How to Reset and Secure the SIP T42G Default Password on Enterprise IP Phones
Learn how to securely reset the T42G default password on enterprise IP phones, prevent lockouts, and establish ongoing password governance with practical steps from Default Password.

Goal: securely reset the SIP T42G default password on an enterprise IP phone and restore safe admin access. You’ll need physical device access or verified admin credentials, plus network connectivity to reach the device’s web interface or provisioning portal. This quick answer previews the exact, step-by-step process and safeguards to prevent lockouts.
Why enterprise ip phone sip t42g default password matters
Every networked device in an enterprise adds a line of defense or a potential entry point for attackers. The SIP protocol used by modern IP phones relies on credentials to protect configuration and call features. The enterprise ip phone sip t42g default password is a well-known risk vector: if left unchanged, an attacker on the same LAN can access admin settings, alter call routing, or export sensitive data. According to Default Password, many organizations underestimate the danger until it’s too late. The consequences include device compromise, rogue provisioning, and exposure of internal DHCP and VOIP configuration. In practice, changing the default password is not just a routine admin task; it is the first line of defense in a broader security baseline for voice networks. This guide focuses on T42G devices but the principles apply to most SIP-based phones. A robust password policy, combined with inventorying devices and enforcing resets on firmware updates, reduces risk and improves compliance with governance standards. This is especially important in regulated industries where voice data is sensitive and regulatory audits require detailed change records.
Understanding SIP authentication and T42G basics
SIP-based phones authenticate to PBX systems or provisioning servers using credentials stored on the device. The T42G supports standard SIP authentication, provisioning via DHCP or manual config, and secure management interfaces. The default password is often a simple placeholder that grants access to admin menus or backup configurations. Understanding the authentication flow helps you plan a secure password strategy, including the use of unique, strong passwords, regular rotation, and device inventory tracking. Always ensure the device’s firmware is up to date, as vendors patch vulnerabilities related to authentication routines. A strong password policy, combined with role-based access and MFA on management interfaces where supported, dramatically lowers risk.
Compliance and governance considerations
Organizations must demonstrate accountability for device credential changes. Compliance frameworks commonly require trackable change management, documented approvals, and periodic audits of critical devices like IP phones. Keeping a centralized inventory of all SIP devices, their admin passwords, and last rotation dates supports both internal controls and external audits. When possible, implement centralized provisioning with unique per-device credentials rather than shared defaults. This approach reduces blast risk if one device is compromised and simplifies incident response. According to industry guidance, aligning password resets with firmware update cycles enhances security posture and minimizes operational friction.
Pre-checks and prerequisites
Before changing a T42G password, verify you have verified admin rights and network reachability. Confirm you can access the device via its web UI or provisioning server, and ensure you have current backups of configurations. Document the existing password policy, determine whether a factory reset is permissible, and identify any device-specific constraints (such as required firmware levels or emergency fallback procedures). If the device is managed by a centralized system, coordinate changes with the admin team to avoid inadvertent overwrites during auto-provisioning. These pre-checks prevent unexpected outages and help you establish a repeatable process for future resets.
Step-by-step security stance before changing passwords
Adopt a security-first mindset: plan the change window, notify impacted users, and prepare rollback steps. Disable non-essential remote management during the password reset window to minimize exposure. Ensure you have access to a secure management workstation and use a trusted network segment. After the password is changed, validate all remote management paths are functioning only with the new credentials and enable tight access controls. Keeping a record of the new credentials in a secure vault reduces the chance of future lockouts and supports audits.
Factory reset vs. manual password change: pros and cons
A manual password change preserves device configurations and provisioning settings, reducing downtime. It is usually less disruptive for devices in large deployments. A factory reset restores defaults but erases all custom configuration, reset schedules, and provisioning links, requiring reconfiguration across the fleet. When possible, prefer a targeted password change for admin access, then re-issue provisioning credentials to maintain centralized control. If the device is already compromised or misbehaving, a factory reset may be the quickest path to regain control—followed by strict re-provisioning and password hygiene.
Network and provisioning considerations
IP phones rely on network reachability for provisioning and authentication. Ensure DNS resolution, correct VLAN assignment, and firewall rules that permit PBX and provisioning server access. If you use a centralized management system, confirm it has up-to-date device records and that provisioning templates align with your new credentials. After password changes, re-apply any security controls such as MAC-based access lists and IP allowlists to limit device exposure. Document any changes to DHCP options or TFTP/HTTP provisioning endpoints.
Post-change validation and auditing
Test admin access with the new password on a test device first, then verify successful login across the production fleet during a maintenance window. Check for provisioning updates, firmware integrity, and any abnormal call behavior. Review access logs and system alerts for authentication failures or repeated login attempts. Establish a short-term audit trail showing who changed what, when, and where the changes were propagated. This evidence supports governance requirements and incident response readiness.
Long-term password management and best practices
Adopt per-device credentials, rotate passwords on a defined cadence, and integrate password management into your overall security program. Centralize credential storage in a vault, enforce MFA where supported, and disable unused management interfaces. Regularly review access permissions and run vulnerability scans focused on SIP devices. These practices reduce the risk of credential leakage and help maintain secure voice communications across the organization.
Authority sources
- https://www.cisa.gov
- https://www.nist.gov/publications
- https://us-cert.cisa.gov
Tools & Materials
- PC or laptop with network access(Ensure you’re on the same VLAN or have VPN access if remote)
- Web browser (Chrome/Edge/Firefox)(Supports TLS; ensure certificates aren’t blocked)
- Admin credentials for the IP phone or provisioning system(Verified owner; avoid sharing in unsecured channels)
- Official device documentation or firmware version info(Helpful for device-specific steps)
- Password management tool or secure vault(Store the new password securely)
Steps
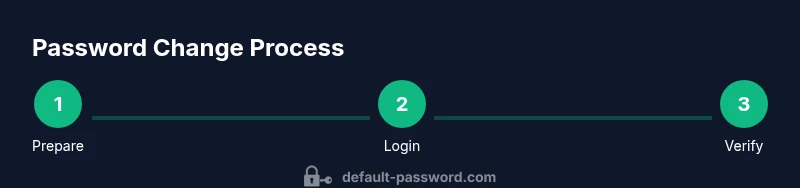
Estimated time: 20-40 minutes
- 1
Prepare access to the device
Identify the device’s IP address, confirm maintenance windows, and ensure you have a secure admin account. Verify you can reach the web UI or provisioning server from your workstation. This preparation minimizes downtime and helps you recover quickly if something goes wrong.
Tip: Have a backup login method in case the main admin password is inaccessible. - 2
Back up current configuration
Export or save the current phone configuration before making changes. Store the backup in a secure location so you can restore settings if needed. This protects against accidental loss of call routing or network settings.
Tip: Keep at least two copies in separate secure locations. - 3
Access the admin interface
Log in to the T42G admin portal using the current credentials. If the credentials are unknown, consult your centralized management system or vendor recovery options. This login is the gateway to credential changes.
Tip: Use a wired connection for stability during login. - 4
Navigate to password settings
Find the Security or Admin section where passwords are managed. Do not change unrelated fields. Confirm you are in the correct device context if multiple phones exist in the same network.
Tip: Double-check device selection to avoid mass changes. - 5
Change the admin password
Enter a strong, unique password following your organization’s policy (length, complexity, and uniqueness). Save changes and log out, then test the new password by re-login.
Tip: Do not reuse passwords from other devices or services. - 6
Re-provision if needed
If your device is managed by a central provisioning server, update credentials there and push to the device to avoid conflicts between local and provisioned settings.
Tip: Coordinate with the provisioning admin to prevent overwrites. - 7
Validate access and functions
Login with the new password and verify admin functions, network settings, and firmware status. Ensure call functions and provisioning links work correctly after the change.
Tip: Run a quick call test to confirm baseline functionality. - 8
Document the change
Record the new password securely, the device’s IP, firmware version, change timestamp, and the admin who performed the change. This supports audits and future resets.
Tip: Store access logs securely and share only with authorized personnel. - 9
Monitor and review
In the following days, monitor for unauthorized access attempts and verify ongoing compliance with password policies. Schedule the next review date to maintain security health.
Tip: Set up alerts for unexpected login attempts.
Your Questions Answered
Why is changing the default password on an IP phone critical?
Default credentials are an easy target for attackers. Changing the password reduces unauthorized access to admin interfaces and protects call routing and configuration data.
Changing the default password is critical to prevent attackers from taking control of the phone’s settings.
Can password changes be performed remotely?
Some phones and provisioning systems support remote password changes, but many require on-device or local admin access for security. Always verify remote change options with your deployment team.
Remote changes are possible in some setups, but you should confirm with your admin before proceeding.
What if I forget the new password after changing it?
Use the device’s recovery options or central provisioning system to reset credentials. If those fail, you may need a factory reset after confirming access risks and having backups.
If you forget it, use recovery options or provisioning to reset credentials, or contact the admin team.
Is factory reset the only safe option?
Not always. A manual password change preserves configurations, while a factory reset clears all settings. Choose only if the device is unresponsive or compromised, then re-provision carefully.
Factory reset is a last resort when manual changes can’t be completed.
What are best practices for ongoing password management?
Use unique per-device passwords, store them securely, rotate on a defined schedule, and disable unnecessary remote access. Regular audits help maintain security.
Keep unique passwords, rotate them on a schedule, and audit access regularly.
Watch Video
Key Takeaways
- Change default passwords promptly to reduce breach risk
- Keep a secure, centralized record of credentials
- Test changes in a controlled window and document outcomes
- Monitor post-change activity to catch misconfigurations early
- Coordinate with provisioning systems to avoid overwrites