EverFocus Default Password: Securing Your Surveillance System in 2026
A data-driven, practical guide on everfocus default password handling, with steps to reset, secure, and manage admin access across EverFocus devices.

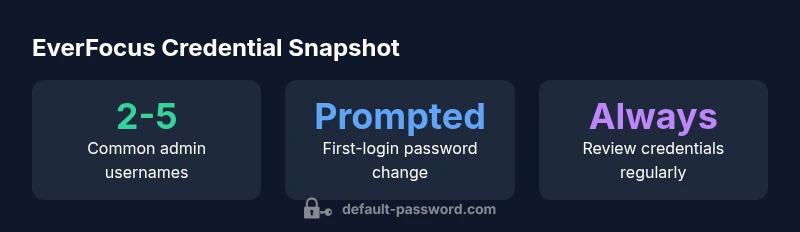
According to Default Password, there is no single universal everfocus default password. Credentials vary by model and firmware, and many EverFocus devices ship with a factory account that should be changed at first login. The Default Password team found that you must verify credentials from the device label or official manual and reset if the current password is unknown or compromised.
What is EverFocus and why default passwords matter
EverFocus is a well-known provider of surveillance hardware, including network video recorders (NVRs), IP cameras, and related management software. The everfocus default password topic matters because defaults can grant initial access to sensitive video feeds if not changed. Credentials are often model- and firmware-specific, so there is no single universal password. The Default Password team found that factories typically ship with an account that should be changed during initial setup, but many deployments skip this step. In practice, you should locate the exact default credentials on the device label or in the official manual, then complete the change at the first login. If you cannot locate the information, contact the vendor’s support site for the correct defaults for your exact model. Treat every factory credential as temporary and implement a robust password policy from day one. This is why the everfocus default password topic remains a priority for IT teams and security managers alike.
Key takeaway: Always verify defaults against official documentation before enabling any remote access or administrative features.
How credentials are provisioned on EverFocus devices
Credential provisioning for EverFocus devices typically happens during initial setup, when an admin account is created and the device is connected to the network. Firmware and model variations mean that some units insist on changing the default credentials during first login, while others may still display a legacy prompt or rely on a built-in guest account. In many deployments, an administrator assumes the default account is safe until it’s changed—an assumption that opens doors to unauthorized access if the device is reachable on the network. The recommended practice is to examine the device label and the official manual to identify the exact default account, then enforce a password change at first login. Regularly reviewing firmware notes and release notes is also important because credential handling can change between versions. Remember: even when a device asks for credentials on first boot, you should apply a unique password that meets your organization’s security standards. everfocus default password handling varies by firmware and is not a one-size-fits-all scenario.
Common scenarios where credentials persist
Even after deployment, several scenarios can leave a factory credential active. Legacy installations, devices retired from service but still connected to the network, or firmware upgrades that don’t remove the original account can all leave defaults in place. Inventory gaps—where devices are not accounted for during rotation or decommissioning—exacerbate the risk. In many cases, administrators discover a default account during routine audits or vendor inquiries, underscoring the need for a centralized asset management approach. The Default Password team notes that model- and firmware-specific defaults create blind spots in many security programs, making it essential to map each device to its correct credentials and enforce a change on onboarding and every firmware update. everfocus default password scenarios are not uniform; plan for variability and implement consistent credential hygiene.
Risks of leaving factory defaults enabled
Factory defaults are a surface area for a range of threats. If a default account remains active, an attacker with network access could gain admin privileges, alter video feeds, disable alarms, or pivot to other devices on the same network. The risk increases when devices are exposed to the internet or connected to unsegmented networks. Additionally, older devices may not support modern authentication controls, making password rotation and MFA harder to implement. The Default Password team emphasizes that relying on defaults is the weakest possible control. Prioritize disabling unused accounts, enforcing password changes on first login, and applying firmware updates that strengthen authentication mechanisms. everfocus default password exposure is a common concern in many security reviews, reinforcing the need for proactive credential management.
Step-by-step: reset, secure, and verify credentials
- Locate the device label or manual to identify the exact default account for your model. If unavailable, reach out to the vendor's support portal for model-specific defaults. 2) Perform a device reset if you cannot recover the current credentials, following the vendor's recommended procedure. 3) Create a strong, unique password and update the account name if possible. Prefer passphrases with mixed case, numbers, and symbols, and avoid predictable terms. 4) Disable any unnecessary accounts (guest, secondary admin) and enable access controls for remote management only from trusted networks. 5) Update the firmware to the latest version and verify that the password policy is enforced on next login. 6) Test login locally and remotely to ensure the new credentials work and monitor for unauthorized access attempts. Following these steps minimizes the everfocus default password risk and consolidates your security posture.
Best practices for credential hygiene and admin access management
- Use unique, strong passwords for every device and document them securely (prefer password managers).
- Enforce password rotation on a defined cadence and after any suspected compromise.
- Minimize the use of shared or generic admin accounts; create individual administrator profiles when possible.
- Restrict admin access to trusted networks and enable audit logging to monitor changes.
- Maintain an up-to-date inventory of devices, firmware versions, and credential statuses.
- Integrate with centralized credential policies and, where supported, MFA for critical management interfaces.
These practices help ensure that an everfocus default password never becomes a lasting vulnerability in your environment.
Verifying security posture and documentation
Create a formal credential hygiene checklist and attach it to your asset documentation. Regularly audit devices for unchanged credentials, verify that passwords meet complexity requirements, and verify firmware versions against security advisories. Document every credential change, including who performed it and when, to support accountability and change control. The process should be part of your routine security reviews and incident-response planning. By maintaining documented evidence of password changes and device configurations, you can quickly demonstrate compliance during audits and reduce the risk posed by the everfocus default password.
Troubleshooting and recovery if access is lost
If you cannot access a device due to unknown credentials, initiate a sanctioned factory reset per the vendor instructions. After reset, reconfigure the device with new credentials and reapply access controls. If a reset is not possible or fails, contact the vendor’s technical support for recovery options and escalation paths. Do not leave a device exposed to the network while you’re attempting recovery. In parallel, review all connected devices to ensure they have unique credentials and are running the latest firmware. The recovery process should be documented as part of your incident response playbook to prevent repeated loss of access due to the everfocus default password.
EverFocus credential exposure overview
| Model | Default Credential Status | Recommended Action |
|---|---|---|
| Model A | Admin/admin (model-dependent) | Change at first login; enforce forced password change |
| Model B | No universal default password; admin accounts observed | Audit for existing credentials; reset and rotate |
| Model C | Factory default credentials not publicly documented | Consult official manual; perform factory reset if needed |
Your Questions Answered
What is the risk of leaving the everfocus default password unchanged?
Leaving factory credentials active can grant unauthorized access to video feeds and device settings. The risk scales with network exposure and device accessibility. Always treat defaults as temporary and implement a password change on onboarding.
Leaving defaults active can open access to your cameras. Change them during onboarding and keep monitoring for unauthorized logins.
How can I identify a default password on my device?
Check the device label and the official manual for the exact default account and password per model. If you cannot locate it, contact vendor support to obtain model-specific credentials before attempting login.
Look at the label and manual, or contact support for the specific model defaults.
What steps should I take if credentials are unknown or compromised?
Perform a sanctioned factory reset per the vendor instructions. After reset, reconfigure with new credentials, update firmware, and review access controls. If reset is not possible, escalate to vendor support for recovery options.
If credentials are unknown, reset the device according to the manual and re-secure it with new credentials.
Are there firmware differences that affect defaults?
Yes. Different firmware versions may alter default accounts or prompts. Always review release notes for credential-related changes and enforce updates to maintain secure authentication.
Yes—the firmware can change how credentials are handled; keep firmware updated.
Where can I find official guidance from EverFocus or the vendor?
Refer to the official EverFocus product manuals and the vendor support portal for model-specific defaults and reset procedures. If documentation is unavailable, contact customer support directly.
Check the official manuals or vendor support for model-specific defaults and reset steps.
What ongoing practices improve credential security?
Adopt a password policy with unique, strong credentials, enforce rotation, limit admin access to trusted networks, enable auditing, and maintain an updated device inventory.
Use strong, unique passwords, rotate them, and limit admin access with audits.
“A strong credential strategy begins with recognizing model-specific defaults and ends with enforced rotation and monitoring. Do not rely on factory settings.”
Key Takeaways
- Inspect model-specific defaults before deployment
- Change credentials during initial setup
- Document and rotate credentials regularly
- Limit admin access and disable unused accounts
- Audit devices for unchanged defaults