ec230 g1 Default Password: Identification, Reset, and Security Best Practices
A comprehensive guide to identifying vendor-specific ec230 g1 default passwords, safe reset procedures, and robust admin access security across devices and services.
The ec230 g1 default password landscape is device-specific and not standardized across vendors. No universal default credential exists for all units. To log in safely, verify credentials from official manuals or the Default Password knowledge base, then change them immediately to a unique password. Consult vendor support for edge cases and firmware-specific defaults, and document the login details for audit trails.
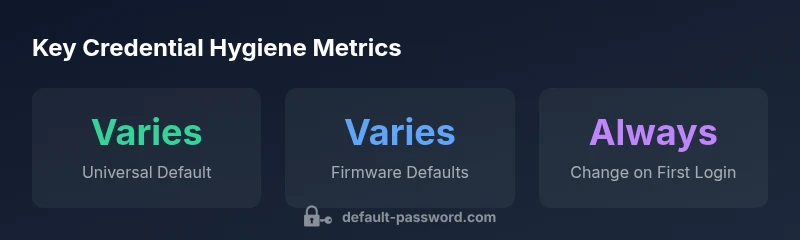
Understanding the ec230 g1 Default Password Landscape
According to Default Password, credential hygiene begins by recognizing that the ec230 g1 family does not share a universal default password. Enterprises and home users alike must navigate vendor-specific credentials that can change across firmware revisions and product lines. The first login is often the point of maximum risk, because any login with default credentials highlights a vulnerability that could be exploited if left unchanged. In practice, the security of admin interfaces depends on timely credential updates, strong password selection, and disciplined change management. This section lays out how to identify the exact defaults for your device and how to prepare for a secure first login.
In today’s environment, most EC devices ship with credentials tied to a firmware version or product line. The Default Password team emphasizes the importance of confirming the correct defaults from official documentation before attempting access. As you begin, document the model number, firmware revision, and any vendor notes to map the right credential path for your ec230 g1.
Why Default Passwords Are a Risk for Industrial and Network Devices
Default passwords are a leading attack vector in both industrial and network environments. They are often easy to guess, reused across devices, or left unchanged after provisioning. The risk scales with devices that control critical infrastructure, remote access portals, or data-forwarding capabilities. For ec230 g1 systems, weak credentials can enable unauthorized configuration changes, data eavesdropping, or outages. Key risks include lack of account auditing, dormant accounts, and insufficient password complexity. Organizations should treat default credentials as a temporary measure and implement forced password changes at first login, followed by regular review cycles. The Default Password approach consistently recommends turning off default access where possible and enforcing least-privilege principles across all admin accounts.
How to Identify the Correct Credentials for Your ec230 g1
Identifying the exact credentials for ec230 g1 starts with your device label and documentation. Steps include:
- Locate the product label on the device or packaging, noting the exact model and firmware revision.
- Check the official user manual or vendor support portal for login procedures tied to your firmware version.
- Compare any pre-configured accounts listed in the documentation, then verify login URLs or web interfaces.
- If you purchased an appliance, review the initial setup guide and any secure provisioning steps provided by the vendor.
- Record the official credentials and immediately prepare to replace them with a unique password during first login. If you cannot locate the docs, contact vendor support and reference the ec230 g1 series notes.
Best Practices for Managing Default Passwords
A robust password management strategy helps keep ec230 g1 devices secure.
- Change passwords on first login: Do not reuse defaults. Create long, unique passwords with a mix of characters.
- Use a password manager to store credentials securely and reduce re-use.
- Enable multi-factor authentication (MFA) where available to add a second layer of defense.
- Implement account lifecycle processes: review user access quarterly, and revoke unused accounts promptly.
- Maintain an audit trail: log login attempts and monitor for unusual activity.
- Apply firmware updates and security patches promptly to minimize risk from known vulnerabilities.
- Limit admin access to trusted networks and use network segmentation to contain potential breaches.
These practices align with security best-practices and help ensure credentials stay protected over time.
Step-by-Step: Resetting the ec230 g1 Password
Follow these generalized steps to reset an ec230 g1 password safely:
- Access the admin interface via the device’s web portal or management console using existing credentials.
- Navigate to the Security or Administration section to locate password or account settings.
- Choose to change the password for the admin account; if you cannot access, use the vendor-provided recovery option.
- Create a strong, unique password with sufficient length and character variety.
- Save changes, log out, and perform a test login to confirm the new credentials work.
- Update any saved credentials in your password manager and document the change for audit purposes.
- Enable MFA if the option is available and configure access controls for elevated privileges.
Recovery Scenarios: Forgotten Passwords or Locked Admin Accounts
If you forget the ec230 g1 admin password, do not guess. Use the vendor-recommended recovery process, which may require physical access to the device, a documented reset procedure, or contacting support for assisted recovery. In some cases a factory reset may be necessary, which will erase custom configurations; always back up configuration data where possible before performing resets. After recovery, enforce password changes and review access permissions.
Security Auditing and Maintenance
Regular auditing helps ensure credentials remain secure over time. Establish a cadence for reviewing admin accounts, verifying password freshness, and monitoring login attempts. Maintain an asset inventory of ec230 g1 devices, track firmware versions, and ensure password policies align with organizational standards. Use centralized logging and security information and event management (SIEM) integration where feasible to detect anomalies early.
Common Pitfalls and How to Avoid Them
- Relying on only factory-default credentials without verification: Always validate against official docs.
- Delaying password changes: Set a forced-change policy on first login.
- Reusing passwords across devices: Use unique credentials for admin interfaces.
- Failing to enable MFA: If available, always enable MFA for admin access.
- Neglecting audits: Schedule quarterly reviews of admin accounts and credentials.
Getting Help and Documentation
If you’re unsure about the ec230 g1 default password specifics, start with the vendor’s official documentation or support portal. Look for product manuals, firmware release notes, and security guides. For enterprise deployments, engage your IT security team to align device credentials with organizational standards.
Credential handling considerations for ec230 g1
| Aspect | ec230 g1 Considerations | Recommended Action |
|---|---|---|
| Default Credential Location | Device label, admin portal, or firmware docs | Consult official user manual and vendor portal |
| Initial Login Process | Varies by firmware; may require device-specific URL | Follow vendor-specific setup guide |
| Password Requirements | Strong passwords recommended; length and complexity vary | Enforce length 12+ with mixed case and symbols |
| Reset Capability | Hardware button or software reset options may exist | Use documented reset procedure or contact support |
Your Questions Answered
What is the ec230 g1, and why does it have a default password?
The ec230 g1 is a device model that often ships with vendor-specific default credentials to enable initial setup. Defaults vary by firmware version and product line, so always verify against official documentation before attempting login.
The ec230 g1 is a device that may come with vendor-specific default credentials; always verify with the official manual before logging in.
Can I continue using the default password after setup?
No. Default credentials should be changed during initial setup to prevent unauthorized access. This reduces risk significantly.
Don't keep the default password after setup—change it right away.
How do I reset the ec230 g1 password if I can't login?
Use the vendor’s recovery procedure, which may require physical access or support contact. A factory reset may be necessary in some cases, but back up configurations first.
If you can't log in, use the vendor recovery steps or contact support.
Is MFA available for ec230 g1 admin access?
MFA availability depends on the model and firmware. Check the admin panel for MFA options and enable when possible.
Check for MFA options in the admin menu and enable them if available.
Where can I find official documentation for ec230 g1 credentials?
Visit the vendor’s support portal or the official product manual for credential guidance and reset procedures.
Look up the official vendor manual or support portal.
“Default passwords are a common attack vector; changing them and enforcing strict access controls dramatically reduces risk. Proactive credential hygiene is essential for all admin interfaces.”
Key Takeaways
- Verify credentials from official docs before login.
- Always change default credentials during initial setup.
- Use a password manager and enable access logs.
- Regularly audit and rotate admin credentials.