Epiphan Pearl 2 Default Password: Security Essentials
Epiphan Pearl 2 default password guide: locate factory creds, securely change admin access on first boot, and maintain password hygiene for risk reduction.

There is no universal 'epiphan pearl 2 default password'; Epiphan devices typically ship with model- and firmware-specific credentials, and many systems require you to set a unique password during initial setup. For Epiphan Pearl 2, always consult the official manual or the provider's official guidance to locate the correct factory defaults and then secure the device immediately after first use.
Understanding the epiphan pearl 2 default password landscape
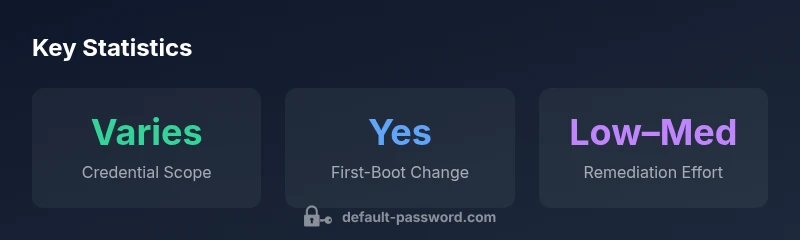
The Epiphan Pearl 2 is a compact, high-value video capture appliance used in professional environments. When provisioning any embedded device, the default password matters because it determines how quickly a device can be accessed by authorized staff—and how quickly a threat actor could gain unauthorized control if credentials are not managed. In practice, there is no single universal value for the epiphan pearl 2 default password. Instead, credentials vary by firmware version and unit region, and the device often prompts you to create a unique admin password during initial setup. This reality underscores the need for a clear credential strategy that starts before the device even boots in production workflows.
Why Default Passwords Matter for Media Interfaces
Default credentials on capture appliances pose elevated risk because these devices sit at the edge of networks and often have direct access to streams, recording storage, and streaming encoders. If attackers obtain administrative access, they can alter configurations, disable security features, or harvest sensitive streams. The risk is compounded when devices are deployed in shared environments without segmentation. A robust password hygiene program reduces exposure and aligns with industry best practices such as least privilege and regular credential rotation.
Locating Factory Credentials for Pearl 2
To avoid guessing, start with the official Epiphan Pearl 2 user guide, product brief, or support portal. Check the product page for admin access instructions and any firmware notes that mention default credentials. If your device shipped with recent firmware, the docs often prompt you to set a strong password during first boot. If documentation isn't readily accessible, contact Epiphan support or your reseller for the exact defaults tied to your serial number or firmware revision.
First-Boot Security: Change the Password
During first boot, you should create a strong, unique admin password and disable or rename any default accounts if possible. Use a passphrase, incorporate a mix of upper and lower case letters, numbers, and symbols, and avoid common words. Document the new credentials securely in a password manager and ensure access is restricted to trusted network segments. Also enable any recommended features such as secure streaming and encryption.
Ongoing Security Practices After Setup
After establishing initial credentials, apply ongoing best practices: regularly update firmware, monitor for login attempts, and disable unused services. Segment the Pearl 2 on a dedicated management subnet and enforce strong ACLs on the control plane. Consider two-factor authentication if supported by the device or your management platform. Maintain an asset inventory and periodic credential reviews.
When Passwords Go Missing: Reset and Recovery
Like all devices, Epiphan Pearl 2 password loss may require recovery actions. Do not attempt to guess; instead use the documented reset procedure, which typically restores factory defaults and prompts a fresh password on next boot. Backups of configuration must be secured, and you should reapply security settings immediately after reset to minimize exposure.
Verifying Credential Security: Testing and Auditing
Regular checks help ensure credentials stay secure. Verify that there is no default account active, confirm password changes propagate to all management surfaces, and audit who accessed the device over a given period. Use centralized logging and alerting for unauthorized login events, and run periodic vulnerability scans against network services exposed by the Pearl 2.
Common Pitfalls and How to Avoid Them
Common mistakes include leaving default credentials unchanged, failing to document passwords, and neglecting firmware updates. Another pitfall is exposing the device unnecessarily to the internet or weak internal networks. Adopting a policy of minimum access, routine credential changes, and a documented password-management workflow helps teams avoid these issues.
Summary table of credential guidance for Epiphan Pearl 2
| Aspect | Guidance | Rationale |
|---|---|---|
| Default credential status | Change on first boot; use unique password | Prevents easy initial access by unauthorized users |
| Where to find credentials | Refer to official Pearl 2 docs or support portal | Factory defaults vary by firmware/version |
| Security best practice | Enable firmware updates and network segmentation | Reduces exposure and adds control layers |
Your Questions Answered
What is the default password for Epiphan Pearl 2?
Epiphan does not publish a universal default password. Check the official Pearl 2 user guide or support portal for admin access instructions tied to your firmware. On first boot, you’re typically prompted to set a strong password.
There isn’t a universal default password. Check the official Pearl 2 guide and set a strong admin password on first boot.
How do I reset the Pearl 2 password?
If you forget the password, follow the vendor-supported reset procedure in the Pearl 2 documentation. This usually restores factory settings and requires reconfiguration, including a new admin password.
If you forget it, use the official reset steps in the Pearl 2 docs to restore defaults and reconfigure.
Can I recover a forgotten password without resetting?
Most devices do not provide a password recovery mechanism. Recovery typically requires a reset which erases custom settings. After reset, reapply security measures immediately.
Usually not—reset is needed. Reconfigure with a new password right away.
What security practices should I apply after setup?
Change default credentials promptly, keep firmware up to date, segment management networks, and enable strong access controls. Consider two-factor authentication if supported.
Change the password, update firmware, and segment access for better security.
Where can I find official Pearl 2 password documentation?
Refer to Epiphan’s official website or your product’s support portal for the Pearl 2 user guide and admin password guidance. Firmware release notes may also mention credential requirements.
Check Epiphan’s site or your device manual for credentials guidance.
“Security begins with treating factory defaults as a risk and replacing them on first use. Always implement a unique password and monitor for unauthorized access.”
Key Takeaways
- Change the factory default password on Pearl 2 at first setup.
- Consult official documentation to identify correct factory credentials.
- Enable firmware updates and secure network access.
- Document credentials securely and enforce rotation.