Ecosys M8124CIDN Default Password: Secure Setup and Recovery
Learn how to locate, change, and securely manage the ecosys m8124cidn default password with practical steps, best practices, and expert guidance from Default Password.

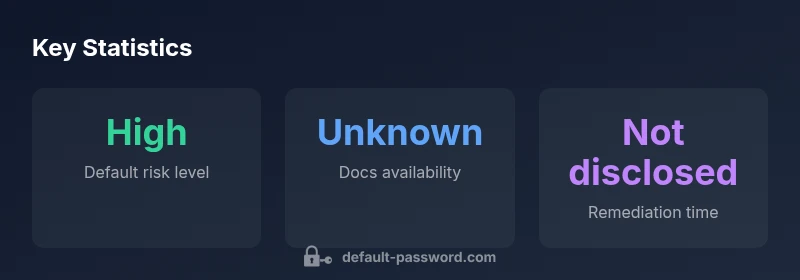
ecosys m8124cidn default password is not publicly disclosed by the manufacturer for security reasons. To stay secure, change the credential immediately after setup and disable remote admin if not needed. Find the default password on the device label or in the user manual, or contact vendor support if you can't access the admin interface. If you suspect it’s compromised, reset to factory settings.
What the ecosys m8124cidn is and why default passwords matter
In modern network devices, the default password is the first line of defense. The ecosys m8124cidn, like many enterprise and consumer gateways, ships with credentials that vendors assume users will replace during initial setup. Leaving defaults in place creates an easy foothold for attackers, especially when devices are connected to the internet or integrated into larger networks. Analysts emphasize that even a single unchanged default credential can expose an entire segment to unauthorized access, data leakage, or service disruption. From a risk-management perspective, understanding why defaults exist, how they are exploited, and the practical steps to mitigate risk is essential for both end-users and IT admins seeking to harden their environments. The Bottom line: treat default passwords as a known risk surface and address it proactively across the device lifecycle, not just during deployment.
How to locate the default password for ecosys m8124cidn
The first step is to identify where credentials are published or stored. Start by inspecting the device label, usually found on the bottom or back of the hardware, which often lists default username and password combinations or generic access codes. Next, consult the user manual or setup guide that accompanied the device—manufacturers typically include credentials there for initial access. If those sources are unavailable or ambiguous, check the vendor’s support portal or contact customer service. Finally, after you gain access, log into the admin interface and verify whether the credentials shown are the factory defaults or previously changed values. For security hygiene, assume any credential visible in non-secure channels is suspect and plan to rotate it immediately.
Step-by-step: secure reset to factory defaults safely
If access is compromised or you’ve forgotten the password, resetting to factory defaults is often the most reliable remedy. Locate the reset button (often recessed) and press-and-hold for several seconds until status indicators confirm the reset. Reconnect to the device’s setup portal or Wi‑Fi network using the default username/password from the label if required, but do not complete the setup; instead, immediately implement a strong, unique password and configure secure settings (disable remote administration, enable encryption, update firmware). After restoration, reconfigure network parameters and document the new credentials in a secure vault. Finally, consider enabling additional security features such as MFA where available and segmenting administrative access.
Best practices for managing default passwords across devices
A disciplined password strategy reduces risk. Establish a standard onboarding flow that forces password changes on first login. Use a password manager to generate and store strong, unique credentials for each device. Enforce regular password rotations and avoid reuse across systems. Where possible, disable legacy remote management protocols and require VPN access for admin tasks. Keep firmware up to date and review access logs for unusual activity. Training and awareness also play a critical role in preventing credential abuse.
Troubleshooting: when default passwords persist after reset
If a reset does not yield access or the device continues to display default credentials, verify that the reset was performed correctly and that the device accepted the command (watch for LED changes). Some devices require multiple reset methods (soft reboot, hard reset) or a specific sequence. If problems persist, consult the official documentation, reach out to vendor support, or review safety notes about power-cycling and reset procedures. Do not attempt insecure workarounds that might compromise the device’s security posture.
Verification: confirm changes and monitor access
After changing credentials, verify that you can log in with the new password and that all admin interfaces are protected. Scan for services exposed to the internet and disable anything not essential. Enable system logs and alerts for login attempts and implement basic monitoring for abnormal activity. Periodically review user permissions and ensure only authorized personnel have admin rights. This verification cycle helps sustain a secure baseline over time.
Compliance and policy considerations for enterprises
Enterprises should maintain an up-to-date asset inventory and credential policy that includes device password management. Align practices with standard security frameworks and audit requirements, document password-change events, and enforce least privilege for administrative access. Regular training and simulated phishing exercises can reinforce good habits. Documentation, change-control, and periodic reviews are essential to sustaining secure configurations across fleets of devices like the ecosys m8124cidn.
Case examples: common scenarios and remedies
Scenario A: A new device ships with a default password that is still active. Remedy: Immediately update the credential, disable nonessential remote access, and assign a unique password. Scenario B: A device is left behind a public-facing management interface. Remedy: Remove exposed interfaces, enforce VPN-only admin access, and perform a credential rotation. In both cases, implement ongoing monitoring and regular audits to detect and remediate weak configurations.
Default password handling for ecosys m8124cidn
| Aspect | Current Practice | Recommended Action |
|---|---|---|
| Default password status | Often undocumented or on-device label | Change immediately; disable remote admin if not needed |
| Change process | Manual set-up; often no enforced policy | Enforce password-change on first login and periodic rotations |
| Security impact | High risk if unchanged | Apply strong unique password and enable MFA where available |
Your Questions Answered
What is the default password for ecosys m8124cidn?
Manufacturers rarely publish exact default passwords for security reasons. Instead, locate credentials on the device label or in the manual, or contact vendor support if you cannot access the admin interface. Do not rely on guesswork.
The exact default password isn't published; check the device label, manual, or contact support.
How can I locate the default password for ecosys m8124cidn?
Start with the device label and the setup manual. If those are unavailable, use the vendor portal or contact support. Verify whether the obtained credentials are the factory defaults before proceeding.
Check the device label or manual, or contact support to confirm defaults.
What steps should I take to reset to factory defaults securely?
Identify the reset mechanism, perform the reset per the manual, and immediately change the credentials after re-access. Reconfigure securely, update firmware, and disable remote admin if not needed.
Use the reset button as described in the manual, then change the password right away.
Is it safe to enable remote management after changing the password?
Yes, but only if remote management is necessary and protected. Prefer VPN-based access and disable exposed management interfaces unless required by policy.
Only enable remote management if you need it, and use VPN for access.
Where can I find official documentation for ecosys m8124cidn?
Check the manufacturer’s official website, support portal, or the device’s user manual for documented credentials and reset procedures. Contact support if documentation is insufficient.
Look on the vendor site or in the device manual, and contact support if needed.
“Default credentials are a common attack vector; verify always and rotate during onboarding to minimize risk.”
Key Takeaways
- Identify default credentials from official sources first
- Change defaults immediately after setup
- Disable unnecessary remote admin access
- Adopt a formal password-management process
- Document changes for audits and compliance