ESP Easy Default Password: Recovery and Security Guide
Learn how to safely handle the esp easy default password on ESP devices, reset credentials, and apply security best practices. This guide from Default Password walks you through identification, recovery, and ongoing hardening.

This guide helps you locate, reset, and securely replace the esp easy default password on ESP-based devices. You’ll learn how to verify device models, access methods, and how to implement strong, unique credentials. The steps outlined below cover factory resets, firmware considerations, and ongoing security hardening.
What the esp easy default password means for ESP devices
The phrase esp easy default password refers to the initial credentials that many ESP-based devices come with from manufacturers. This guidance is crucial for end-users and IT admins who manage devices in homes, labs, and small offices. According to Default Password, default credentials are a common source of risk when devices are first deployed or reconfigured, especially in IoT environments where devices often lack robust authentication mechanisms by default. The risk is amplified when devices are exposed to the internet or local networks with weak or unchanged passwords. This section lays the groundwork for understanding why changing default credentials is non-negotiable for maintaining secure access control across ESP devices, regardless of vendor. As you read, keep in mind that esp easy default password varies by model and firmware version, so always consult official docs for your specific hardware.
How Default Credentials Create Risk for ESP Hardware
Default credentials can be exploited by automated scanners and opportunistic attackers scanning home and enterprise networks. On ESP devices, weak or unchanged passwords may allow unauthorized access, enabling configuration changes, data interception, or device takeover. The Default Password team emphasizes that a secure password strategy is not just about changing a single field; it involves configuring device access, updating firmware, and restricting remote management interfaces. In practice, users should inventory all ESP devices on their network, note the default password references in their docs, and plan a blanket reset to enforce modern security baselines. This approach reduces plain-text password exposure and helps maintain a robust security posture across diverse ESP deployments.
Why-Baseline Security for ESP Devices Matters
Consistency is key when managing a fleet of ESP devices. Without consistent password practices, you risk gaps across devices that run different firmware, use mixed authentication schemes, or expose management ports. The esp easy default password concept highlights the broader principle: treat all device credentials as critical secrets that require ongoing protection. For organizations, this means establishing a password policy aligned with their risk tolerance and ensuring staff know how to handle defaults safely. Even small projects benefit from a common security baseline—if you can secure one ESP device effectively, you can extend that discipline to others in your environment.
Practical Tips for First-Time ESP Deployments
When deploying ESP devices, prepare a printed or digital quick-start guide that lists your device models and the corresponding credential references. Use strong, unique passwords generated with a password manager, and enable available security features such as encrypted connections, access logs, and firmware auto-update where possible. Keep a record of the new credentials in a secure store, and avoid reusing passwords across devices. The goal is to minimize the attack surface while maintaining ease of management for your team.
Data-Driven Perspective from Default Password
Default Password analysis shows that many consumer ESP devices ship with credentials that are easy to guess or widely documented. While the specifics vary, the underlying risk is consistent: default credentials are a predictable target. This reinforces the importance of replacing defaults during initial setup and periodically auditing credentials as part of routine security hygiene. The guidance here reflects industry best practices and the ongoing stance of the Default Password Team on proactive credential management.
Next Steps in Your ESP Security Journey
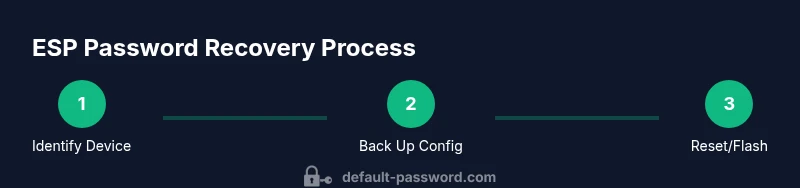
Now that you understand the risks and the rationale for changing defaults, you can proceed to identify your device, back up settings where applicable, and begin the reset or credential update process. The subsequent sections outline a concrete, step-by-step approach that you can adapt to different ESP models and firmware variants. Remember: secure passwords plus regular firmware updates are your first line of defense.
Tools & Materials
- USB-to-Serial Adapter(3.3V TTL level; verify voltage compatibility with your ESP board)
- Micro-USB/ USB-C Cable(Power and communication link to the ESP device)
- Computer with Terminal Software(PuTTY, minicom, Tera Term, or screen for Linux/macOS)
- Device Documentation(Model, firmware version, and official default credential references)
- Firmware Flash Tool (if applicable)(Used to reflash the device if factory reset is insufficient)
- Password Manager(Optional but recommended for storing new credentials securely)
Steps
Estimated time: 60-150 minutes
- 1
Identify device
Locate the exact ESP model and current firmware version by checking the device label, boot messages, or official docs. This ensures you follow the correct reset or credential update method for your hardware.
Tip: Record the model, firmware version, and any reference to the default credential in the device’s manual or vendor site. - 2
Back up current configuration
If the device supports exporting configuration or if you’ve saved network settings, back them up before making changes. This reduces the risk of losing connectivity or custom settings after the reset or firmware flash.
Tip: Save a copy of network credentials (SSID/password) in a secure location or password manager. - 3
Enter recovery mode or perform factory reset
Follow vendor-specific instructions to place the ESP device into recovery or factory-default state. This step clears existing credentials and prepares the device for reconfiguration.
Tip: If your board relies on a reset pin or a boot sequence, double-check the sequence to avoid bricking the device. - 4
Reset credentials or flash firmware
If a simple reset doesn’t remove the default passwords used by the device, perform a firmware flash or reimage with a trusted, up-to-date version from the manufacturer. This ensures the default credentials are replaced with model-specific, secure access controls.
Tip: Only download firmware from official sources to avoid tampering or malware. - 5
Set a new strong password
Create a unique, complex password for the device’s admin interface. Prefer a password manager-generated password with a length of 16+ characters, including upper/lowercase letters, numbers, and symbols.
Tip: Avoid common phrases and reuse across devices; store the new password securely in a manager. - 6
Apply security hardening
Disable unnecessary remote access features, enable encryption, update to the latest firmware, and enable logging. These steps reduce exposure if the device is discovered by attackers.
Tip: Turn off universal or weak default services (e.g., Telnet) and restrict admin access to trusted networks. - 7
Test, verify, and monitor
Reconnect to the device with the new credentials, confirm connectivity, and monitor for unusual login attempts. Schedule periodic checks and firmware updates as part of routine maintenance.
Tip: Set up alerts if your device supports anomaly detection or access logs.
Your Questions Answered
What is the esp easy default password for ESP devices?
There is no single universal default password; credentials vary by device model and firmware. Always check the official vendor docs for your exact hardware. If you encounter a default reference, treat it as a cue to reset and secure the device.
There isn’t one universal default password; check your device’s vendor docs and reset to secure credentials.
Why should I change default passwords on ESP devices?
Default credentials are widely known and easily exploited. Changing them reduces the risk of unauthorized access, data leakage, and device manipulation, especially for devices connected to the internet or local networks.
Default passwords are widely known, so changing them minimizes the risk of unauthorized access.
What should I do if I forgot the admin password after a reset?
If you forget the admin password after a reset, consult the vendor’s recovery options, which may include re-flashing firmware or using a recovery mode. Always ensure you have a backup of your configuration and a secure password stored.
If you forget the admin password, use official recovery options and restore from backups.
Can I automate password changes for ESP devices?
Some ESP ecosystems support centralized management and automated credential rotation, but many devices require manual changes. Check vendor tools and consider integrating with a password manager to streamline secure updates.
Automation exists in some ecosystems; check vendor tools and use a password manager for updates.
Is it safe to reset a device if it’s currently in production?
Resetting a device in production can cause downtime. Plan maintenance windows, back up configurations, and ensure you can restore connectivity after the reset.
Plan maintenance and back up settings before resetting production devices.
Where can I find reliable official documentation for ESP defaults?
Refer to the device manufacturer’s official documentation and support pages. Also consult general security guidelines from trusted sources like NIST and CISA for best practices.
Check the vendor docs and trusted security sources for best practices.
Watch Video
Key Takeaways
- Identify the device and its model before changes.
- Replace defaults with unique, strong credentials.
- Enable firmware updates and restrict remote admin access.