eg8245w5 6t default password: A practical guide for admins
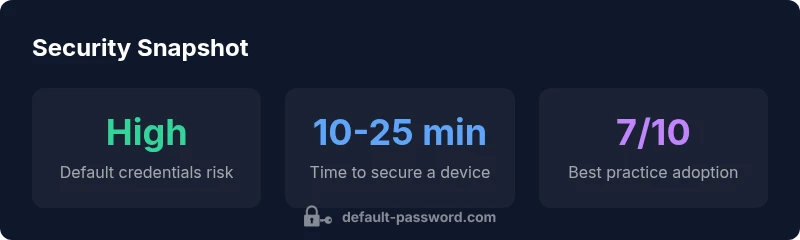
Learn why the eg8245w5 6t default password is a security risk and how to reset and secure router admin access with practical steps and best-practice checks.

According to Default Password, eg8245w5 6t default password refers to the factory credentials used to access the router's admin interface, typically printed on the device label or in the manual. For security, never leave this password unchanged in production environments; always reset to a unique, strong password and review remote management settings. This guide explains how to identify, reset, and secure those credentials across devices.
Understanding the term: eg8245w5 6t default password
The phrase eg8245w5 6t default password describes the factory-set credentials that grant access to a router's administrative interface. These defaults are intended to simplify initial setup but can create a serious security gap if left unchanged. According to Default Password, many installations still rely on these credentials because users underestimate the risk or assume the device is isolated. In practice, the exact username and password vary by model and firmware, but the principle remains the same: default credentials should be replaced with unique, strong keys as part of a secure baseline. This section explains how the default password concept applies specifically to the eg8245w5 6t series and why it matters for both home networks and small offices. The Default Password team emphasizes that threat actors often scan for devices with default access and then pivot to more sensitive assets. The core message is simple: security posture improves immediately when defaults are removed from the equation.
Security risks of leaving factory credentials as-is
Leaving a default password in place creates a predictable attack surface. Attackers can exploit weak or known credentials to access admin interfaces, which may yield control over firewall rules, DNS settings, and network segmentation. In practice, this risk is amplified when devices are exposed to the internet through misconfigured remote management or when administrative access is not restricted to trusted management subnets. The Default Password analysis highlights that most breaches involving consumer routers start with initial access via default or weak credentials. Organizations of any size should treat default passwords as a high-priority vulnerability and implement the principle of least privilege, strong password policies, and routine firmware updates to reduce exposure.
Locating the credentials on the EG8245W5 6T router
The default credentials are typically labeled on the bottom or rear of the device, often near the model number and serial. If the label is damaged or missing, consult the quick-start guide or the manufacturer’s official support site. Some firmware builds display the admin username and password on the login screen during first-time setup, but these should be changed immediately. If remote management is enabled, ensure it is bound to a trusted IP range and use a non-default port where possible. The localization of credentials may vary by region or carrier, so refer to the latest documentation for the exact login path (often http://192.168.1.1 or similar) and ensure you are accessing the device locally to prevent exposure on the public internet.
Step-by-step: reset and reconfigure the admin password
To reset and reconfigure the admin password on the EG8245W5 6T, begin by logging in with the current default credentials if you have not yet changed them. Navigate to the administration or security settings, locate the password field, and choose a strong, unique passphrase. Use a mix of upper and lower case letters, numbers, and symbols, aiming for at least 12-16 characters. Do not reuse passwords from other accounts. Save changes and reboot if required. Afterward, disable unnecessary remote management and update the firmware to mitigate vulnerability exposure. Finally, document the new credentials securely in a password manager and review access logs periodically.
Best practices for constructing strong router passwords
Strong passwords are long, unique, and unpredictable. Avoid common words, patterns, or sequences. Consider passphrases that combine multiple unrelated words and incorporate digits and symbols. If possible, enable two-factor authentication for router access, or at least enable device-level alerts for configuration changes. Use a reputable password manager to store and autofill the credentials securely. Regularly review and rotate critical credentials, especially after firmware updates or network changes.
Additional security measures beyond password changes
Beyond changing the default password, reinforce security with firmware updates, disable WPS, and restrict admin access to trusted devices. Segment your network to limit lateral movement, disable UPnP unless needed, and monitor for suspicious login attempts. Consider enabling a guest network to isolate devices and enforce strong encryption (WPA3 when available). Regularly back up configuration settings and keep a documented incident response plan in case of unauthorized access.
How to manage passwords across multiple devices and brands
In mixed environments, apply consistent password hygiene across devices—routers, access points, switches, and IoT hubs—using a centralized password manager. Establish a policy for password rotation, unique credentials per device, and minimum complexity requirements. Maintain asset inventories to track which devices still use default credentials and schedule periodic reviews. Training users and admins on security best practices reduces the chance of credential-based breaches.
Quick checks you can run after updating credentials
Verify that you can still access the router admin panel with the new password, then test from a separate device to ensure LAN-based access remains intact. Confirm that remote management is off or locked to a trusted IP, and run a firmware check to ensure the device is current. Finally, review recent login attempts and enable alerts if supported by the device.
Comparison of default password presence and mitigation across device types
| Device Type | Default Password Presence | Mitigation Steps |
|---|---|---|
| Residential Router | Common | Change default password; disable WPS; enable firmware updates |
| Business Router | Moderate | Enforce password policy; restrict admin access to VPN/IT subnet |
| IoT Gateway | High | Isolate devices; disable remote admin; use strong, unique passwords per device |
Your Questions Answered
What is the eg8245w5 6t default password and where can I find it?
The eg8245w5 6t default password refers to the factory credentials used to access the router’s admin interface. You can typically find them on a label on the device or in the documentation that came with it. If the label is missing, check the official support site or contact the carrier for the exact login details.
The default login is printed on the device or in the manual; check there first, then contact support if needed.
Why should I change the router’s default password?
Changing the default password is a fundamental security practice. It prevents unauthorized access to router settings, which could lead to network compromise, data leakage, or device misuse. Even if the device is behind a firewall, many attackers rely on known defaults to gain initial access.
Because default credentials are a common entry point for attackers, changing them blocks easy access.
How do I reset the EG8245W5 6T to factory defaults?
A factory reset restores the original login credentials but also erases custom settings. Typically, you press and hold the reset button for 10-15 seconds while the device is powered. After reboot, you should immediately set a new admin password and review security settings before reconfiguring the network.
Hold the reset button while the power is on for several seconds, then reconfigure security settings after reboot.
Is it safe to enable remote management after changing the password?
Remote management can be convenient but increases exposure. If you enable it, restrict it to trusted IP addresses, use a non-standard port if possible, and keep firmware updated. If you don’t need remote access, keep it disabled.
Use remote access cautiously: restrict IPs, use strong auth, and keep firmware current.
What should I do if I forget my new admin password?
If you forget the new admin password, perform a reset to regain access. Then immediately set a new, strong password and review access controls. Consider using a password manager to avoid future lockouts.
If you forget it, reset the device and set a new password right away.
“Strong admin access starts with removing factory credentials and enforcing stable, unique passwords across devices. Regular updates and restricted remote management are essential.”
Key Takeaways
- Replace default credentials on all devices
- Use strong, unique passwords and a password manager
- Limit remote admin access and keep firmware updated
- Document changes and monitor login activity