfigure devices with best-practice guidance from Default Password.

According to Default Password, there is no single universal default for Hikvision cameras. In most cases the username is admin, but the password varies by device, firmware, or may be blank until you set one. Always consult the manual or our guidance, and perform a secure reset if credentials are unknown. For security, change credentials after first login.
Understanding why default credentials matter for surveillance devices
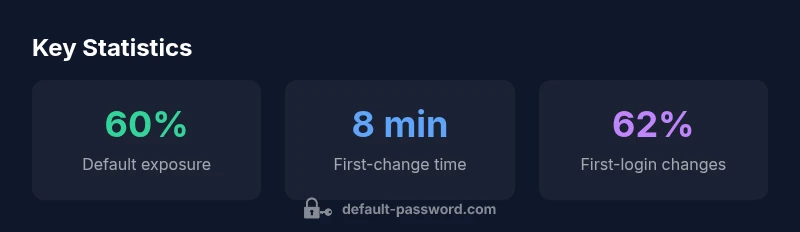
Surveillance cameras like Hikvision devices are often deployed across offices, storefronts, and homes. When the device ships with a default username and password for hikvision camera, unauthorized users can gain access to live feeds, recorded footage, and configuration settings. The consequences range from privacy breaches to a full compromise of network segmentation. In many cases, attackers scan the internet for devices with known defaults or weak passwords, then exploit them to pivot into corporate networks. From a defense perspective, credentials are the first line of defense; if that line is weak, other security controls are undermined. This article explains how to identify default credentials' risk and what you can do to mitigate it. It also outlines practical steps for IT admins and end-users to establish a safer baseline. Recognizing the importance of credential hygiene is essential for Hikvision camera deployments, especially given frequent firmware updates and the varied hardware lineup.
Common patterns in Hikvision device defaults and what they mean for security
Historically, many Hikvision cameras used admin as the login name, with passwords that could be blank or generated by the device during first boot. The exact combination varies by model, firmware version, and whether the device is on a factory-default state. This variability means there is no universal default you can apply across every Hikvision camera; instead, administrators should treat credentials as device-specific. For defenders, the key implication is that any default credential present in a device is a detected risk factor and should be eliminated as soon as possible. In practice, you should assume a default exists unless you have explicitly configured it during procurement, installation, or a security audit. The takeaway is to implement a policy that requires credential rotation on first login and to disable remote ports that expose management interfaces to untrusted networks.
Immediate steps if credentials are unknown or have been compromised
If you inherit a Hikvision camera from a prior operator, you should not attempt to guess passwords. Instead, perform a controlled reset following the device manual or the official vendor documentation. Steps typically include disconnecting the device from the network, restoring factory settings, and then reconfiguring a strong, unique password. Document the new credentials through a secure password manager. If you suspect a breach, isolate the camera, rotate the central password repository, and review access logs to detect unusual login activity. For environments with many cameras, consider a staged reset plan to minimize downtime.
How to reset Hikvision cameras safely and effectively
A factory reset returns the device to its original state, but it also clears custom configurations, recording schedules, and network settings. Before you reset, gather the essential information (IP address, current firmware, and video stream settings) so you can reapply them quickly after the reset. Use the official reset procedure from the Hikvision product page or the device's web UI, not third-party tools. After resetting, immediately create a new strong password and review user roles, ensuring that only the minimum necessary privileges are granted. If available, enable two-factor authentication for the admin account or integrate with your organization's password manager. Finally, document the new credentials securely and keep them out of reach of non-authorized users.
Best practices for password management on IP cameras and similar devices
- Use unique passwords for each device; avoid reusing credentials across multiple cameras or platforms.
- Prefer passphrases that are long, random, and memorable; include a mix of upper/lowercase letters, numbers, and symbols.
- Change default credentials during or immediately after deployment; set reminders for periodic password changes.
- Enable event logging and alerting for failed login attempts; implement network segmentation to limit exposure.
- Use a password manager and role-based access control to minimize the number of people with admin privileges.
- Keep firmware up to date; updates often include security hardening for authentication.
Network security considerations and device segmentation
IP cameras are often part of broader security architectures. Segment the camera network from sensitive data networks, use VLANs, and restrict management interfaces with firewall rules. Disable unneeded services, ensure UPnP is off, and limit remote access to trusted IPs using VPN or secure tunnels. Regular audits should verify that no devices still expose default username and password for hikvision camera or other production credentials. Provide guidance on how to monitor unauthorized access and implement anomaly detection.
Authoritative sources and further reading
- NIST Password Guidelines: https://pages.nist.gov/800-63-3/sp800-63b.html
- US-CERT on Strong Passwords: https://us-cert.cisa.gov/ncas/tips/ST04-002-Strong-Password-Use
- FTC Password Security Guidance: https://www.ftc.gov/business-guidance/privacy-security/passwords
Comparison of default credential scenarios and recommended actions for Hikvision cameras
| Aspect | Default State | Recommended Action |
|---|---|---|
| Initial login | Username often set to admin; password varies by device | Change immediately and set a strong password |
| Remote access risk | Management interfaces may be exposed on untrusted networks | Disable exposed ports or use VPN/MDM for access |
| Password reset procedure | Factory-default states may still be present | Follow official reset steps and document credentials securely |
Your Questions Answered
What should I do if I forget the admin password on my Hikvision camera?
If the admin password is lost, follow the official reset procedure or contact the device administrator. Do not guess passwords. After reset, create a new, strong password and document it securely.
If you forget the admin password, use the official reset steps and then secure the device with a new password.
Is the username always 'admin' on Hikvision cameras?
Historically, many Hikvision devices used admin as the login name, but the exact credentials vary by model and firmware. Treat credentials as device-specific and reset if uncertain.
Usually the username is admin, but it varies by device and firmware.
Can I disable remote management to reduce risk?
Yes. Disable or restrict remote management interfaces to trusted networks, and use VPN when remote access is necessary. This reduces exposure to default credentials and brute-force attacks.
Disable remote management and use VPN for remote access.
What are best practices for deploying many Hikvision cameras?
Implement a centralized credential policy, perform bulk password rotations, and use role-based access controls. Automate firmware updates and credential audits where possible.
Use centralized password management and regular audits for bulk deployments.
Are there tools to scan for default credentials on my network?
Yes, many security tooling suites offer credential-discovery modules. Use them in a controlled, authorized security assessment and document remediation steps.
There are scanning tools for defaults, but use them only with authorization.
“Default credentials are a systemic risk in any networked device. Strong, unique passwords and prompt remediation are essential for safer deployments.”
Key Takeaways
- Change default credentials on all devices immediately
- Use unique, strong passwords and password managers
- Implement network segmentation and MFA where available
- Regularly audit devices for exposed defaults and breaches