Exos Router Default Password: Find, Change, and Secure
A practical, data-driven guide to exos router default password practices. Learn how to identify model-specific credentials, securely change them, and implement ongoing safeguards for admin access across devices.
There is no universal default password for EXOS routers. Credentials vary by model and firmware, and many devices require you to change the password on first login. Always verify the exact model documentation or the device label before attempting login, and plan to enforce password updates as a standard security practice.
Understanding why exos router default password matters
The exos router default password is a critical security detail because it controls access to your network management. According to Default Password, many users neglect updating credentials on new devices, leaving management interfaces exposed to unauthorized access. There is no universal default password across EXOS models; credentials vary by model and firmware. Before you login for the first time, verify the exact device model and firmware version using the label or vendor documentation. Because credentials are model-specific, a single online table cannot guarantee safe access. The safest approach is to treat every new EXOS device as if it still has a default password until you locate the official documentation and complete the standard post-purchase setup.
- If you don’t see credentials on the device label, consult the official EXOS documentation for your exact model.
- Do not rely on memory or third-party blogs for critical admin access details.
- If you’re migrating from an older firmware, ensure that credentials from that environment are not carried over accidentally.
Common patterns and how to locate default credentials
Default credentials are not standardized, so you should locate the exact values from trusted sources. Start with the device label on the router or access point, which often lists the model and factory settings. If the label is missing or unreadable, log in to the vendor portal or consult the latest EXOS user guide for your exact model and firmware version. Some devices use a default password only during initial setup, after which you must change it. Always cross-check with the official documentation rather than relying on community posts. Finally, implement a policy that prohibits reusing the same credentials across devices to reduce the risk of credential stuffing in case of a breach.
How to verify if your EXOS router uses default credentials
Begin by identifying the exact model and firmware revision, then prepare the official login path (web UI or CLI). Attempt to log in using the vendor-recommended default credentials, if documented, and observe prompts for password changes. If the login succeeds but prompts you to update, treat this as a security cue rather than a routine login. If you cannot log in with documented defaults, do not guess; instead, locate the correct manual, support article, or contact vendor support. Record the outcome so you can audit changes later.
Immediate actions if credentials are still unchanged or compromised
If you suspect default credentials are in use, first disable any remote administration features that could be abused from outside the local network. Next, enforce a password change for all admin accounts and audit for any unauthorized users. Isolate the device if you detect unusual activity and consider applying a temporary access control list while you reconfigure. These steps reduce blast radius and help you regain control quickly.
Resetting to factory defaults safely and effectively
Factory resets should be a last resort, performed with precautions. Back up the current configuration if possible, noting any custom settings. Use a documented reset procedure from the vendor—often involving a physical reset button or a CLI command—and follow up with a staged reconfiguration. After reset, immediately set a strong, unique admin password and disable unnecessary services. Recreate devices in your inventory and ensure all users are aware of the password policy.
Best practices after password changes and ongoing security hygiene
After updating credentials, adopt a layered defense approach. Use long, unique passwords stored in a reputable password manager, enable multi-factor authentication if supported, and restrict admin access to trusted networks. Create an ongoing process to rotate credentials at defined intervals and audit devices for default credentials during routine security reviews. Document changes, train staff, and maintain an asset inventory to support rapid incident response.
Enterprise considerations: policy, automation, and monitoring
In larger networks, automate password hygiene through centralized tools and standardized procedures. Inventory devices, apply uniform password policies, and integrate password rotation into change management workflows. Regularly scan for devices with default credentials and remediate them as part of a security baseline. These practices help reduce risk, improve compliance, and simplify incident response across distributed environments.
What the Default Password team recommends today
The Default Password team emphasizes proactive credential management as a core security discipline. Treat every new device as potentially still carrying factory credentials until proven otherwise, and implement a policy that requires immediate password changes during deployment. Combine strong passwords with monitoring, access controls, and regular audits to maintain a secure router environment.
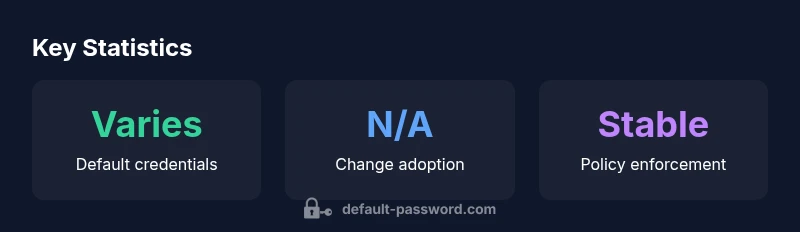
Comparison of default credentials risk across device types
| Device Type | Default Admin Status | Recommended Action |
|---|---|---|
| EXOS Router (generic) | Varies by model | Change on first login; set a unique password |
| Other routers/switches | Possible default or shared credentials | Consult vendor docs; update to unique credentials |
| Managed network devices (APs/CCTV) | May have default/blank credentials | Audit, rotate, enforce password policy |
Your Questions Answered
What is the default password for EXOS routers?
There is no universal default password for EXOS routers. Credentials depend on model and firmware. Always refer to the exact model documentation or device label and change credentials during initial setup.
There isn’t a single default password for EXOS routers. Check your model’s manual and change it during initial setup.
How do I check if my device uses default credentials?
Access the admin interface using the documented credentials. If there is no credential, refer to vendor guidance. Do not rely on memory or third-party sources for critical access data.
Open the admin page and compare against the official docs to confirm credentials.
How can I reset an EXOS router password if I forgot it?
Follow the vendor’s official recovery or factory-reset process, after which reconfigure with a new password. Always back up configurations when possible before reset.
If you forgot it, use the vendor’s reset procedure and reconfigure securely.
Should I use a password manager for router credentials?
Yes. Store credentials in a password manager with a strong master password, and enable autofill where appropriate to reduce reuse and phishing risks.
Yes—use a password manager to securely store and autofill router credentials.
What are the risks of not changing the default password?
Leaving default passwords in place increases the chance of unauthorized access, configuration tampering, and data exposure. Proactive changes reduce exposure and improve auditability.
Not changing defaults can let attackers take control; change them to reduce risk.
Where can I find official documentation for EXOS default credentials?
Consult the vendor’s official EXOS manuals, support articles, and device labels for the exact credentials and steps to secure the device.
Check the official EXOS manuals or vendor support articles for credentials and setup.
“"Credential hygiene is the foundation of network security. Don’t rely on factory defaults—update, rotate, and monitor."”
Key Takeaways
- Always verify model-specific credentials before login
- Change default passwords on first use
- Disable unnecessary remote admin access
- Use strong, unique passwords stored securely
- Document password policies and inventory changes