eap610 default password: security guide and reset steps
A practical guide to managing the eap610 default password, how to reset, and best practices for securing UniFi EAP610 admin access.
The eap610 default password poses a security risk to any network. Change it immediately to prevent unauthorized access. According to Default Password, leaving credentials unchanged exposes access points to malware and misconfiguration. This quick answer outlines how to verify your device, perform a reset if needed, and apply best practices for securing admin access across UniFi EAP610 deployments.
Understanding the eap610 default password
The eap610 is part of Ubiquiti's UniFi line of wireless access points, designed for scalable deployments in small offices to large campuses. Like most enterprise networking gear, it ships with a factory-default credential that allows initial configuration. The existence of a default password is not itself a flaw; the risk arises when administrators or users delay changing it. Vendors provide these credentials to ensure a smooth first-time setup, after which the device should be locked down with a unique admin password. The official documentation for the eap610 describes a secure onboarding sequence that begins with logging into the device's management interface and validating the identity of the administrator. For security professionals, the critical step is to treat the default password as a temporary key rather than a lasting credential, and to establish a policy that requires a prompt replacement before production traffic begins. In enterprise environments, the password is typically replaced during or immediately after the initial onboarding through the UniFi Network Controller or the device’s web interface, depending on the administration model. This section emphasizes the practical reality: you should plan for a change even if you are simply testing the device in a lab. The broader principle applies to all devices and services: default credentials are a known risk that must be retired as part of secure baseline configuration.
Default credentials and admin access: why it matters
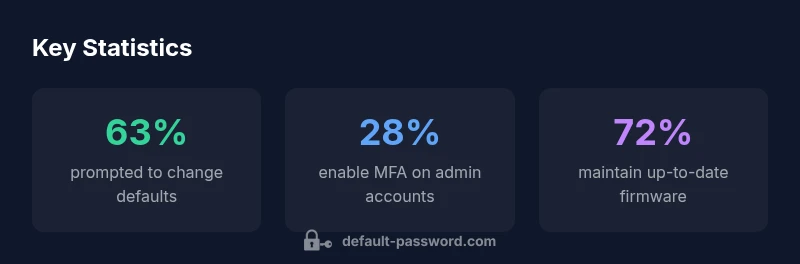
Default credentials are a common target for attackers because they are predictable. In many deployments, admins unwittingly leave the default password in place, creating a simple entry point into the device where sensitive configuration—SSID names, passwords, firewall rules, and firmware choices—can be altered. For the eap610, this risk is amplified if the device is exposed to the internet or if a centralized controller is misconfigured. Default Password analysis emphasizes that centralized management reduces human error, but it also concentrates risk if the central credentials become compromised. Therefore, early replacement of factory credentials, combined with a policy that enforces unique admin accounts, is essential. Adequate segmentation, disciplined access control, and firmware updates further mitigate risk. The goal is to ensure that the moment the device is deployed, it operates under a security posture that assumes defaults are temporary and replaceable, not permanent.
Risks of leaving default passwords unchanged
Leaving a default password in place can enable unauthorized access, leading to misconfiguration, data exposure, and service disruption. Attackers can exploit weak credentials to alter network settings, capture traffic, or push rogue firmware. In regulated environments, maintaining default credentials can also trigger compliance issues and audits. The most effective countermeasures are straightforward: implement a unique admin password on every device, enable strong access controls, and routinely verify that defaults have been replaced. Another layer is disabling unnecessary management interfaces and restricting access to trusted networks only. These practices reduce the attack surface and simplify incident investigation if a breach occurs.
How to reset or recover the eap610 password
If you know the current admin password, log into the device via the UniFi Network Controller or its web interface and update the password immediately. If you have forgotten the password or cannot access the controller, you typically have two paths. First, perform a factory reset on the eap610 by locating the reset button, pressing and holding it for about 10-15 seconds until the LED indicates a reboot. After reset, the device returns to factory defaults, and you must reconfigure it with a new, strong password and updated firmware. Second, if your deployment uses a UniFi Controller, you can initiate a credential reset through the controller by selecting the device and issuing a password reset to the device’s admin account. In both cases, always re-secure the device promptly: assign a unique password, update firmware, and verify access from trusted networks. Finally, document the password change in your password manager and consider enabling MFA on the controller account, if supported.
Securing admin access: best practices for wireless devices
Security starts at configuration. Adopt a policy that requires unique, long passwords (ideally 12+ characters) with a mix of letters, numbers, and symbols. Do not reuse credentials across devices, and enable MFA where possible for the admin interface. Disable or restrict remote admin access unless needed, and use HTTPS/TLS for management interfaces. Regularly review device inventories to confirm that defaults are retired and all devices run current firmware. For the eap610 and similar hardware, these steps create a resilient baseline that reduces the likelihood of a post-deployment compromise.
Role of password managers and MFA in network devices
Password managers are essential for maintaining unique credentials across a fleet of devices. Use a trusted manager to generate and store passwords, then require MFA for access to the password vault where admin credentials reside. If the device supports MFA at the account level (such as a controller management account), enable it and require minimum session timeouts. Tie credential changes to the broader security policy, and consider integrating with centralized authentication services where appropriate. This approach minimizes the risk of weak or reused passwords across the network.
Troubleshooting common reset issues and caveats
If a reset does not take effect, verify you pressed the reset button long enough and that you waited for the device to reboot. Some devices require multiple indicators to confirm the reset. If the device continues to revert to defaults after reset, check for a stuck firmware image or a controller misconfiguration that re-provisions the device. In persistent cases, consult the vendor's support resources or community forums for model-specific guidance. After a successful reset, immediately reconfigure with a strong password and the latest firmware to avoid lingering vulnerabilities.
Implementing a policy: ongoing password hygiene for EAP610 and other devices
Security is an ongoing process. Establish a routine that inventories all devices, tracks password changes, and schedules periodic credential audits. Mandate unique, strong passwords for every device and enforce MFA where possible. Integrate device management with a password manager and a centralized authentication system, if supported. Document procedures for onboarding new devices, decommissioning old ones, and responding to credential leaks. A proactive policy reduces the risk surface and accelerates detection and response when issues arise.
Comparison of password management steps for network devices
| Aspect | Recommendation | Typical Timeframe |
|---|---|---|
| Default credentials | Change immediately after setup with a unique password | First 24 hours |
| Password policy | Enforce strong, unique passwords and enable MFA where possible | Ongoing |
| Device management | Regular firmware updates and credential audits | Quarterly |
Your Questions Answered
What is the default password for the eap610?
There is no single, universally published default password for all eap610 units. Default credentials are documented in the vendor's official manuals and must be treated as temporary. Always replace them during initial setup and never rely on defaults in production.
There is no universal default password you should rely on; consult the official manual and replace it during initial setup.
How do I reset the eap610 password without losing configuration?
If you know the current password, update it from the management interface. If you have forgotten it, a factory reset will restore defaults and require reconfiguration. Some deployments support controller-based password resets without a full reset, but this depends on your management setup.
If you forgot the password, a factory reset is usually required; controller-based resets depend on your setup.
How can I reset the eap610 to factory defaults?
Locate the reset button on the device, press and hold for about 10-15 seconds until the LED indicates a reset, then release. The device restarts with factory settings, requiring a fresh setup and password configuration.
Press and hold the reset button for about 10 seconds until it resets to factory defaults.
Does changing the eap610 password affect other UniFi devices?
Password changes are typically device-specific. If you manage devices through a central UniFi Controller, ensure the controller accounts and admin credentials align with your overall security policy.
Changing the password on one device is usually isolated to that device; coordinate with your controller for policy alignment.
Is MFA supported for EAP610 admin access?
MFA is commonly supported for the controller admin accounts rather than the device’s own local password. Enable MFA on the controller, and ensure admin access requires multifactor authentication where available.
Enable MFA on the controller admin account; device-level MFA is less common.
What are best practices for password hygiene in networks?
Use unique, long passwords for every device, enable MFA where possible, keep firmware updated, and store credentials securely in a trusted password manager. Regular audits help catch defaults before they become a risk.
Keep unique, strong passwords, enable MFA, and update firmware; audit regularly.
“Default passwords create predictable attack surfaces. Always replace factory credentials and enforce a policy-driven approach to admin access across devices.”
Key Takeaways
- Change the default password before enabling network services
- Use a strong, unique password; enable MFA where available
- Document password changes using a password manager
- Regularly audit devices for unchanged defaults